Ryan Preston retweetledi
Ryan Preston
562 posts
Ryan Preston
@awsmhacks
Keyboard Cagefighter, Console Cowboy, cache me sliding into your DC's #secKC
House of Zero Katılım Ekim 2015
631 Takip Edilen335 Takipçiler
@malcomvetter @SentinelOne Trust but verify Tim. 😉 I'm not sure when it was introduced but agent 23.2 came out in 2023
English

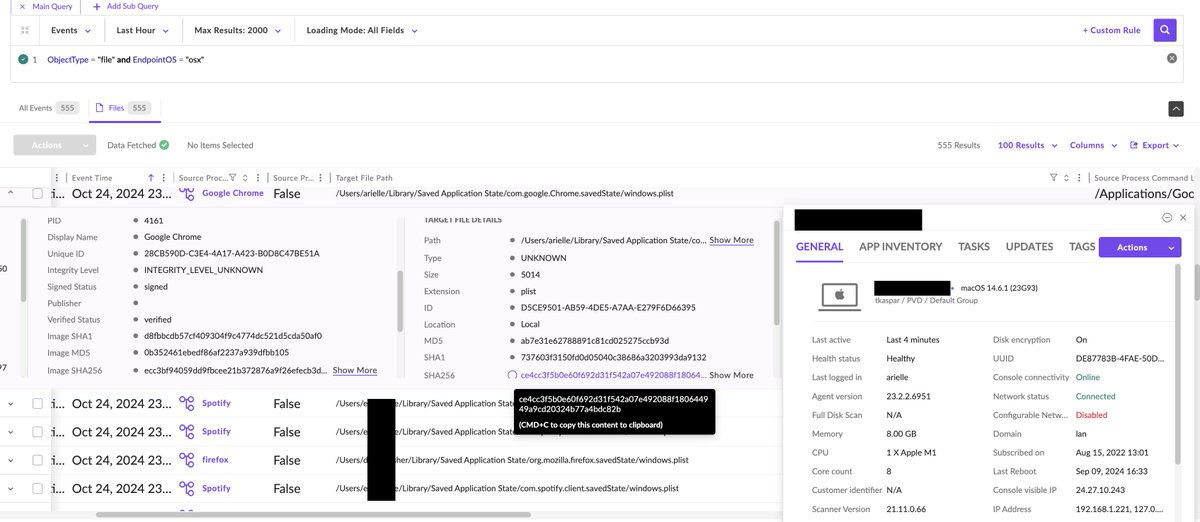
TIL: @SentinelOne doesn't have the ability to collect SHA-256 file hashes on Macs.
English

We have a new party page defconparties.com that allows you to build your own party agenda by selecting the events you are interested in attending. Our party list is also built into the @defcon hacker tracker. #defcon32 #BHUSA


English
Ryan Preston retweetledi

bro no one is burning a 0day at a hacker cosplay convention PLEASE
Jack Rhysider 🏴☠️@JackRhysider
My DEFCON hot take tips! 🔥 Bring a burner phone 📱Don't scan QR codes 🎧 🔊
English
Ryan Preston retweetledi

Today I am pleased to announce the release of a code analyser I’ve been working in my free time - wSAST (wsast.co.uk)
wSAST aims to make code analysis easier for application security consultants by providing tools to graph relationships, find paths between functions, and identify entry points into codebases as well as perform full dataflow and static analysis using a powerful rules engine.
Rules for analysis can propagate taints, express arbitrary relationships between variables, and attach arbitrary data to variables as they flow through the application during simulated execution. Rules can be written as simple XML format rules (for simpler types such as function rules, variable and type rules, and data rules), or in .NET for completely customised rules which can then be as convoluted as you like.
Multiple sources can be attached to any variable and multiple sinks to any trace, which then come and go from execution scope per a specified scope anchor.
Since wSAST is implemented over a custom intermediate language (WSIL) to which all supported languages are translated it will be able to support multiple languages. At the moment only Java core language support has been completed, and C support is about 95% complete but has no rules at this time.
My plan for the moment is to keep the core engine closed source but make all the rules, the front end, rules engine all open source and .NET based. I plan to make further steps towards this by releasing the code for these components to the wSAST GitHub when developer guides are finished. It will be possible for developers to add custom language support (if they’re brave enough!) using the interfaces provided, and the C to WSIL translator will be open source as an example.
I hope people find this useful! Don’t hesitate to contact me if you have any questions, on here or on @wsastsupport
English
Ryan Preston retweetledi

Made a tool which finds DLL files with RWX section in memory. I came up with this idea after I stumbled upon an interesting article by @SecurityJoes
github.com/pwnsauc3/RWXFi…
English
Ryan Preston retweetledi

New blog: Obtaining Domain Admin from Azure AD by abusing Cloud Kerberos Trust
I teased this a bit during my Windows Hello talks, now found some time to write about this interesting technique. Also contains defenses and detection opportunities.
dirkjanm.io/obtaining-doma…
English
Ryan Preston retweetledi
Ryan Preston retweetledi

My latest research which completely breaks trust transitivity, enjoy :-)
exploit.ph/external-trust…
English
Ryan Preston retweetledi

We are happy to announce we are hosting our first ever Malware Research Contest! Sponsored by our friends at @SentinelOne
* Must be novel research
* Applicants can only be from the United States due to anti-gambling and money laundering laws
* First place is a new Macbook Pro ♥️
GIF
English
Ryan Preston retweetledi
This is great!
its also cross-platform!
Download the CLI code binary for other os's/chipsets from code.visualstudio.com/Download# and they offer the tunnel feature too!
pfiatde@pfiatde
VSCode has a Tunnel Feature which can be used as a reverse shell. A very comfortable reverse shell. badoption.eu/docs/blog/2023…
English
Ryan Preston retweetledi
Ryan Preston retweetledi
This is a must-see for me at LABScon next week:
** The life and times of Sysinternals -- Mark Russinovich, Microsoft (@markrussinovich)
Agenda is legit 💪
#day-1" target="_blank" rel="nofollow noopener">labscon.io/#day-1
English
Ryan Preston retweetledi

We are releasing an alternative way for elevating to SYSTEM when you have SeTcbPrivilege
How?
Leveraging AcquireCredentialsHandle through an SSPI hook that allows authenticating as SYSTEM to SCM
Should be "lighter" than the classic S4U
cc @decoder_it
gist.github.com/antonioCoco/19…

English

An article of mine called "Attacking on Behalf on Defense" which talks about abusing EDRs/XDRs to dump lsass (and much beyond), plus a bonus collab with @dec0ne.
mansk1es.gitbook.io/edr-binary-abu…
English
Ryan Preston retweetledi
Ryan Preston retweetledi

@Zeusb0x Yep. You are partially correct but theres a lot more to it than EAT and IAT hooks. Finding syscalls are fine, but in order to do that you must first find the ntdll in memory which is the tricky part. I think if you evade S1, you by default evade almost every EDR there is.
English
Ryan Preston retweetledi
Ryan Preston retweetledi

SCCM network access accounts (NAAs) are back... And they're not going away. Not only can we query the credential blobs from WMI, we can also retrieve previously used account blobs from the CIM repository, even if the computer is no longer a client...
posts.specterops.io/the-phantom-cr…
English