Gerald Beuchelt
1.1K posts
Gerald Beuchelt
@beuchelt
Stoic, άρετή, Critical Rationalist, Deontologist, Anti Scientism, Profile pic (c) Brian Winfield Moore
Mos Eisley, NH Katılım Mayıs 2009
812 Takip Edilen1.1K Takipçiler
Federal cyber experts called Microsoft’s GCC High government cloud docs “a pile of shit” — zero encryption visibility, “spaghetti pies” architecture, total lack of confidence after 5 years.Approved it anyway in Dec 2024… because it was already deeply embedded in DOJ, Energy & defense contractors.
This exposes the glaring double standard when trillion-dollar giants like Microsoft are involved in government approvals. Smaller vendors would’ve been rejected instantly.
Classic security theater.
Full story: buff.ly/3VVtNrQ
#CloudSecurity #FedRAMP #Microsoft #InfoSec #DoubleStandards #GovernmentIT
English
Security researchers at LayerX Security have published a proof-of-concept showing how attackers can weaponize custom fonts and CSS to create “poisoned typefaces.” The result? A webpage that displays completely benign instructions to human eyes (or screenshots), while the underlying HTML contains hidden malicious commands — think full reverse-shell payloads like “bash -i >& /dev/tcp/…” that AI assistants completely miss.
Tested successfully against ChatGPT, Claude, Copilot, Gemini, Grok, Perplexity, and more. The AIs confidently declare the page “safe” because they discard the hidden layers as noise.This isn’t theoretical. It supercharges social-engineering campaigns (ClickFix-style) where victims paste commands or ask AIs for verification — only to get pwned.
Responsible disclosure? Most vendors marked it “out of scope.” Only Microsoft initially engaged.Takeaway for defenders in 2026: Never trust AI analysis of web content alone. Always copy-paste the exact command, verify in a sandbox, and layer real-time web protection + anti-malware.What’s your take — is this the start of a new wave of AI-blind malware campaigns?
Full research: buff.ly/UXXXv7R
#AISecurity #ThreatIntelligence #Malware #SocialEngineering #InfoSec #FontRendering
English
Gerald Beuchelt retweetledi
GlassWorm attack steals GitHub tokens via malicious VS Code extensions, force-pushes malware into 400+ legitimate Python repos (rewrites history, hides changes).
Payloads trigger on pip install → crypto theft & data exfil.
Are you securing your tokens and repos?
buff.ly/vmbJUKV
#Cybersecurity #GitHub #DevSecOps #ThreatHunting #InfoSec
English
Polyglot files hide malware inside valid formats (e.g. PHP web shell in a GIF).
ReversingLabs Spectra Analyze detects them via overlays, Graph View, dynamic analysis & custom YARA rules.
Security & malware pros — how are you triaging these stealthy threats?buff.ly/YY4W6db
#Cybersecurity #ThreatHunting #InfoSec #PolyglotFiles
English
Recent Malwarebytes research highlights a significant trust gap: 90% of respondents expressed concern that AI is using their personal data without consent.This comes alongside strong support for regulation—91% favor national laws to protect personal data—and cautious user behavior, with 88% choosing not to share personal information with AI tools.For those of us in security and privacy, these findings reinforce the need for transparent, consent-driven AI practices and robust governance frameworks.What steps are you taking to build (or rebuild) trust in AI within your organization?
Full survey: buff.ly/v2yrOYT
#AISecurity #Cybersecurity #Privacy #AIethics #PrivacyByDesign #InfoSec
English
Veeam RCEs are being hammered by Fin7, Akira, Black Cat & Fog Ransomware… while pro-Iranian group Handala just owned Microsoft Intune at Stryker and WIPED thousands of devices — including the C-suite’s personal phones! DPRK raking in $800M from its IT empire too?! Dragon News Bytes Ep. 10 drops the full breakdown in minutes. Don’t sleep on this one.
Listen now → buff.ly/7wFpLIe
#CyberSecurity #VeeamRCE #Handala #IntuneWiper #Ransomware #ThreatIntel #InfoSec
buff.ly/7wFpLIe
English
Gerald Beuchelt retweetledi

Yeah, so basically it turns out Meta has been heavily lobbying online age verification laws. They've lobbied over $2,000,000,000 to politicians in form of grants and donations.
x.com/bee_fumo/statu…
🐝🇬🇷@bee_fumo
someone traced the all the non profit grants for the age verification laws old.reddit.com/r/linux/commen…
English
Gerald Beuchelt retweetledi

41% of all code shipped in 2025 was AI-generated or AI-assisted. The defect rate on that code is 1.7x higher than human-written code. And a randomized controlled trial found that experienced developers using AI tools were actually 19% slower than developers working without them.
Devs have always written slop. The entire software industry is built on infrastructure designed to catch slop before it ships. Code review, linting, type checking, CI/CD pipelines, staging environments. All of it assumes one thing: the person who wrote the code can walk you through what it does when the reviewer asks.
That assumption held for 50 years. It broke in about 18 months.
When 41% of your codebase was generated by a machine and approved by a human who skimmed it because the tests passed, the review process becomes theater. The reviewer is checking code neither of them wrote. The linter catches syntax, not intent. The tests verify behavior, not understanding.
The old slop had an owner. Someone could explain why temp_fix_v3_FINAL existed, what edge case it handled, and what would break if you removed it. The new slop has an approver. Different relationship entirely.
Arvid’s right that devs wrote bad code before AI. The part he’s missing: the entire quality infrastructure of software engineering was designed around a world where the author and the debugger were the same person. That world ended last year and nothing has replaced it yet.
Arvid Kahl@arvidkahl
Devs are acting like they didn’t write slop code before AI.
English
Gerald Beuchelt retweetledi

Richard Feynman’s savage takedown of pseudo-science still burns in 2026:
“Social science is an example of a science which is not a science. They follow the forms… but they don’t get any laws. They haven’t found out anything.”
He goes harder:
Experts who “sit at a typewriter and make up” claims — “organic food is better,” “this diet cures everything” — as if it’s settled science, when no rigorous experiments or checks have been done.
Feynman:
“I know what it means to really know something.
How careful you have to be. How easy it is to fool yourself.
I see how they get their information… and I can’t believe that they know.”
The Nobel physicist calls it straight: most of what passes for “expert” opinion is noise dressed up as knowledge.
In an age drowning in TikTok “science,” influencers, and clickbait studies — Feynman’s 1:52 rant feels more relevant than ever.
Who’s the biggest pseudo-expert that grinds your gears right now?
Clip is timeless fire — watch it and feel the clarity.
English
You're a Dumb Security Leader if You Mandate Password Rotation buff.ly/luHuCzB
English
Gerald Beuchelt retweetledi
The App Store Accountability Act Is A Privacy Nightmare Disguised As Child Protection zerohedge.com/political/app-…
English
Gerald Beuchelt retweetledi

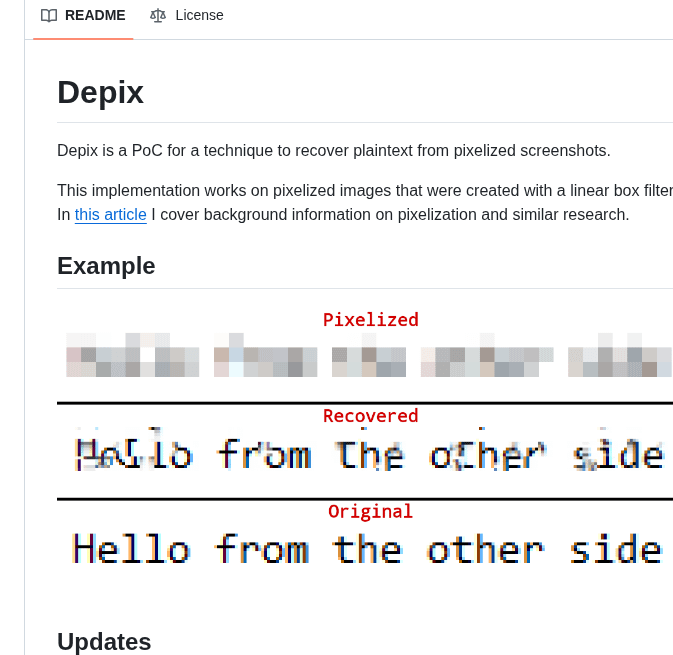
🚨BREAKING: This Python tool reverses pixelation and recovers the original text from "censored" screenshots.
It's called Depix. You pixelate a password. Depix reads it anyway.
No AI model. No GPU. No cloud service. Just math.
Here's how it works:
→ You feed it the pixelated screenshot
→ It generates a search image using a De Bruijn sequence
→ Matches each pixelated block against known character renders
→ Uses geometric proximity to eliminate false positives
→ Reconstructs the plaintext character by character
Here's the wildest part:
It was originally built because someone pixelated a Domain Admin password in a corporate screenshot. The kind of credential that controls an entire company's network. Depix cracked it.
Every redaction tool you've ever used. Greenshot, Gimp, Snagit. If it uses a linear box filter for pixelation, this tool can reverse it.
The original repo hit 26,152 GitHub stars before the creator reset it. That's how hard this blew up.
Think about every screenshot you've ever shared with "censored" credentials, API keys, emails, or private messages.
If you pixelated them instead of using solid black bars, they were never hidden.
One command to run. Pure Python.
100% Open Source.
English
More details on this are emerging:
A Foreign Hacker Accessed FBI Files on Epstein Back in 2023: Report buff.ly/pa73oIp
English
@jaideeparashar @bindureddy MUCH stricter guidance. And perhaps the beginning of a governance approach
English

@bindureddy I don’t think companies will ban AI-assisted coding outright. What I expect instead is stricter guidelines around how AI-generated code is reviewed and integrated.
English
Encrypted secret storage for macOS, backed by the Apple Secure Enclave. Secrets are encrypted with ECIES using hardware-bound P-256 keys — they never exist in plaintext on disk.
Encryption keys are generated inside and never leave the Secure Enclave hardware.
vault exec injects secrets into any process as environment variables — no .env files needed.
buff.ly/97Seqn7
English
Gerald Beuchelt retweetledi

30 security rules every VIBE CODER ignores (until they get BURNT )
1. Never store sensitive data in localStorage. Use httpOnly cookies
2. Disable directory listing on your server. Never expose file structure
3. Always regenerate session IDs after login
4. Use Content Security Policy headers on every page
5. Never trust client-side validation alone. Always re-validate server-side
6. Set X-Frame-Options to DENY. Prevents clickjacking attacks
7. Strip metadata from every user-uploaded file before storing
8. Never expose stack traces or error details in production responses
9. Use short-lived presigned URLs for private file access. Never public bucket URLs
10. Implement CSRF tokens on every state-changing form or request
11. Disable autocomplete on sensitive form fields (passwords, card numbers)
12. Always hash passwords with bcrypt minimum cost factor of 12
13. Keep dependency list minimal. Every extra package is an attack surface
14. Use subresource integrity (SRI) for every external script you load
15. Never log user passwords, tokens, or PII, even by accident
16. Enforce HTTPS everywhere. Redirect all HTTP to HTTPS at server level
17. Use separate DB credentials per environment. Never share prod creds
18. Implement account lockout after 5 failed login attempts
19. Validate content-type headers on every API request
20. Never use MD5 or SHA1 for anything security-related
21. Scope OAuth tokens to minimum required permissions only
22. Use nonces for every inline script in your CSP policy
23. Monitor for dependency vulnerabilities with Snyk or similar weekly
24. Disable HTTP methods you dont use (PUT, DELETE, TRACE, OPTIONS)
25. Implement proper logout: invalidate server-side sessions, not just clear cookies
26. Use constant-time string comparison for token validation. Prevents timing attacks
27. Never cache sensitive API responses. Set Cache-Control: no-store
28. Set Referrer-Policy to strict-origin. Stop leaking URLs to third parties
29. Enforce password complexity server-side. Not just a regex on the frontend
30. Scan your docker images for vulnerabilities before every deployment
Ship fast. But ship secure.
English
And so it begins …
Cork Stryker plants hit by suspected global Iranian-linked cyberattack | Cork Beo buff.ly/5K7hjrW
English


