BGP.Tools
217 posts
@bgptools
It's like a real-time global BGP looking glass that doesn't hate you! You can also pay us to tell you when stuff changes! Tweets by: @[email protected]
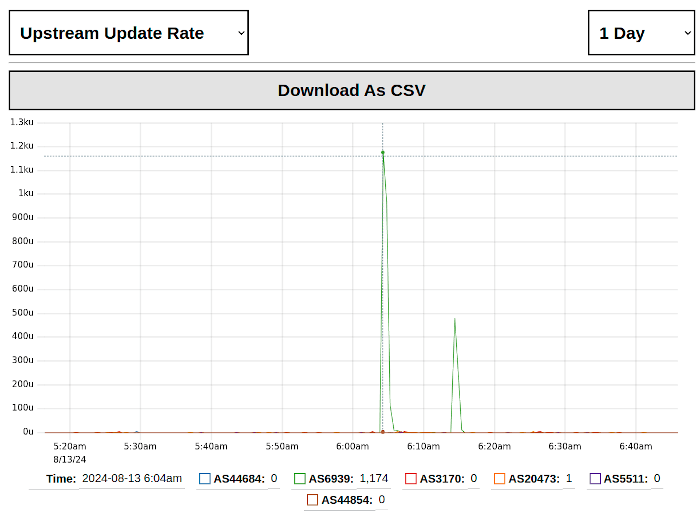


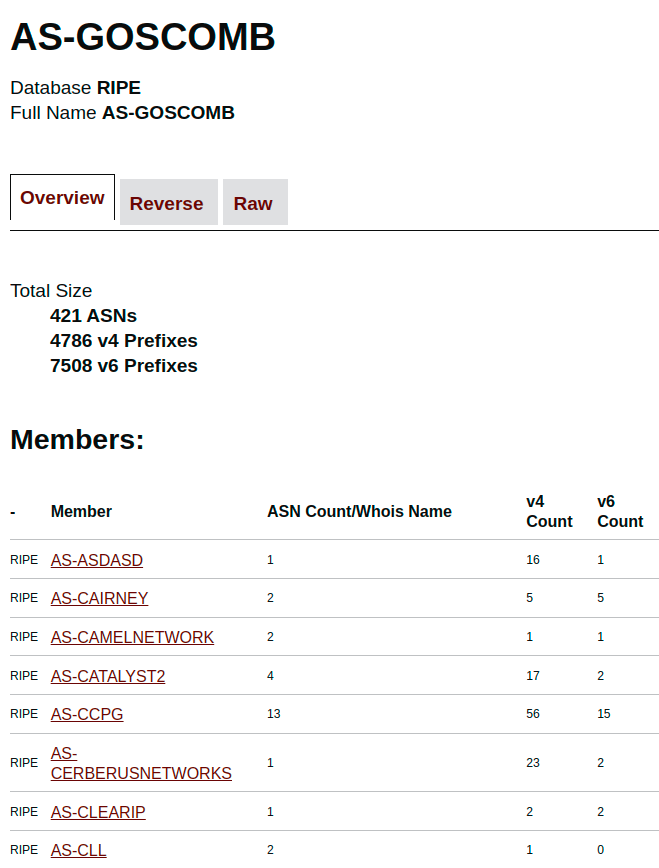
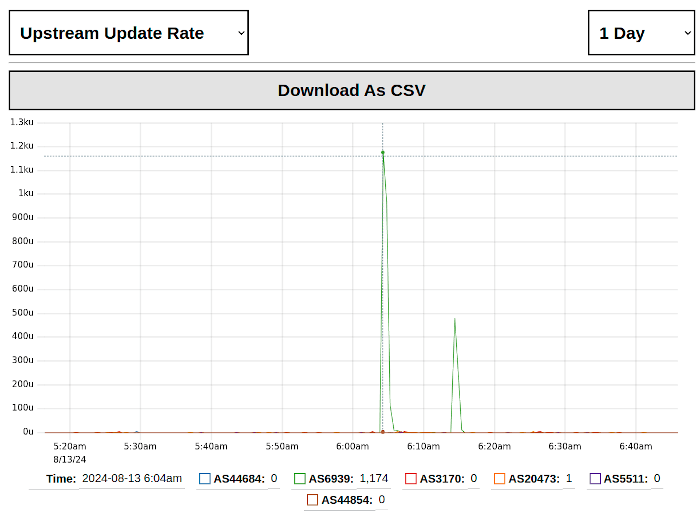
Looks like AS9498 (Bharti Airtel) typod a /32, /31 or /30. And turned it into a /3 (aka, 12.5% of the IPv4 internet) and other carriers (At least TI & GTT) accepted it!
@bgptools Thanks BGP Ben for the alert! It turns out that prefix-length checking does contain some hidden man-traps

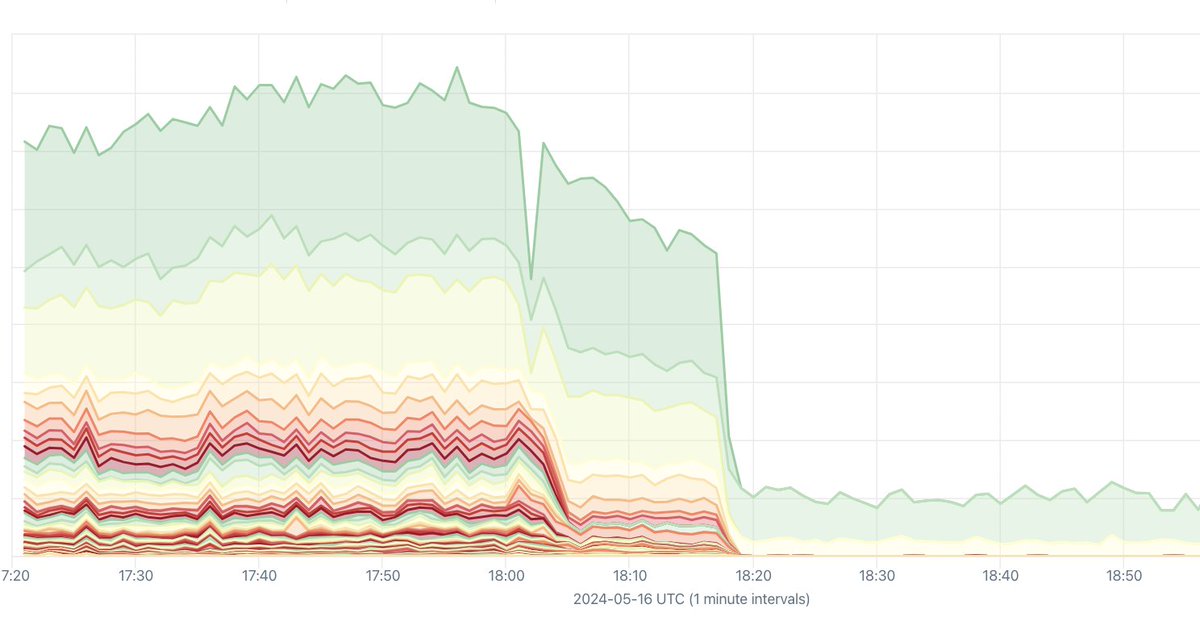
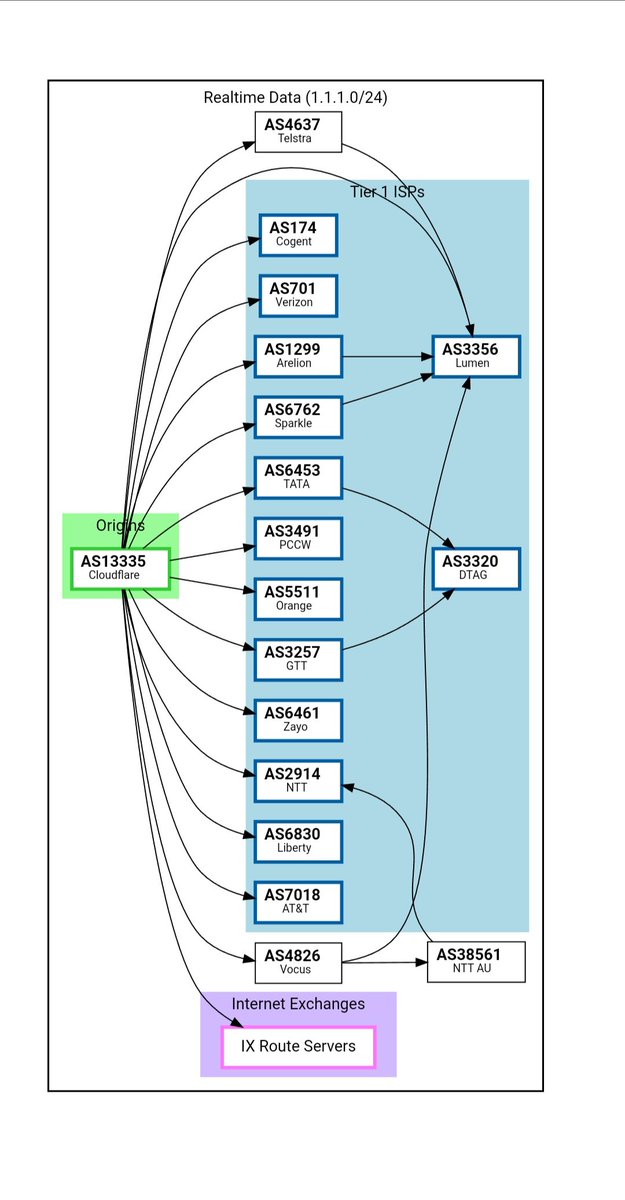
(The previous TATA-Cogent Full depeering post was wrong) It appears that TATA-Cogent have partially depeered in APAC. Cogent can't see APAC (notably India) routes anymore. It seems based on statements Cogent has initiated this depeering (Some EU/US routes seem to still be find)