Bhabesh
1K posts
Bhabesh
@bh4b3sh
Cybersecurity Analyst | Detection Engineer | Threat Hunter #Microsoft365 #EntraID #Azure #Windows #AD #AWS #Kubernetes





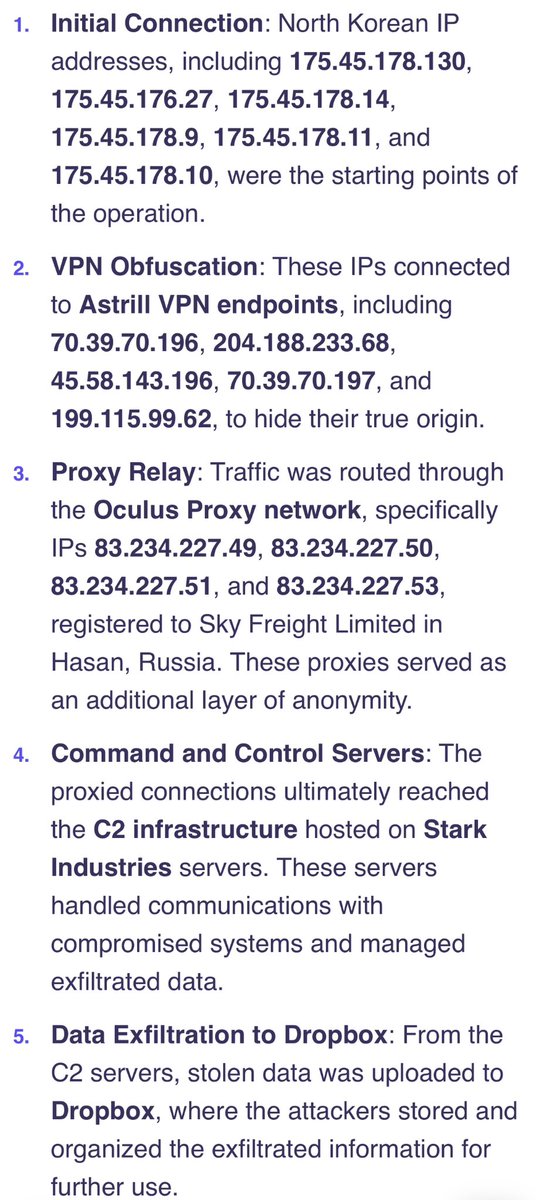
#Lazarus via LinkedIn Operation blogs.jpcert.or.jp/ja/2025/01/ini… Operation 99: North Korea’s Cyber Assault on Software Developers securityscorecard.com/blog/operation…


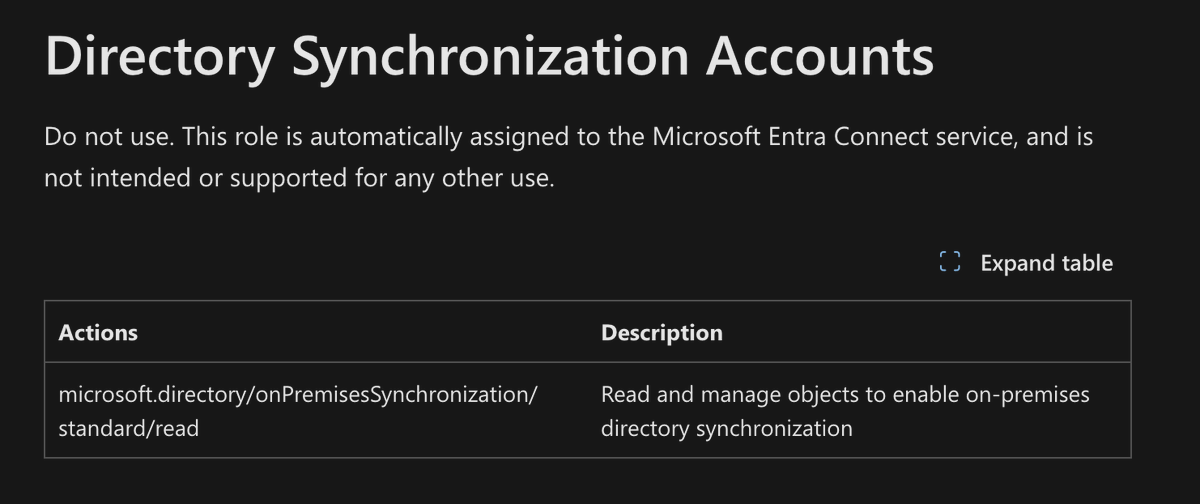
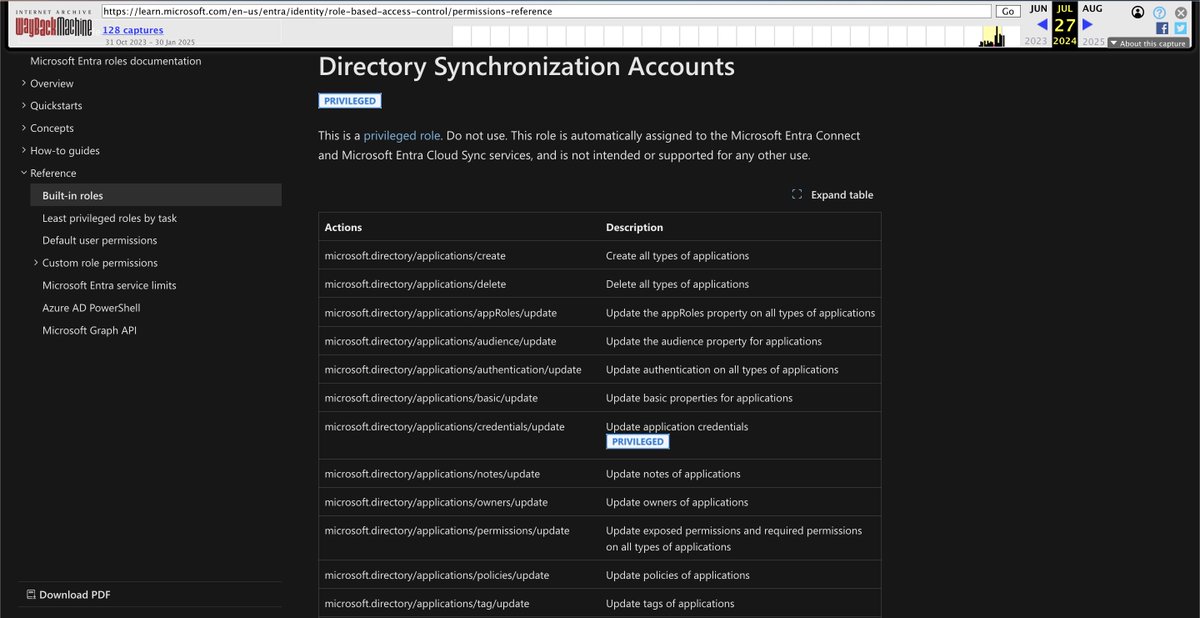
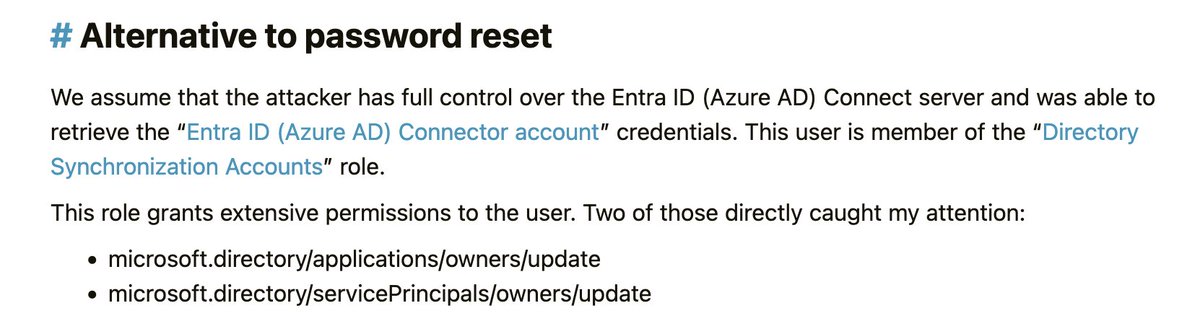
In this blog post: ● My analysis of the Midnight Blizzard breach affecting Microsoft ● Step-by-step explanation of the attack path the adversary took ● Practical, free steps ANY Azure admin can take to protect themselves posts.specterops.io/microsoft-brea…

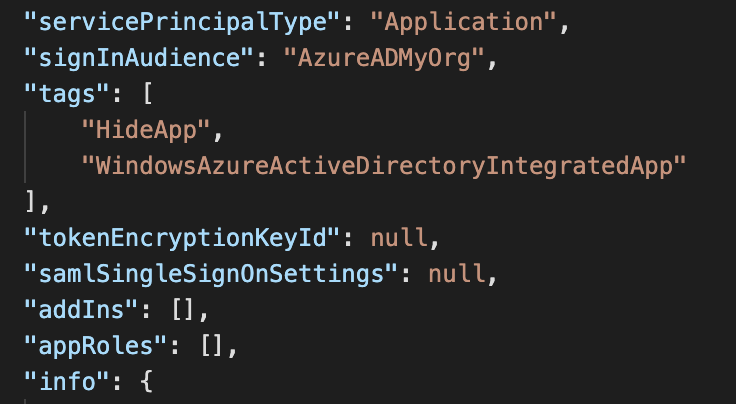
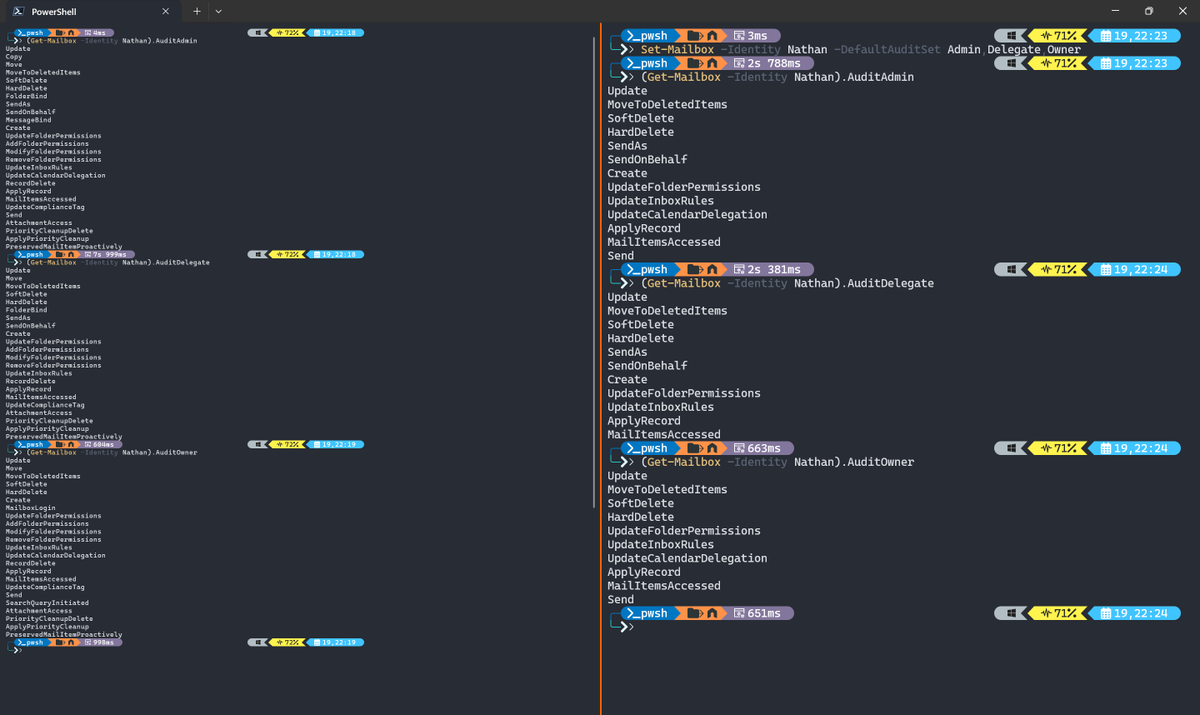
Torn on sharing this, but I think it's important everyone be aware The Office 365 Management Activity API is awesome, but it's also an incredible persistence location to monitor a victim that is almost invisible once set up Let me explain how it works and what to look for ;)




I created the first draft of a website for the EDR telemetry project to help people quickly compare vendor telemetry visibility. What do you think about it? Are there any specific features you want to see for the website? Built with ChatGPT 4o with canvas (wanted to test it out😂) EDR Telemetry project 🔗: github.com/tsale/EDR-Tele…