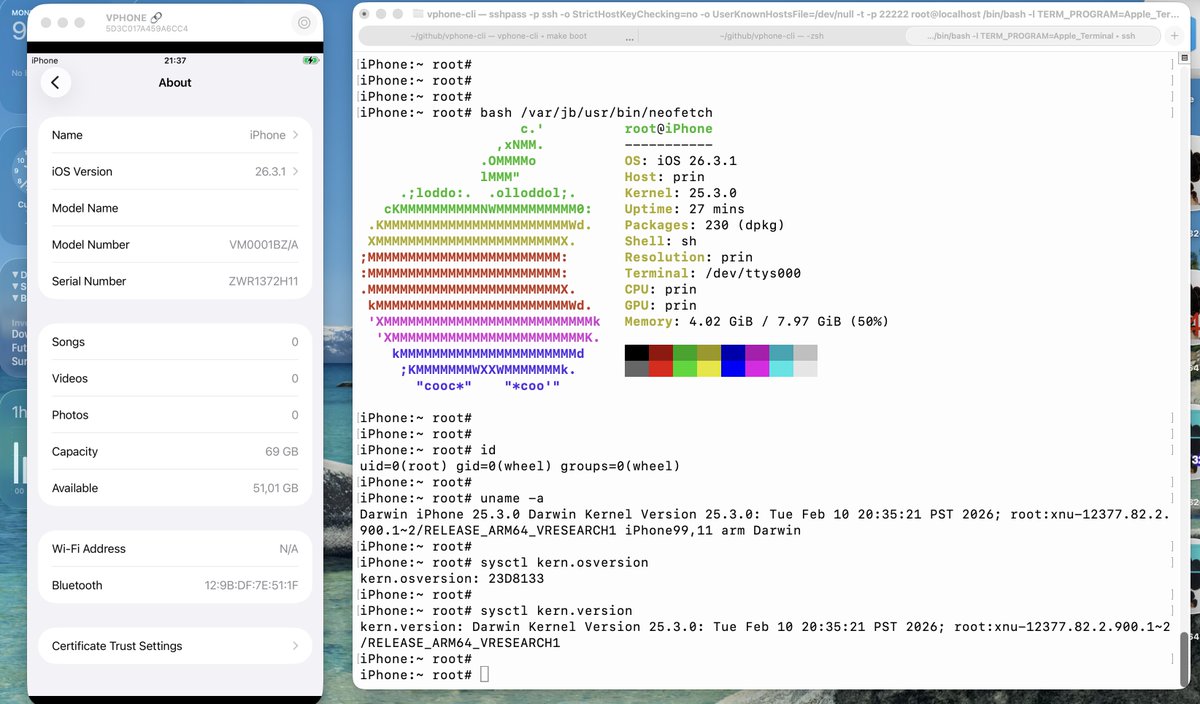
GPUBreach: A Root Shell Through GPU Abuse — and How Stealthium detects it.
stealthium.io/blog/gpubreach…
#gpu #infosec #informationsecurity #cybersecurity #vulnerability
English
Blackstorm Security
2.4K posts
@blackstormsecbr
Cyber security company focused on vulnerability research and exploit development.