Sabitlenmiş Tweet
Bounty X
27 posts


Bounty X
@bountyXAI
Universal & Blockchain Security. Protect ya neck!
Katılım Ağustos 2025
3 Takip Edilen87 Takipçiler

@c_call_me_papi @0xytocinX yes, @0xytocinX lets do spaces , bring bug bounties to SOL using TEE for payments
English

@bountyXAI @0xytocinX Maybe do a spaces with them! Would be nice
English

use our cybersecurity AI , ask for recommendations, run scans, figure out bug bounties. the platform is free
scan smart contracts , scan your infra, ask recommendations.
we will bring bug bounties to web3 using TEE for commission @0xytocinX can we run this shit
English

smart contracts vulnerabilities can be easily exploited by hackers to trigger attacks which can cause users to lose their sol/eth, we have built a sc scanner which you can use for free and scan your code before you move it to production
#ai #sol
bountyx.ai
English

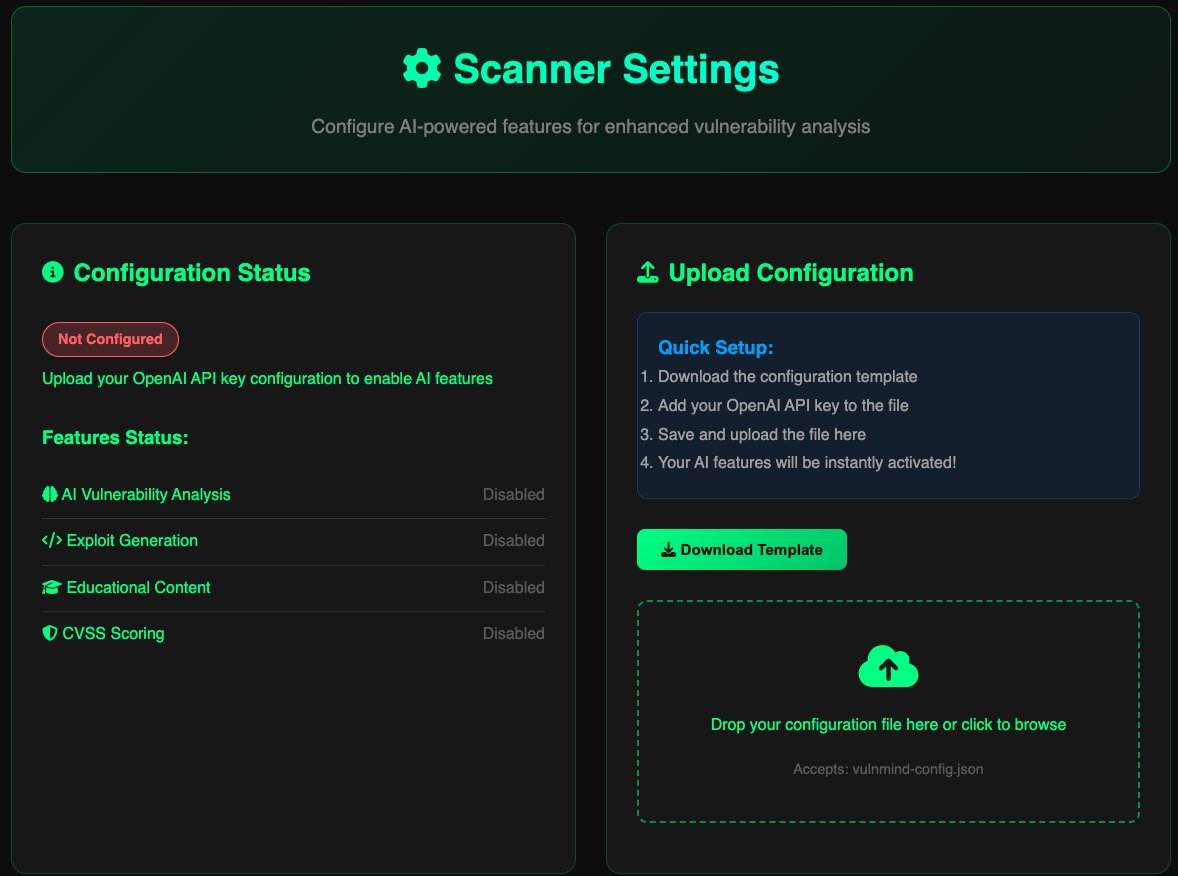
there are not many mcp server scanners available , specially for free, configure the template and use it to analyze the vulnerabilities for your MCP Severs
#ai #security #vulnerability
Prompt injection testing
OAuth token validation
JWT security analysis
Model manipulation test
English

What is the major flaw in @ethereum you may not be told about by Tom Lee that has accounted for 80% of blockchain exploits and remains unfixed and unable to be fixed.
The re-entrancy bug in Ethereum refers to a vulnerability in smart contracts that allows an attacker to repeatedly call a function before the previous execution completes, potentially draining funds or manipulating contract state. Below is a detailed explanation of the technical issues associated with the re-entrancy bug:
1. What is Re-entrancy? Re-entrancy occurs when a smart contract calls an external contract or sends $ETH to an address, and that external contract or address re-enters the original contract by calling one of its functions again before the initial execution is complete. This can lead to unintended behavior, such as multiple withdrawals of funds.
Ethereum smart contracts often use functions like call(), send(), or transfer() to send $ETH or interact with other contracts.
These external calls can trigger the recipient contract's fallback function (or other logic) before the calling contract updates its state.
If the contract's state (e.g., balances or flags) isn't updated before the external call, the attacker can exploit this by re-entering the function.
Consider a vulnerable contract:
(Solidity code)
contract Vulnerable {
mapping(address => uint) public balances;
function withdraw() public {
uint amount = balances[msg.sender];
require(amount > 0);
(bool success, ) = msg.sender.call{value: amount}(""); // External call
require(success, "Transfer failed");
balances[msg.sender] = 0; // State update after call
}
}
An attacker deploys a malicious contract with a fallback function that calls withdraw() again:
contract Attacker {
Vulnerable vulnerable;
constructor(address _vulnerable) {
vulnerable = Vulnerable(_vulnerable);
}
fallback() external payable {
if (address(vulnerable).balance >= 1 ether) {
vulnerable.withdraw(); // Re-enter
}
}
function attack() external {
vulnerable.withdraw();
}
}
When withdraw() sends $ETH (or any erc-20) to the attacker's contract, the fallback function triggers, calling withdraw() again before balances[msg.sender] is set to 0.
This allows the attacker to drain the contract's funds.
Note: This bug will be exploited forever and will risk anything substancially valauble from being passed through a Ethereum Smart Contract. This renders Ethereum as a "psuedo" Store of Value, simply holding "zipped" Layer 2 transactions with a 7 day escrow window. But dont be misled, Ethereum will never be the Execution Engine that powers the internet. It is a Proof Of Stake Store Of Value at best. But Bitcoin is a better Store of Value and Solana and SUI are exponentially better Execution Engines.
You probably dont know about this critical bug in Ethereum that has led to massive losses and limited the use of Ethereum in applications due to the insane amount of defensive code required to protect any functionality from the bug.
But within the engineering world, we know about it, have abandoned Ethereum as development tool and have moved to more modern environments and chains with real languages and without re-entrancy risks.
But Tom Lee wont tell you that. He is shilling.
English

Maybe our friends over at @0xytocinX would like to share some of whats planned too :)
English

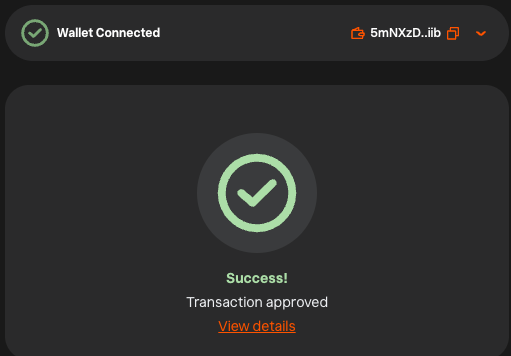
Dex has been paid!
We appreciate each and every one of you for the support and would like to share some cool things that we have coming up.
In the meantime please test out our scanners and check out our gitbook!
More to come shortly!
solscan.io/tx/iwMvvP67keu…
English

@DreamSohoPin @asym_grg The though process is there, we also agree that not paying the dex unless a certain criteria is met is a sign of poor faith on a team.
So we are in the process of paying the dex at the moment.
English

@asym_grg @bountyXAI Paying DEX means dev or team are serious
Not pump and dump
That’s all
English

Dev tokens have been locked
app.streamflow.finance/contract/solan…
English
