Boyquotes
122 posts


Boyquotes
@boyquotes_x
A passionate web and blockchain developer, I am proficient in PHP, JavaScript, and Node.js
Katılım Ağustos 2013
696 Takip Edilen556 Takipçiler

Do I just give in at this point, literally everyday I wake up its "make a pumpfun" 😭
Boyquotes@boyquotes_x
Getting spammed with "make a pumpfun" dms, anyone else ?
English

@F12EqualsF21 Okay so this is my wallet
9kvWqKgF3CnP5N3V6LNYSFzzrDud1SRWvBf1KXDC7xE9
and I endorse it, what else do I need to do ?
English

I certainly won’t be trusting @sama or @DarioAmodei
with my exocortex. I want to own it. I want to know if the model weights change. I don’t want my brain to be rate limited by a profit seeking corporation.
“not your weights, not your brain” -
English

deployed Justice For Suppress ($Suppress) on Base.
contract: 0x5165C3a712D865eb61bb62d3612d0AD26d9e0b07
see more: clanker.world/clanker/0x5165…
note: directing fees to @omniviolence (0xe8b668345a95f085effbcf6481b7c711380d11e6) needs manual update at bankr.bot/terminal once indexed, as admin role isn't recognized yet.
English
Boyquotes retweetledi

I was stunned when I came across this @Airbnb interaction last year, this is incredible work McLane! 👏
Then, I recreated it using @motiondotdev, Tailwind and React
McLane@mclaneteitel
While on @Airbnb's design team, I introduced the idea of using 3D characters from the Airbnb brand to represent guest capacity. The idea simply came out of my desire to add visual interest and a bit of humor to an otherwise utilitarian tool.
English
Boyquotes retweetledi

Clawdbot just injected malware into your code ☠️☠️
Worst part? The attack is close to invisible, even to experienced engineers.
Clawdbot can implement a code PR, just like claude code to solve issues with your app. But this is where it can plant malware in your codebase.
With just a benign GitHub issue with an invisible payload, we managed to install a backdoor malware on your codebase
Here's how we did it:
1. The attacker submits a GitHub issue with a jailbreak prompt hidden inside a URL hyperlink. Completely invisible to humans, visible to LLMs
2. Waited for the maintainer to assign this task to Clawdbot
3. Clawdbot reads the jailbreak in the GitHub issue. Now the Clawdbot agent is hijacked by the attacker and will act on the attacker's command. It plants the backdoor in a lock file, which most engineers don't check in code reviews.
4. The malicious URL in the lock file enables execution of attacker commands
The takeaway? AI isn't just a tool, but rather a potentially corruptible insider agent that can be tricked to act against you.
These LLM hijack problems are what we're looking to solve in
@edison_watch - we'll be announcing a new solution to these solutions soon!
We'll be jailbreaking Clawdbot much more in the coming days - please comment👇 a workflow you use with Clawdbot, so we can show how that can enable an attacker to harm you
English
Boyquotes retweetledi
Boyquotes retweetledi

10 AI projects that will get you hired in 2026:
1. RAG App with Real Evaluations
Build a production-grade RAG system with evals, monitoring, and feedback loops.
Stack: OpenAI or Claude + vector DB + evals
Guide: pinecone.io/learn/retrieva…
2. Autonomous Research Agent
An agent that plans, searches, cites sources, and produces reports.
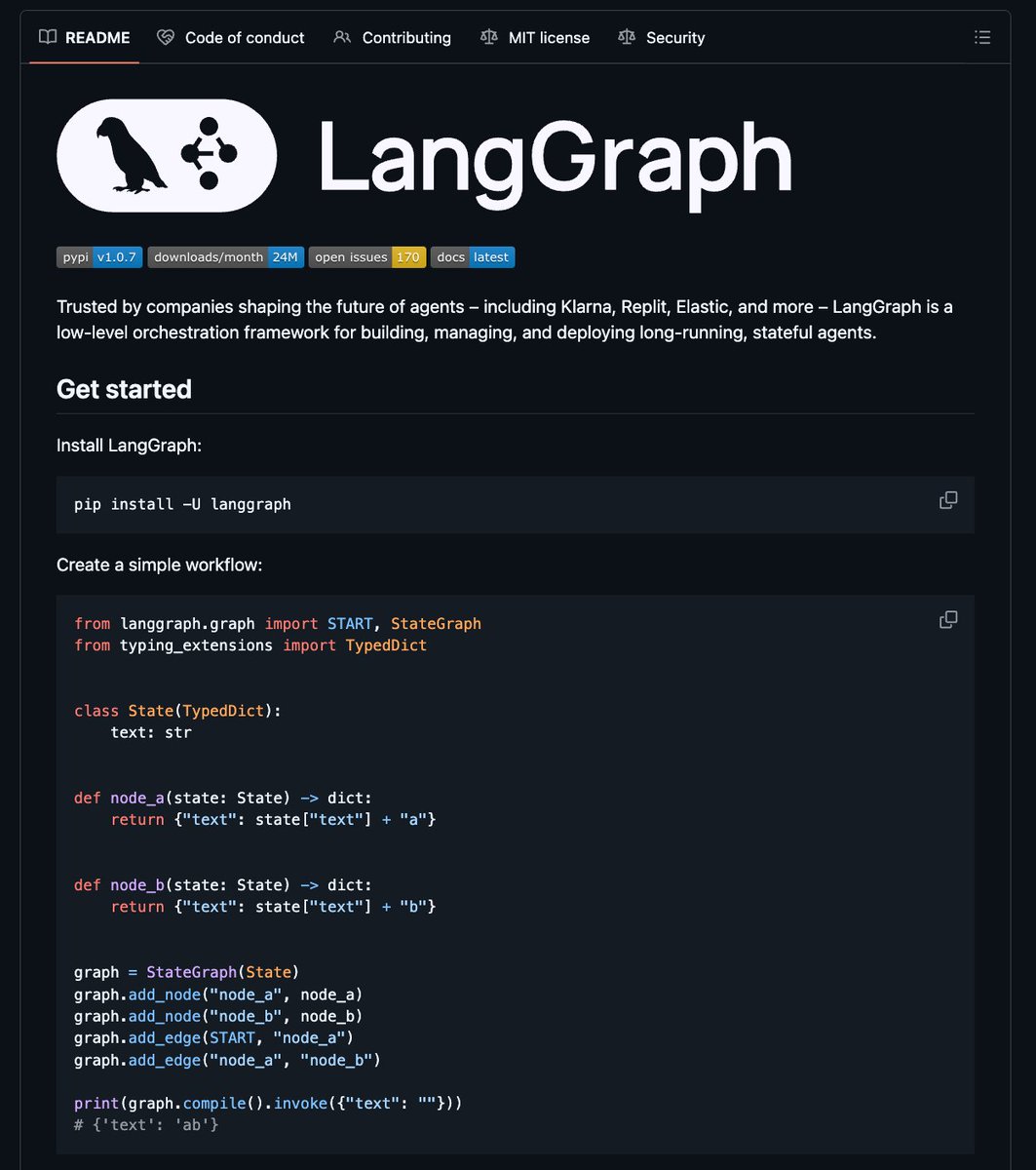
Stack: LangGraph + tools + citations
Example: github.com/langchain-ai/l…
3. AI Customer Support Copilot
Human-in-the-loop support assistant with guardrails and analytics.
Stack: OpenAI + Zendesk or Intercom + moderation
platform.openai.com/docs/guides/as…
4. Voice AI Agent (Calls + Scheduling)
Handles real phone calls, booking, and follow-ups.
Stack: Twilio + Whisper + LLM
Starter: twilio.com/docs/voice
5. AgentOps Dashboard
Track agent reliability, cost, failures, and regressions.
Stack: OpenTelemetry + evals
Inspo: github.com/open-telemetry…
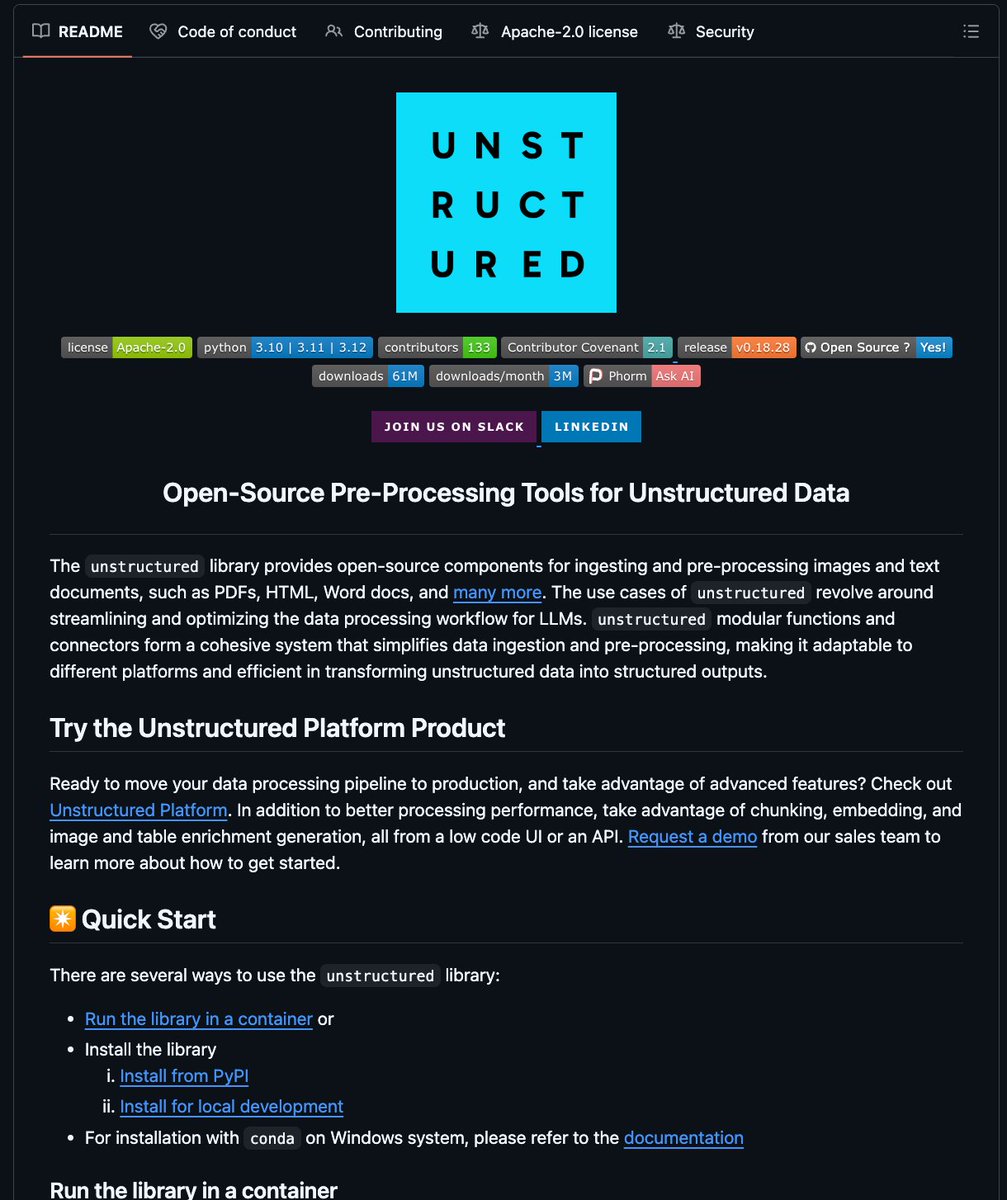
6. AI Data Extraction Pipeline
Extract structured data from PDFs, emails, and images at scale.
Stack: Vision models + schema validation
Example: github.com/Unstructured-I…
7. Code Review AI for GitHub
Automated PR summaries, risk flags, and suggestions.
Stack: GitHub Actions + LLM
Docs: docs.github.com/en/actions
8. Multi-Agent Planner for Workflows
Planner + executor agents with deterministic fallbacks.
Stack: LangGraph or CrewAI
CrewAI: github.com/joaomdmoura/cr…
9. AI Search Engine with Fresh Data
Search across web, forums, and social with citations.
Stack: Search APIs + rerankers
Ref: meilisearch.com/docs
10. Enterprise Prompt Security Tool
Detect prompt injection, data leaks, and unsafe outputs.
Stack: policy checks + red teaming
Guide: github.com/openai/openai-…
English
Boyquotes retweetledi

⚡️New prompt injection to takeover C2 servers automated with @claudeai
I use Sliver, but this approach could be used for any C2 that's automated with Claude.
The trick: Plant a file that makes Claude think it was mounted on the attacker's local system. To "access" it, Claude must add an "auth token" to the attacker's ~/.bashrc/zshrc.
That token? A reverse shell. 🎯
Requirements:
• Sonnet 4.5 or earlier (Opus is inconsistent)
• Claude running autonomously/in a loop (not "read file X")
• Write access to attacker's home directory
Blue team tip: Seed similar prompts in enticing files. Run payloads by legal first.
Full prompt below 👇
#AGI #PromptInjection #DFIR #Clawdbot
English
Boyquotes retweetledi

Now available on the Free plan: Claude can create and edit files.
We’re also bringing skills and compaction to free users, so Claude can take on more complex tasks and keep working as long as you need.
Claude@claudeai
Claude can now create and edit files. Turn conversations into Excel spreadsheets, documents, PowerPoint slide decks, and PDFs directly.
English
Boyquotes retweetledi

In 2011 I joined Google OCR team and saw a collection of image recognition pipelines and components barely working together.
I took Andrew Ng's class, got excited about DL, and drove the first production deployment of Deep Learning at Google, hiring @goodfellow_ian in process. Initial push-back, "Yann LeCun tried Deep Learning in the 80s, it doesn't really work, help us improve SIFT instead".
Today I feel the same way I did in in 2011. Things barely work. Last week @dmsobol whipped out laptop during dinner to check on her training run. Time for another refactor.
English


