Rich Warren
1.6K posts


Rich Warren
@buffaloverflow
Red Team & Offensive Security Research @AmberWolfSec // @buffaloverflow.rw.md on bsky



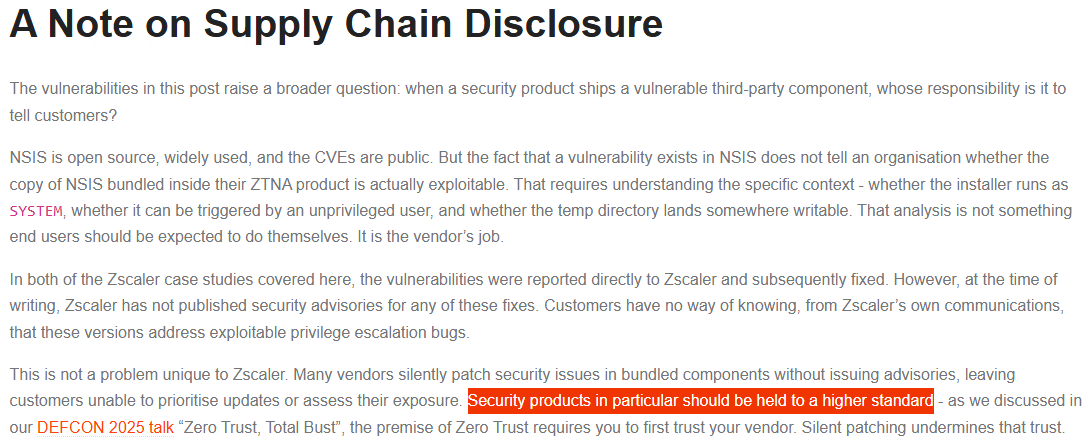
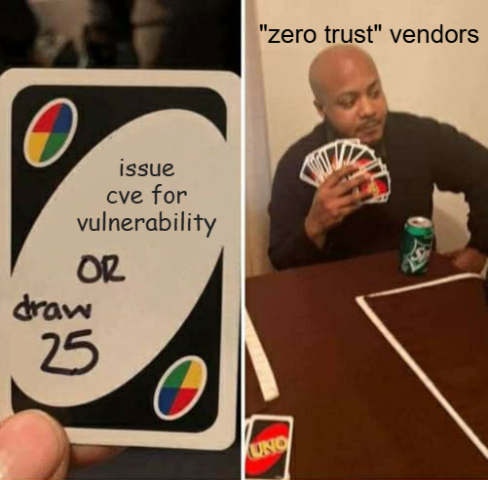
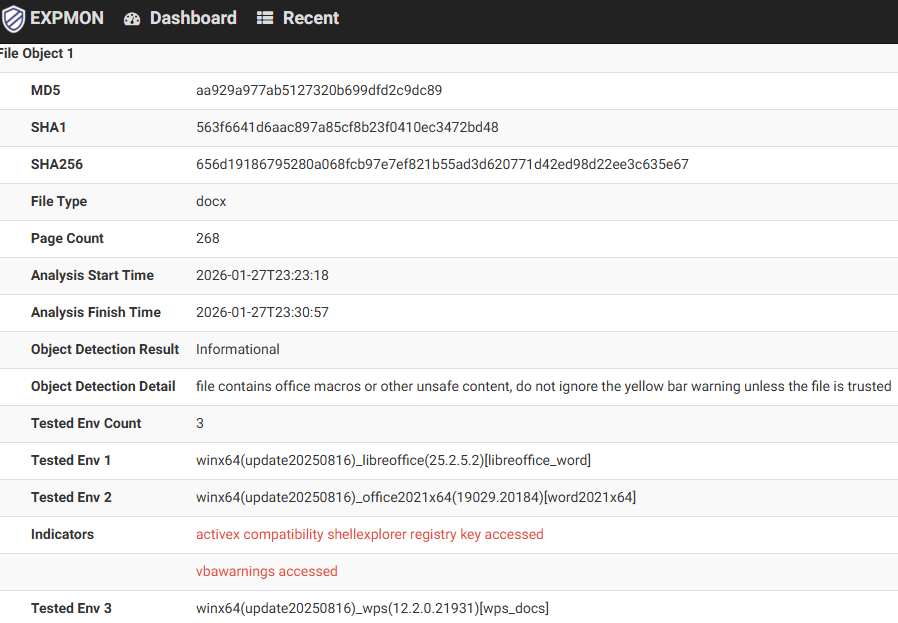
Next, Next, SYSTEM: Exploiting NSIS installer bugs to escalate privileges in Zscaler Client Connector In this blog post I show how patch gaps in Zscaler's bundled NSIS versions led to LPE.. includes PoCs and yara rule to help you find other affected s/w blog.amberwolf.com/blog/2026/apri…



Finishing off the week with a writeup of CVE-2025-0309 - Netskope Windows Client LPE This was one of the bugs we demo’d in our DEF CON #ZeroTrustTotalBust talk. Also releasing a NachoVPN plugin and our 🆙skope PoC. Details on the @AmberWolfSec blog: blog.amberwolf.com/blog/2025/augu…








‼️ Meet the guy almost everyone hates for releasing a PoC for a MongoDB unauthenticated memory leak exploit dubbed Mongobleed the day after Christmas. This is allegedly the vulnerability used to breach Ubisoft, which led to the R6 chaos.