Seven
41 posts


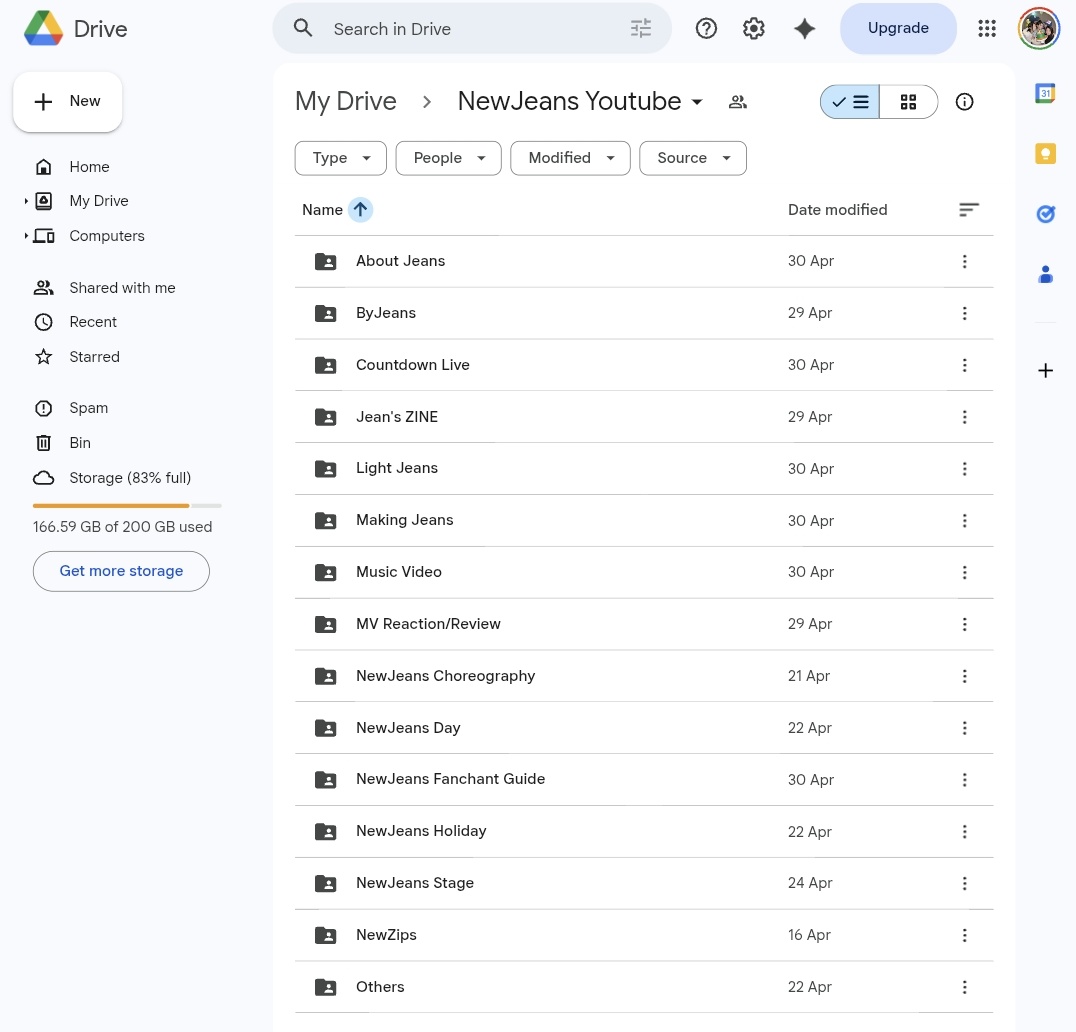


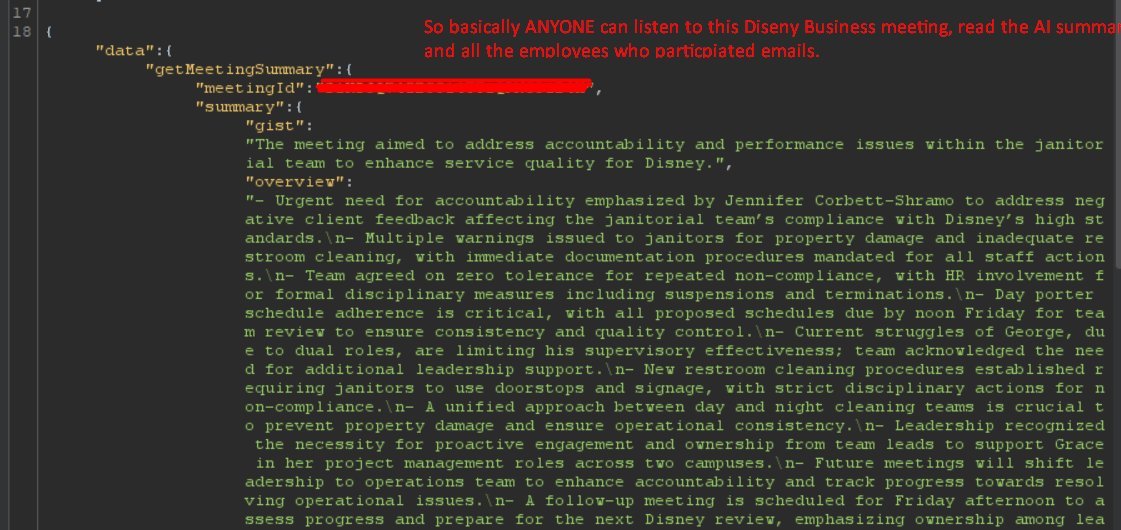
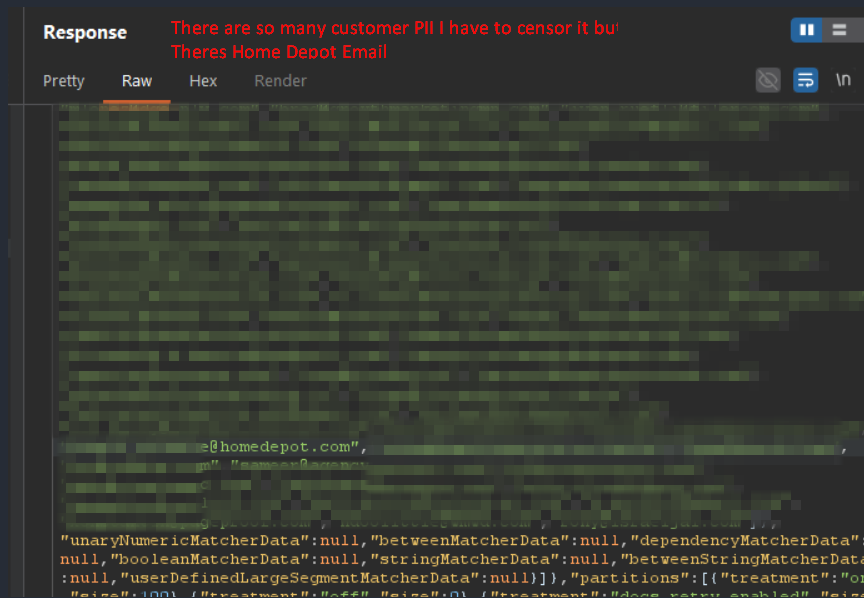
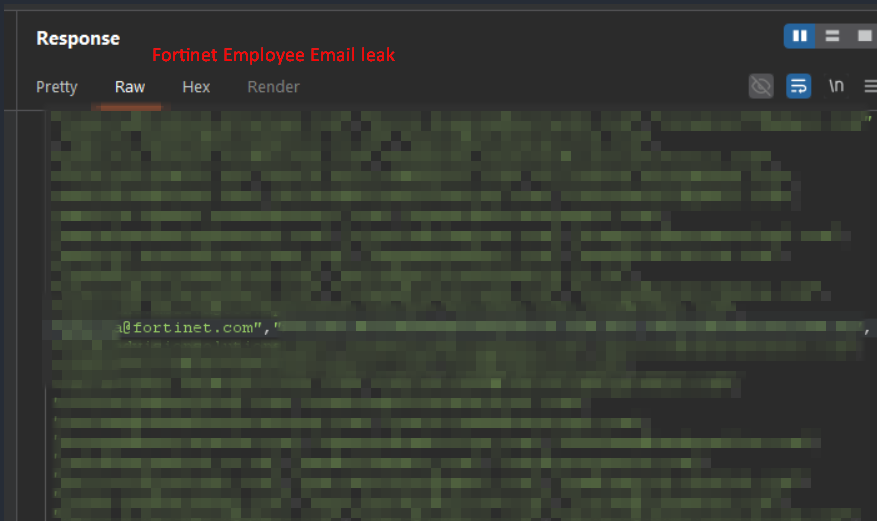
i went to clickup.com. opened the page source. found a hardcoded API key in the javascript. copied it. sent one GET request. got back 959 email addresses and 3,165 internal feature flags. employees from Home Depot. Fortinet. Autodesk. Tenable. Rakuten. Mayo Clinic. Permira. Akin Gump. government workers from Wyoming, Arkansas, North Carolina, Montana, Queensland Australia, and New Zealand. a Microsoft contractor. 71 clickup employees. fortinet sells enterprise firewalls. tenable makes Nessus, the vulnerability scanner half the industry runs. their employees emails are exposed because clickup hardcoded a third party API key in a javascript file that loads before you even log in. this was first reported to clickup through hackerone on January 17, 2025. its now April 2026. the key has not been rotated. i just pulled the response five minutes ago. every email is still there. clickup raised $535 million at a $4 billion valuation. claims 85% of the Fortune 500 use their platform. looks like the proof is in the page source.