Bas Westerbaan retweetledi
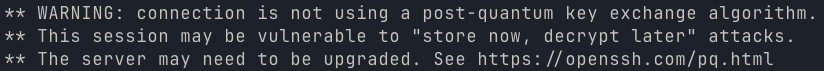
Also applies to most other privacy tech until its ubiquitous
Matthew Green@matthew_d_green
I would liken Tor to putting on Sauron's ring. The wearer is invisible to ordinary beings, like Men, but highly visible to the Nazgûl.
English