Call4pwn
121 posts

@call4pwn
Software Engineer | Cybersecurity Specialist | Pwn/RE | CTF Player @0xfun






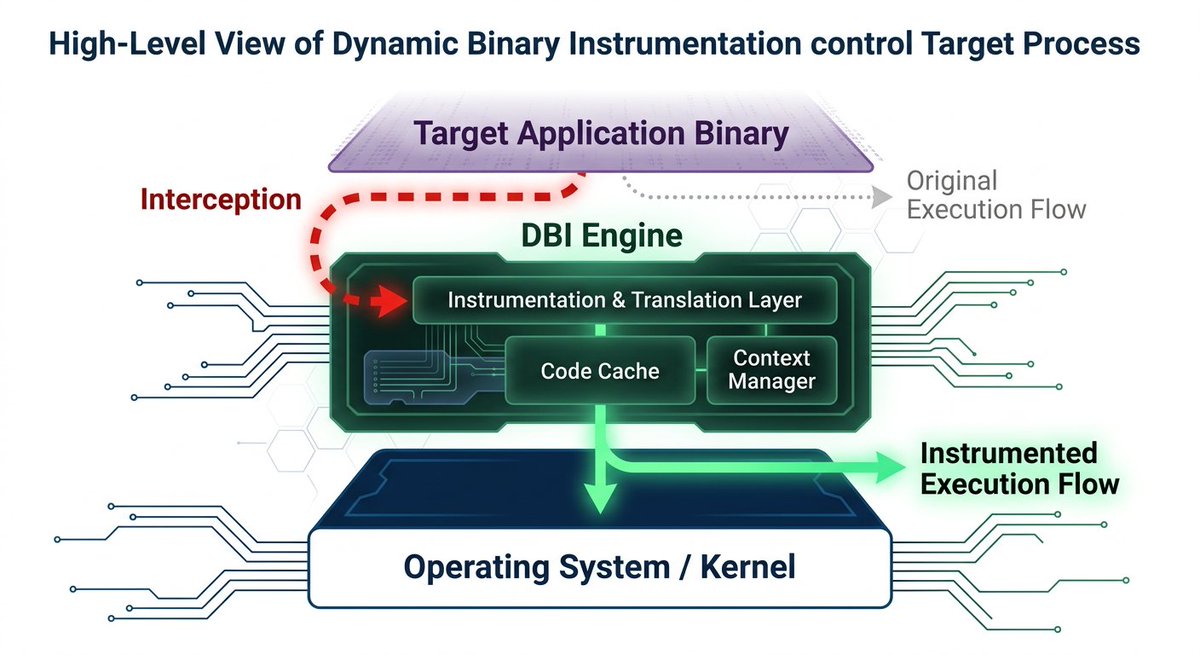
We at @verialabs built an autonomous CTF agent in a weekend and won 1st place at @BSidesSF 2026, solving all 52/52 challenges. It races multiple AI models (Claude, GPT-5.4) in parallel, each in isolated Docker sandboxes with full CTF tooling. A coordinator LLM reads solver traces and sends targeted guidance to stuck agents. As AI gets better at finding and exploiting vulnerabilities, we think it's important to understand exactly how good it is and where it fails. github.com/verialabs/ctf-…
🏁Hackena Ramadan CTF is officially OVER! 🌙💻 Flags: Captured 🚩 Leaderboards: Locked 🔒 Competition: FIERCE 🔥 Massive congrats to the top teams who dominated the scoreboard! 🏆 Thank you to everyone who brought the heat this holy month. Drop your write-ups and tag us!📝


I started playing CTFs in 2022, and LLMs definitely changed the **competitive** CTF scene a lot, especially since mid-2025. I also started using LLMs in late 2025. Yes, those models did one-shot many challenges, but what's the fun of slopping them? I learned absolutely nothing 🥲