cat name | less
222 posts







THREAD: Goodboy Framework Stage 15 is live. The final stage. A fully operational C2 agent. 0/71 on VirusTotal. Zero detections. Not a calc popup. A real C2 with encrypted beaconing, 9 commands, and a triple sandbox bypass. Here's how we got to 0/71. It took 14 iterations.




CYBERSECURITY IS ABOUT TO CHANGE FAST. Someone just open sourced an autonomous AI red team made of multiple agents that coordinate with almost no human input.




Deployed @openclaw in under 5 minutes on AWS free tier. Open source personal AI. Full system access. Interfaces through WhatsApp, Discord, Telegram. People are rigging it to their Ray-Bans for real-time price comparisons. One command. That's it.






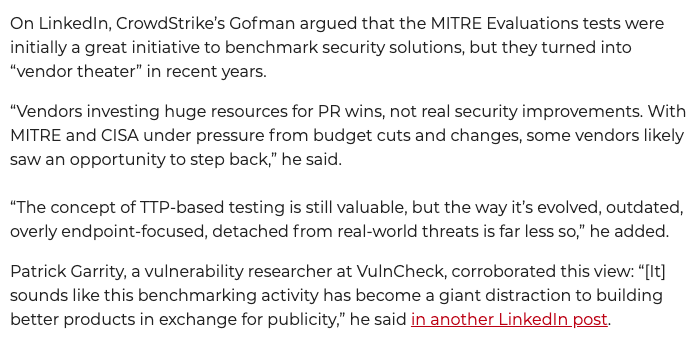
crowdstrike.com/en-us/security… fully agree with Kevin