

Clément Notin
8.7K posts


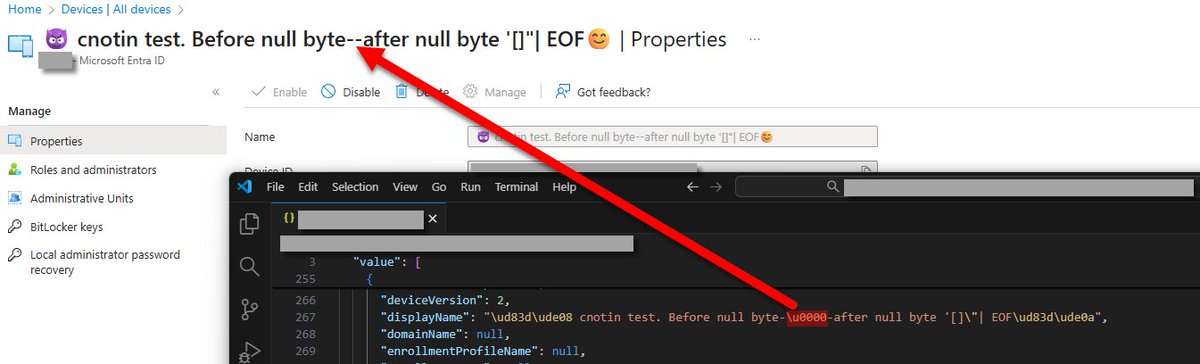
@cnotin
😈 Security research (#ActiveDirectory #EntraID) & pentest 🎉 #CTF @tipi_hack 👨💼 Works @TenableSecurity, opinions my own 🪂 https://t.co/4HRwJQ6PUm










When you see an S-1-12-1-something SID in (for example) your local Administrators group, you have no idea what it actually represents. Now that’s changing! With the new feature flag active, Windows finally recognizes Entra groups by name. No more guessing which SID, resembles which group . It's now perfect readable. #Intune #MSIntune #Windows #Windows11





Hotel toilet privacy is disappearing. ❌Glass door. ❌No door. ❌Big window into the room.. Even in rooms with twin beds... Who is asking for this?


Should Active Directory be considered "legacy"?












Here's the guidance from the docs on why this is important #inactive-applications-dont-have-highly-privileged-microsoft-graph-api-permissions" target="_blank" rel="nofollow noopener">learn.microsoft.com/en-au/entra/fu…

If my tenant has 22K applications with expired secrets, is that bad?

