CODE WHITE GmbH
178 posts


CODE WHITE GmbH
@codewhitesec
Red Teaming. Security Research. Continuous Penetration Testing. Threat Intelligence.
Ulm & Mannheim Katılım Temmuz 2014
44 Takip Edilen6.9K Takipçiler

Thrilled to announce the start of a new chapter @codewhitesec 🙂 Thank you for the welcome package 🙃

English

Highly recommend the writeup from our @flomb_ and congrats on this well-deserved achievement!
flomb - @fl0mb.bsky.social@flomb_
incredibly excited to share that my research 'Playing with HTTP/2 CONNECT' made the final @PortSwigger Top 10 Web Hacking Techniques of 2025! A huge thank you to everyone who voted. It’s a privilege to be featured alongside such talented researchers. portswigger.net/research/top-1…
English

You like technical deep dives into binary exploitation and crazy heap wizardry? Then you'll like our blog post by @0xor_solo about unauth'ed RCE in NetSupport Manager aka CVE-2025-34164 & CVE-2025-34165 code-white.com/blog/2026-01-n…
English

Our 2024 applicants challenge is officially #roasted: the full BeanBeat × Maultaschenfabrikle walkthrough is now online. Unwrap the write-up at apply-if-you-can.com/walkthrough/20… and revisit the hacks that escalated from cold brew to full breach.
English
CODE WHITE GmbH retweetledi

Latest ≠ Greatest? A Retrospective Analysis of CVE-2025-59287 in Microsoft WSUS from our very own @mwulftange who loves converting n-days to 0-days code-white.com/blog/wsus-cve-…
English

@tmechen_ Well deserved, especially after three full solves in a row on apply-if-you-can.com over the past few years.🥳
English

Friendship restored with @codewhitesec - thx for this awesome festival cup :) #ULMageddon #applyIfYouCan

English

@codewhitesec Is there somewhere we can ask for a reset? It seems that someone has overwritten an initial access path.
English

CODE WHITE proudly presents #ULMageddon which is our newest applicants challenge at apply-if-you-can.com packaged as a metal festival. Have fun 🤘 and #applyIfYouCan

English

Ten days left. The warm-up fades. Maultaschen were soft. Bean Beats were dark and burnt. But the beats of #ULMageddon will be brutal! #applyIfYouCan

English

We always love a good challenge. That’s why we’re sponsoring the 10th FAUST CTF. Game on at 2025.faustctf.net
English

We've added a new demo to NewRemotingTricks that makes deploying a MarshalByRefObject (e.g., WebClient) even easier: System.Lazy<T> creates an instance of T on serialization, which is probably more likely to be allowed than a XAML gadget getting through. github.com/codewhitesec/N…
English

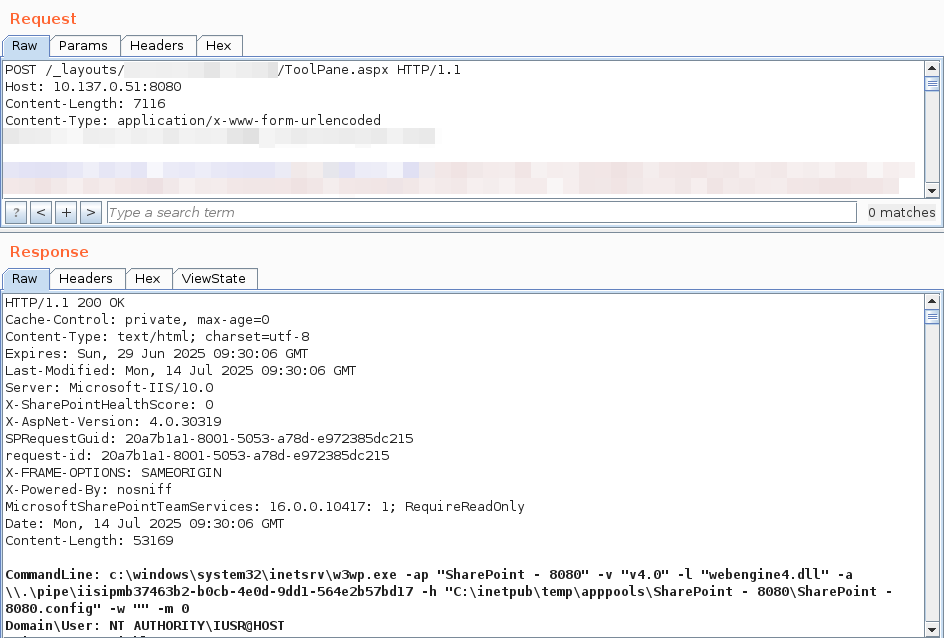
To clarify: we did not discover these bugs - all credit goes to @_l0gg. We diffed the patches, quickly built a working exploit internally (and identified another auth bypass afterwards)
English

We have reproduced "ToolShell", the unauthenticated exploit chain for CVE-2025-49706 + CVE-2025-49704 used by @_l0gg to pop SharePoint at #Pwn2Own Berlin 2025, it's really just one request! Kudos to @mwulftange
English

Yes, we're beating a dead horse. But that horse still runs in corporate networks - and quietly gives attackers the keys to the kingdom. We're publishing what’s long been exploitable. Time to talk about it. #DSM #Ivanti code-white.com/blog/ivanti-de…
English
CODE WHITE GmbH retweetledi

At @codewhitesec we have a red team style hacking challenge each year which is also a great way to practice/test/improve your skills ;)
English
CODE WHITE GmbH retweetledi

Our crew members @mwulftange & @frycos discovered & responsibly disclosed several new RCE gadgets that bypass #Veeam's blacklist for CVE-2024-40711 & CVE-2025-23120 as well as further entry points following @SinSinology & @chudyPB's blog. Don’t blacklist, replace BinaryFormatter.
English

Ever wondered how Kurts Maultaschenfabrikle got hacked in 2023? The full story, all technical details, out now ;-) apply-if-you-can.com/walkthrough/20…
English