hi^^ retweetledi
hi^^
806 posts


Fact: the size of the software stack (lines of code) is enormous. Millions of bugs remain in the IT software stack.
Personally, I think the marketing and rumor claims are somewhat exaggerated. Automation and transparency will become more important.
(4/4)
#glasswing #mythos
English
hi^^ retweetledi

🚨 Secure your virtualization layer against threats like BRICKSTORM.
Apply our recommendations, and use our vCenter hardening script to automate key security configurations directly at the Photon Linux layer.
Get details and the script the script: cloud.google.com/blog/topics/th…
English
hi^^ retweetledi

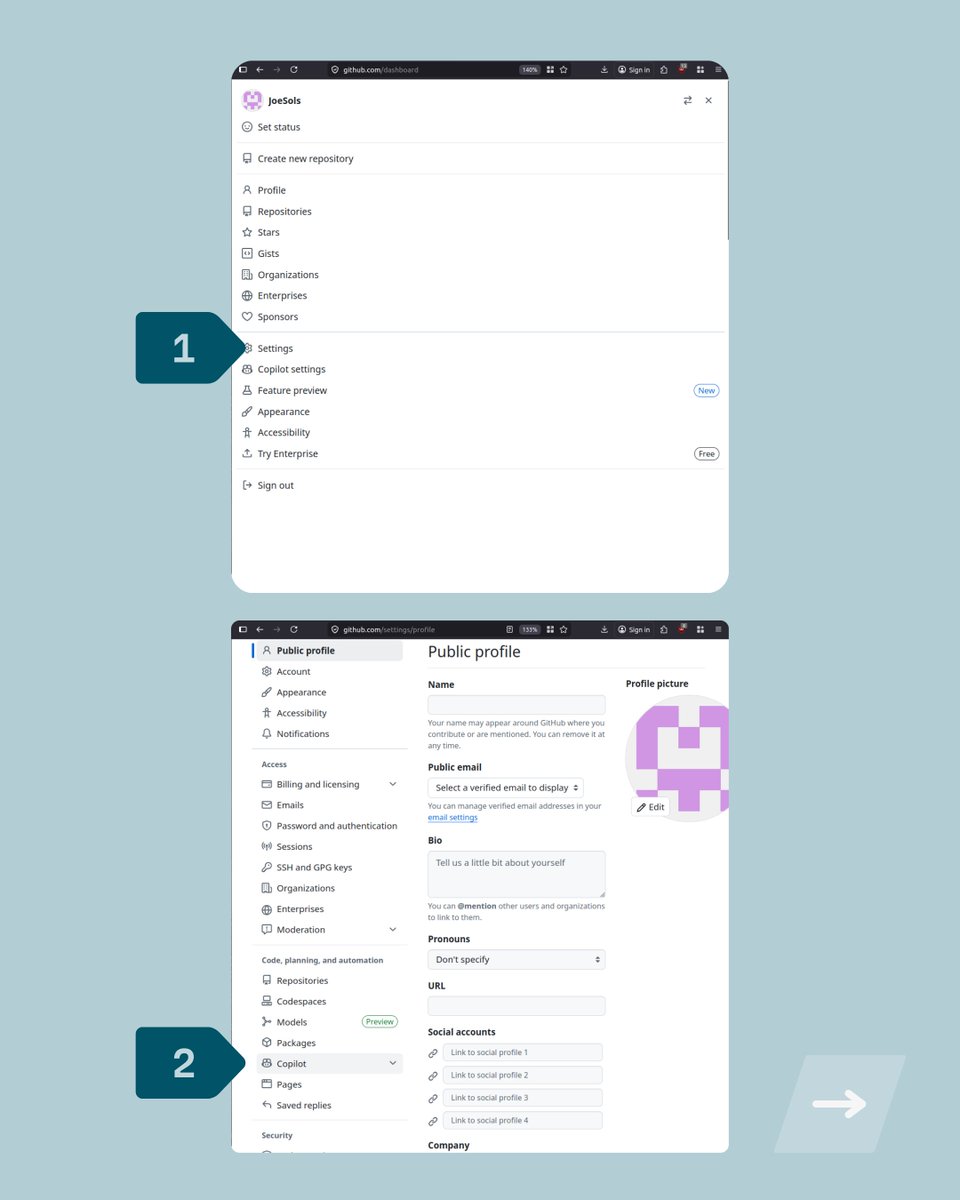
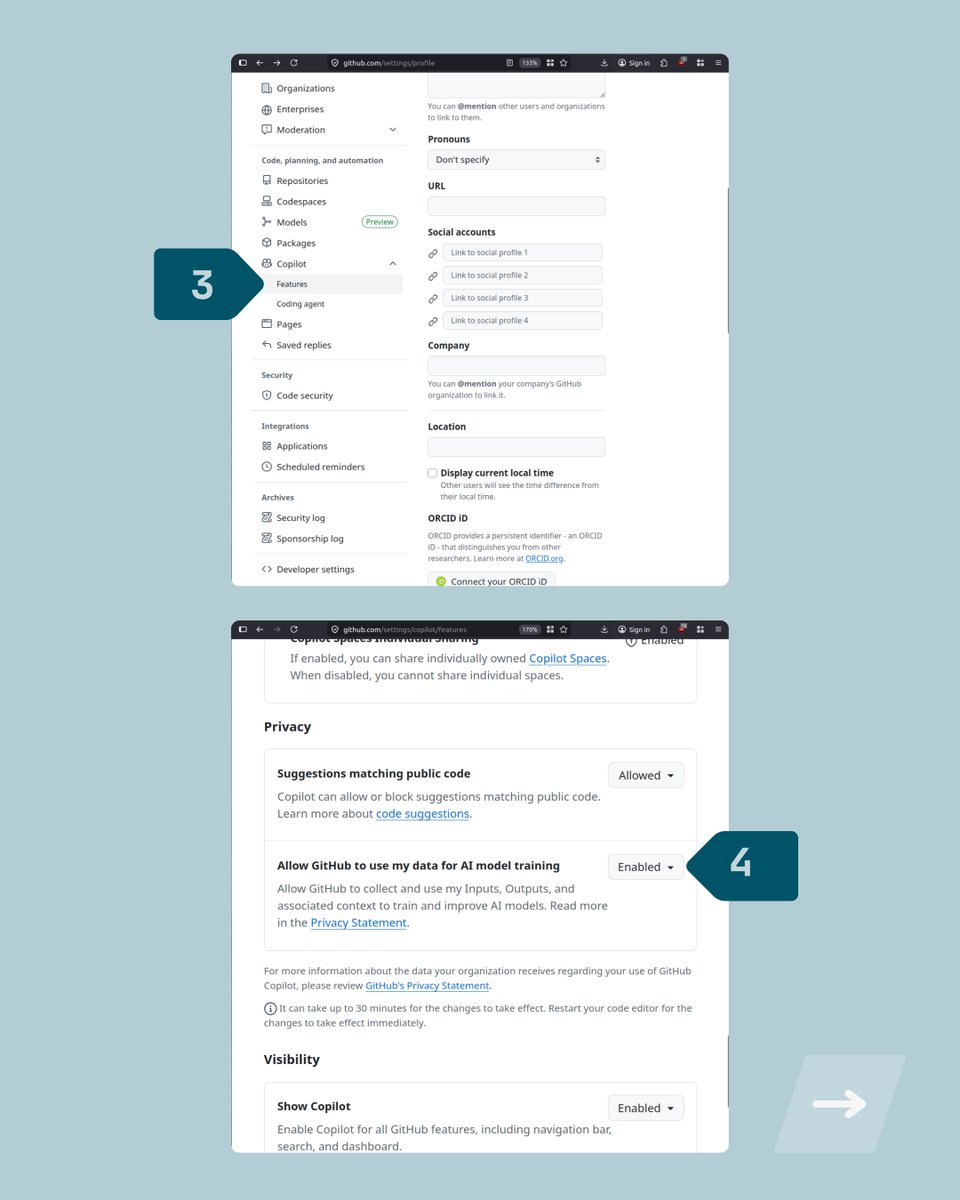
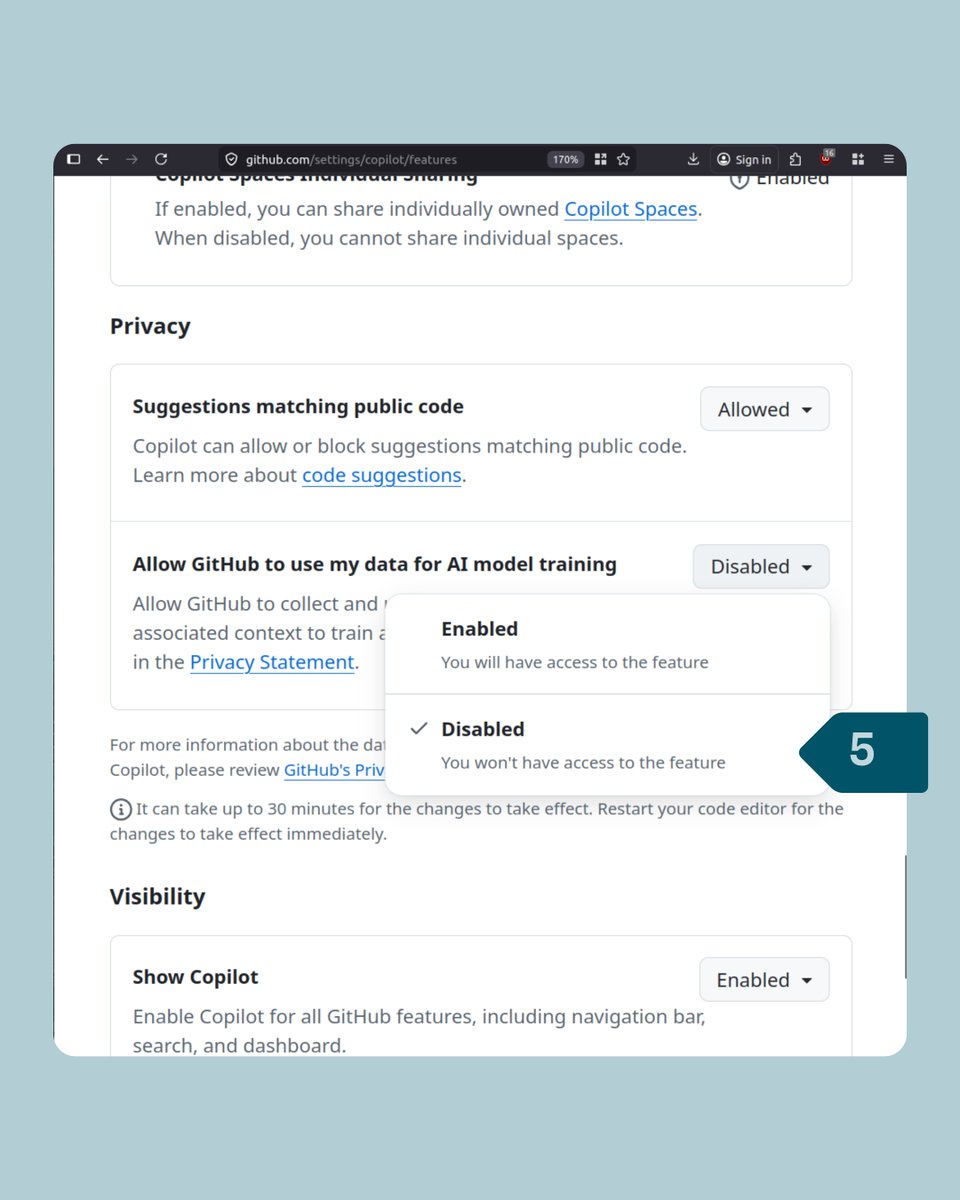
🚨 OPT OUT & say NO to #GitHub using your interaction data to train & improve its AI models. 🚨
GitHub is the next company to choose to opt you into having your data used - by default. 🚩
Opt out in Settings --> Copilot --> Features.
Under "Allow GitHub to use my data for AI model training" -→ Disabled.
It recently announced that if you do not opt out before April 24th, it will use your interaction data when using #Copilot this includes:
- Inputs & outputs
- Code snippets
- Associated context
This applies to Copilot Free, Pro, and Pro+ users.

English
hi^^ retweetledi

Citrix NetScaler RCE CVSSv4.0 9.3 - CVE-2026-3055 & CVE-2026-4368
support.citrix.com/support-home/k…
#infosec #citrix
Dansk

github.com/aquasecurity/t…
Aquasec Trivy breached again? (Last incident from 2 weeks ago: github.com/aquasecurity/t… )
#infosec #cicd #trivy
English

github.com/aquasecurity/t…
„Trivy has been attacked today via GitHub Actions, along with other popular projects: stepsecurity.io/blog/hackerbot… “
#infosec
English
hi^^ retweetledi

Yea, well, this is bad
“Google API Keys Weren't Secrets. But then Gemini Changed the Rules.”
@trufflesec
trufflesecurity.com/blog/google-ap…



English
hi^^ retweetledi

Every Entra ID assessment ends here: “How do I get a token without triggering Conditional Access controls?” 🤔
@rbnroot built CAPSlock, an offline ROADrecon-based Conditional Access engine that simulates sign-ins & flags gaps without touching the tenant. ghst.ly/4aKIk64
English
hi^^ retweetledi

This is an absolute basic for regulated orgs.
I tell people a lot: if you don't want to listen to me, fine. Listen to Mandiant.
cloud.google.com/blog/topics/th…
English
hi^^ retweetledi

What I learnt today: Mandatory User Profiles
Praetorian named their blog "Persistence Through Forgotten Windows Internals", and true, at least I never heard of Mandatory User Profiles before reading this article.
In enterprise environments, administrators sometimes want to enforce a specific user profile that resets on each login. To accomplish this, Windows supports a file called NTUSER[.]MAN (the .MAN standing for “mandatory”), which takes precedence over the usual NTUSER.DAT registry hive stored in %USERPROFILE% when a user logs in.
Setting up persistence on a copy of NTUSER.DAT using the Offline Registry Library might evade some EDRs. The whole blog post is worth a read, but the TL;DR for defender is:
Consider monitoring for NTUSER[.]MAN file creation in user profile directories, especially when it doesn’t come from an enterprise profile management system.
Source:
praetorian.com/blog/corruptin…
English

fortiguard.com/psirt/FG-IR-25…
FortiGate SSLVPN vuln CVE-2025-68686
(Not) rated highly yet. However, I would promptly patch it (and quickly move away from SSL VPN, regardless of the vendor; instead use IKEv2 EAP-TLS or WireGuard). I think this one might rapidly elevate to a RCE
English

@cyb3rops Love it, great work Flo :-)
I built something similar: Based on the info-classification (confidentiality, integrity, availability, business priority) of each application, it gets points. The higher the score the more logs necessary (authN, authZ, change, security, web, etc logs)
English

Just built a demo “monitoring matrix” for a slide in my blind spots talk.
Many orgs I’ve worked with have the same idea: “we monitor our systems, visibility is pretty good, only a few systems are not integrated yet.”
Then you put it into a simple table and the pattern is always the same: the top-left looks great. Servers and workstations send OS logs, basic auditing is enabled, some alerting exists. It feels like control.
But when you go deeper, it gets thin fast. Application logs are missing, not collected centrally, not normalized - and often there isn’t even alerting defined for them. People also rarely agree on what a “critical” application-level alert should be. That needs application owners and security to sit down and define signals. OS-level monitoring is already hard; application-level monitoring is where many programs stop.
And when you expand the coverage, it gets harder too. The further you move away from the “standard” systems, the more limits you hit: legacy systems, appliances, OT/embedded, unusual platforms, proprietary log formats, limited access, sometimes legal or organizational limits. Even if you get logs, they are often not easy to ingest and use.
Main point: “we have monitoring” is not a checkbox. It’s a spectrum - and many environments are fairly wide, but shallow.

English

msrc.microsoft.com/update-guide/v…
Azure Front Door CVE-2026-24300 CVSS:3.1 9.8 / 8.5
Anyone additional information?
#infosec #azure
English

@techspence Can you share a screenshot, timestamp, hostname, username and the whole error message?
Is the problem reproducable?
English