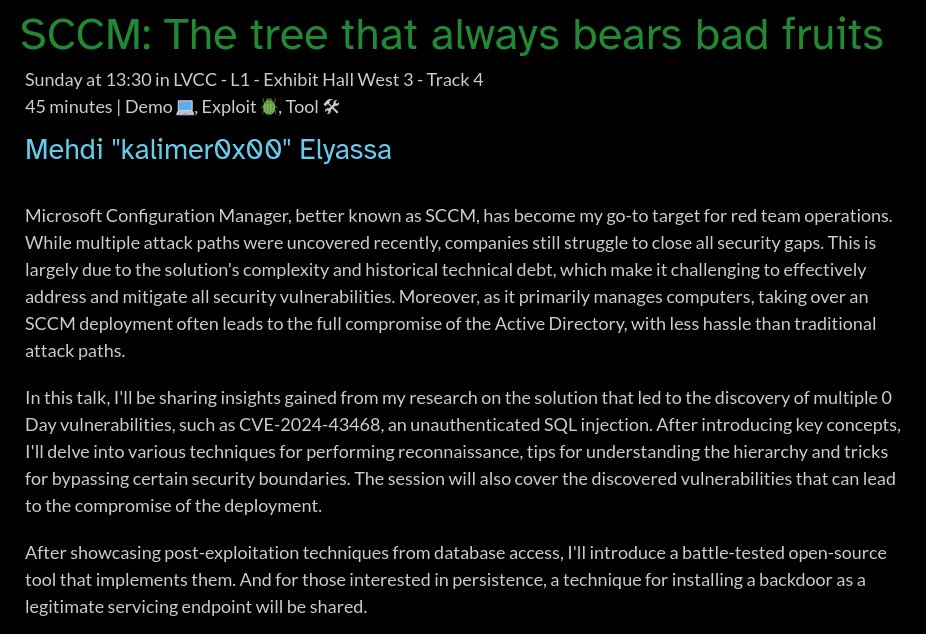
Quentin Roland retweetledi

SCCMSecrets.py: Exploiting SCCM Policies Distribution for Credentials Harvesting, Initial Access and Lateral Movement, by @croco_byte
synacktiv.com/publications/s…
English
Quentin Roland
70 posts

@croco_byte
Pentester @Synacktiv 🤖 https://t.co/FhHN2RnPym










I can confirm there will be a Windows Active Directory lab at @_barbhack_ 🏴☠️ This is an insane lab for the time allowed, be prepare and make sure your tools are up to date ! 🎯👿














Microsoft just released the patch for CVE-2025-33073, a critical vulnerability allowing a standard user to remotely compromise any machine with SMB signing not enforced! Checkout the details in the blogpost by @yaumn_ and @wil_fri3d. synacktiv.com/publications/n…