Big C
74 posts

Big C
@cyphercoreX
Cybersecurity & Python learner | Sharing the grind + building Cyphercorex ⚡
Katılım Ekim 2020
41 Takip Edilen2 Takipçiler

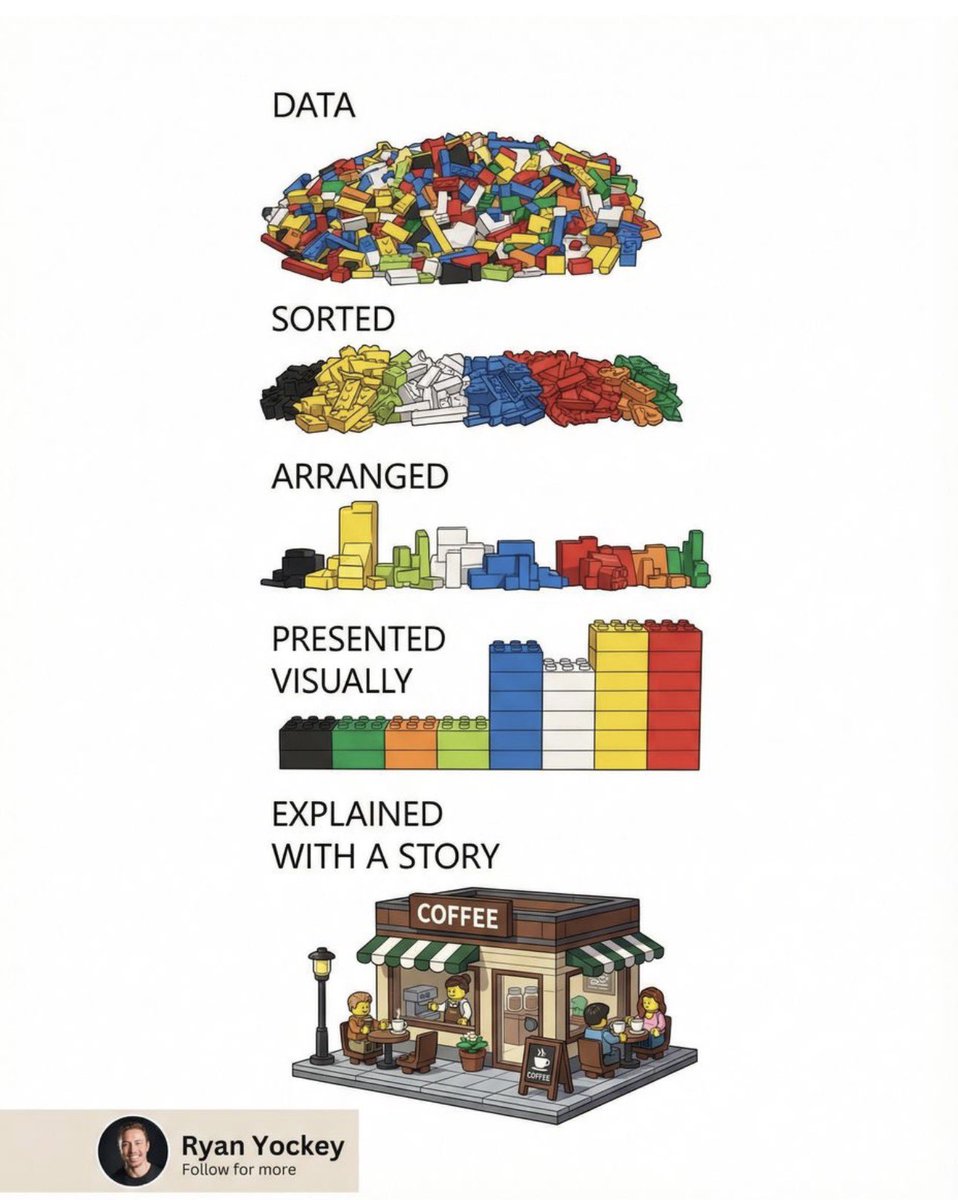
Learn why they exist before learning how to use them.
Master fundamentals first. Tools then become force multipliers.
#CyberSecurity #BlueTeam #RedTeam #OSINT #Forensics #Networking #InfoSec #ContinuousLearning
English
Big C retweetledi
Big C retweetledi
Big C retweetledi