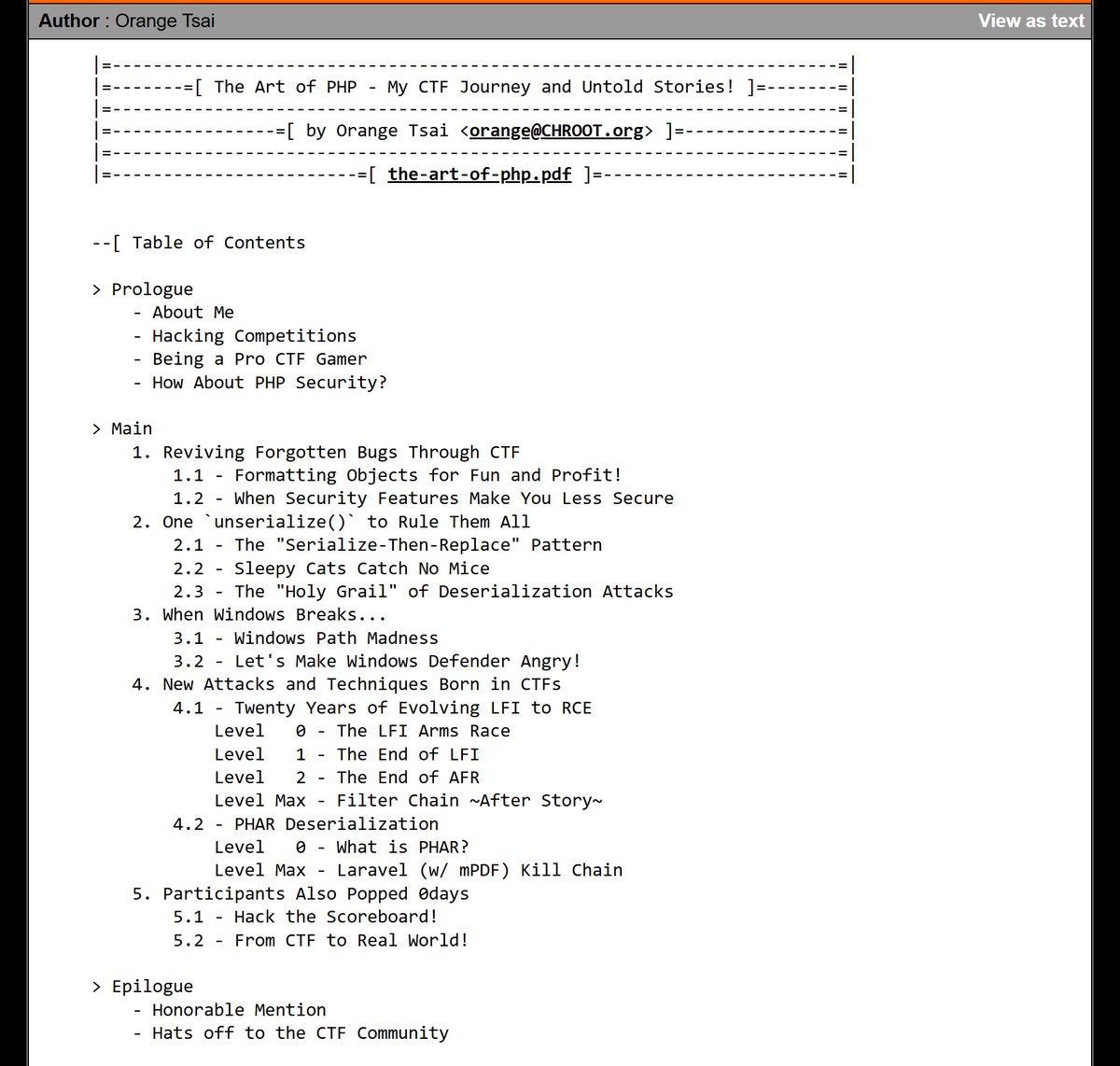
Sabitlenmiş Tweet

After January's patch of KeePass trigger abuse technique, I decided to take a deep dive into the software features, ending up with new ways to extract passwords through the the configuration file!
Details and mitigations below, enjoy the read ✌️
d3lb3.github.io/keepass_trigge…

English