Daniel Bradley
1K posts


Daniel Bradley
@DanielatOCN
Microsoft MVP, blogger and I write a little PowerShell


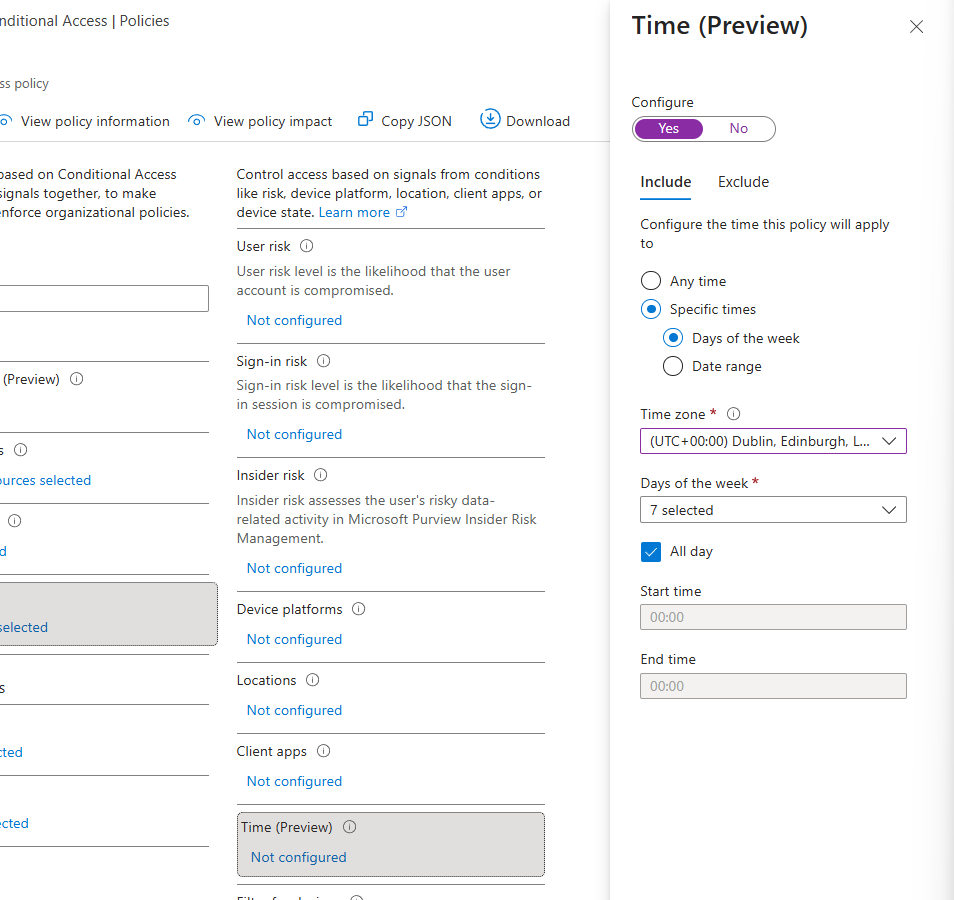






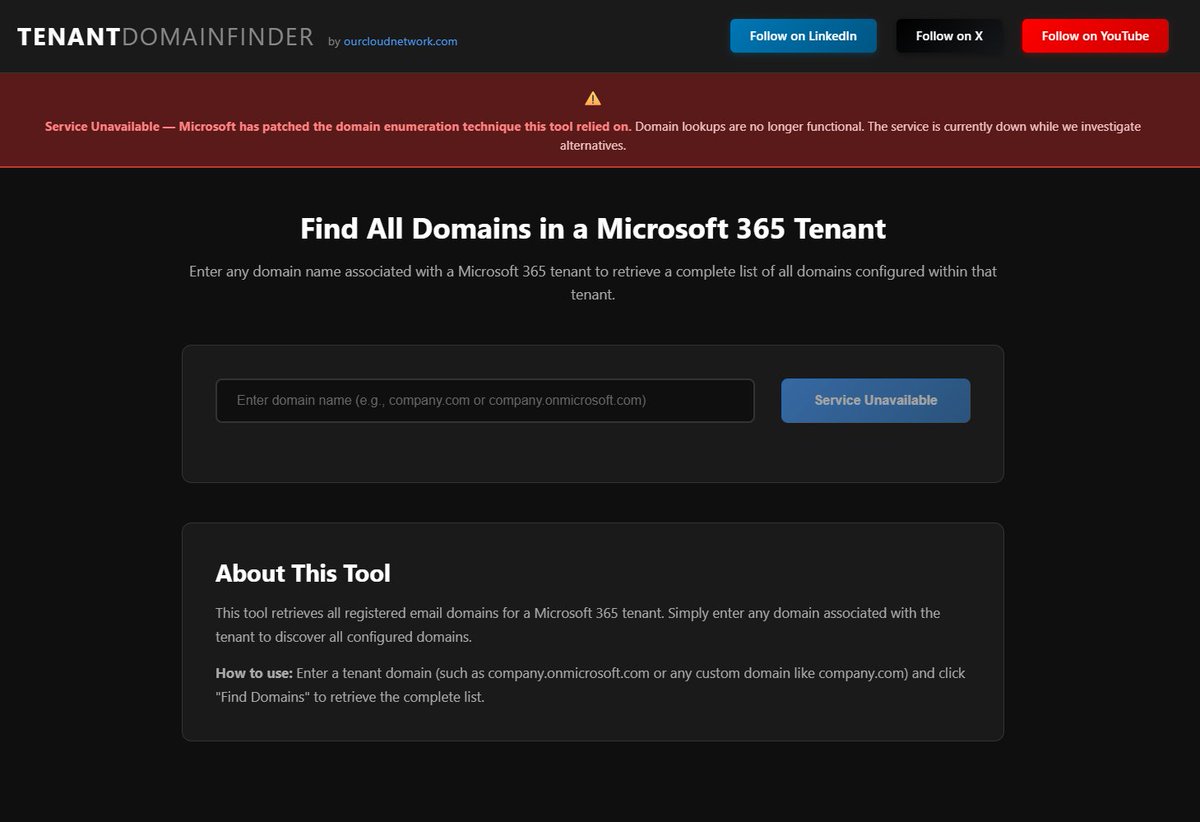
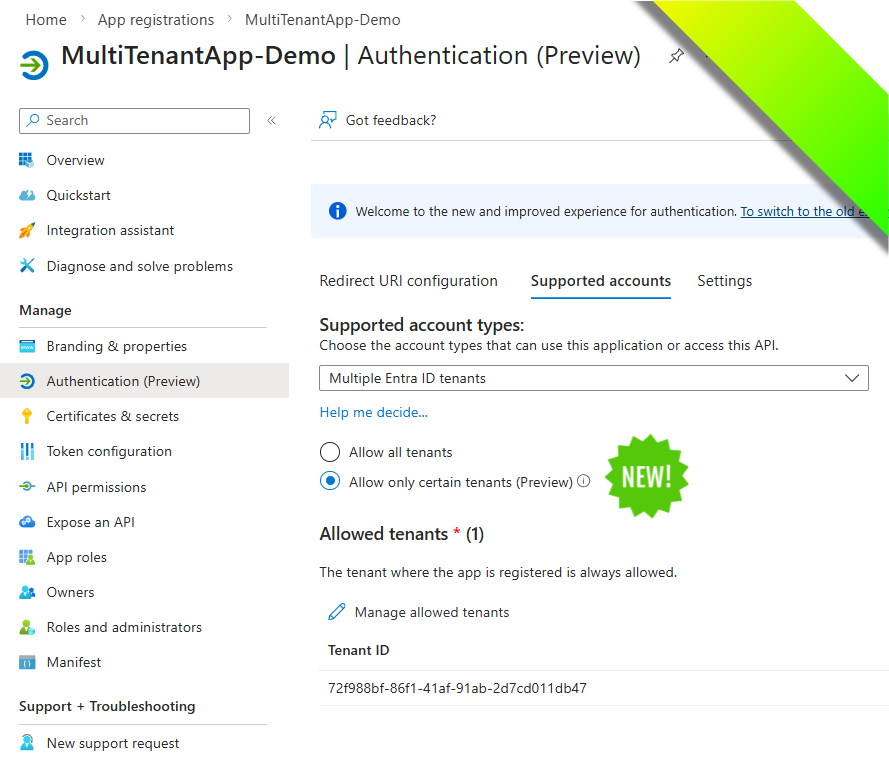
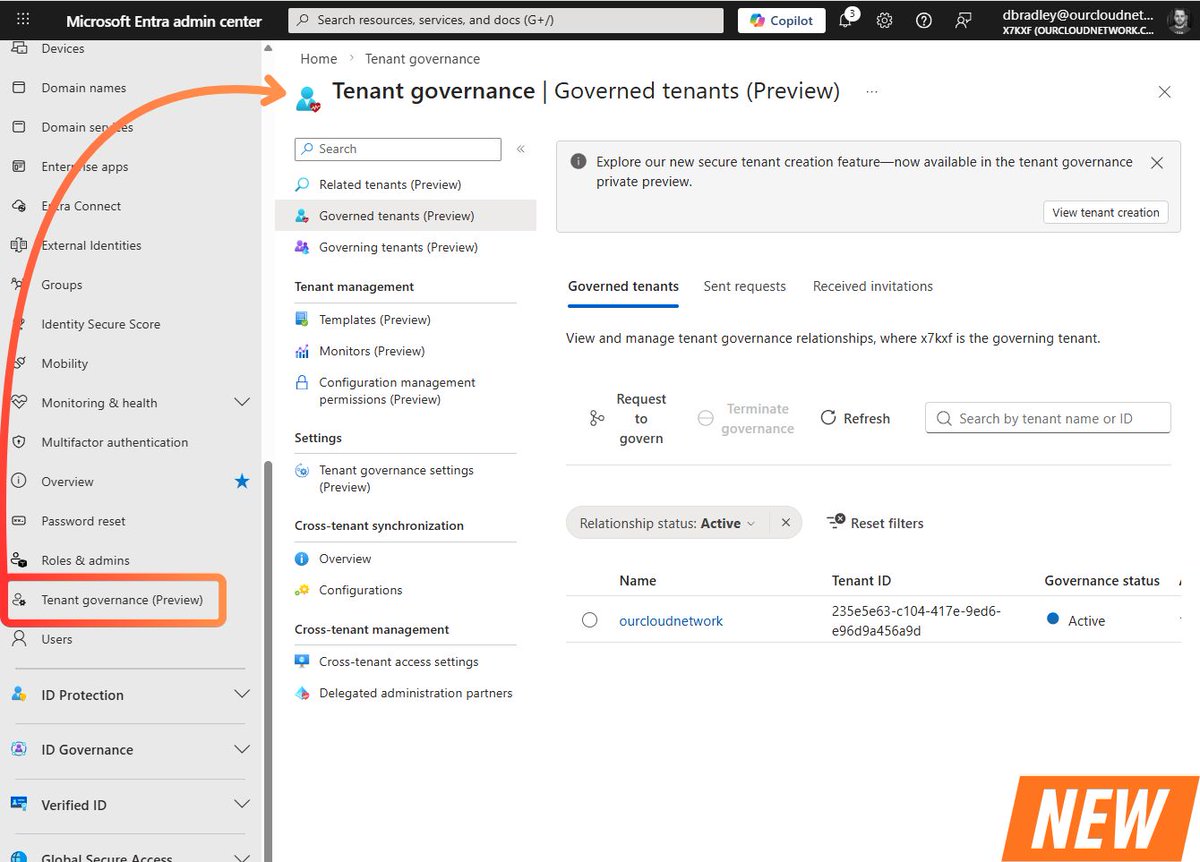
Native multi-tenant configuration drift management is now built directly into Microsoft Entra, take a read > ourcloudnetwork.com/use-entra-tena… ❤️ With the recent release of UTCM, the engine behind the snapshots, baselines, monitors and drifts, Tenant Governance adds a framework that enables you to apply the UTCM engine, as well as management permissions across multiple Microsoft Entra tenants! Another game changer for Entra!


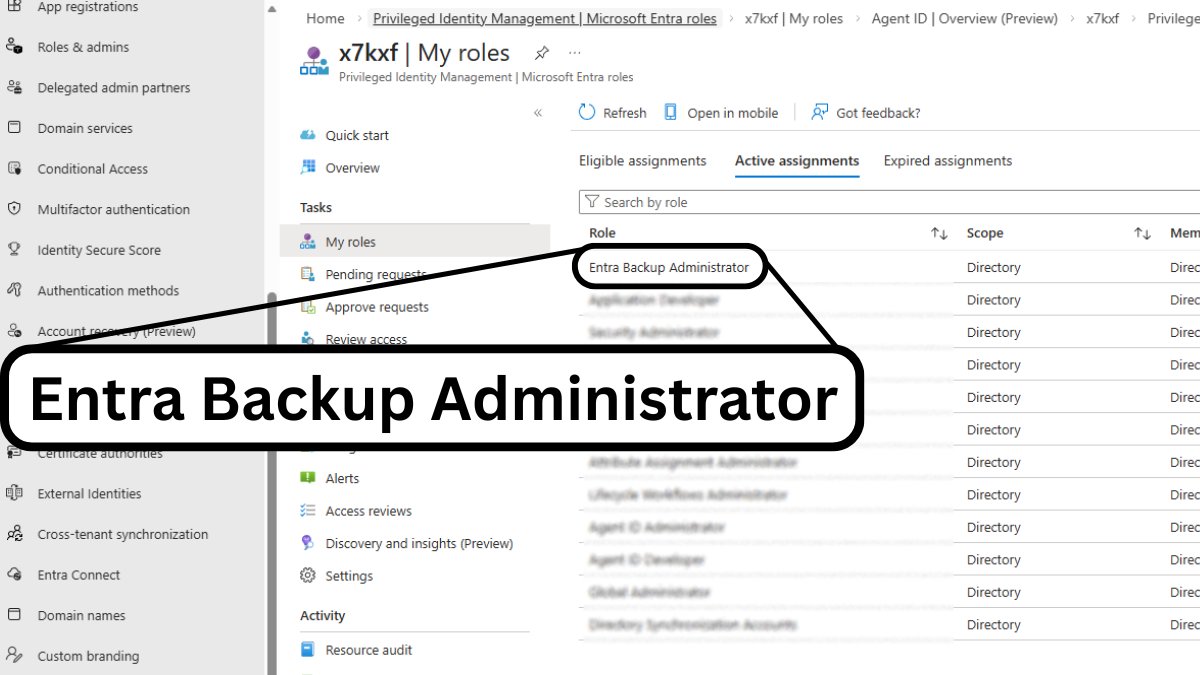
Microsoft Entra Backup just dropped this morning! I talked a little about this in my previous blog > ourcloudnetwork.com/microsoft-entr… You get: • Automated backups taken once per day for the last 5 days! • Ability to revert objects to any previous state within the last 5 days! • To view the difference reports to see the state difference between backups! Yes, it is not a foolproof solution, and the retention doesn't account for the average time an attack can go unnoticed! But, it's better than nothing and a huge step forward! #Entra #Microsoft #Backup