David Benjamin
423 posts


David Benjamin
@davidben__
There are lots of people with my name. I'm the Chromium (and cuttlefish) one. I work on TLS, privacy, and general amusements in Chrome.
Katılım Kasım 2014
144 Takip Edilen994 Takipçiler

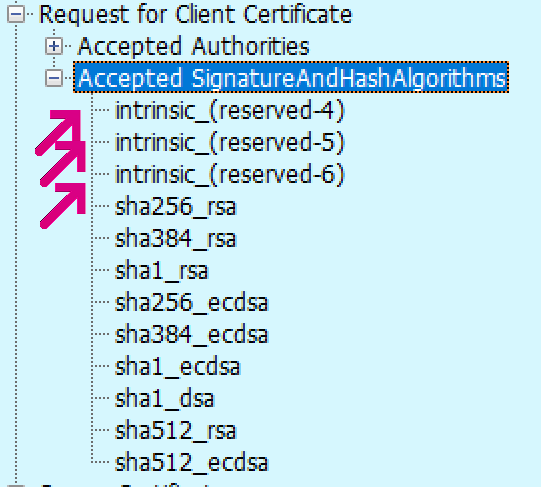
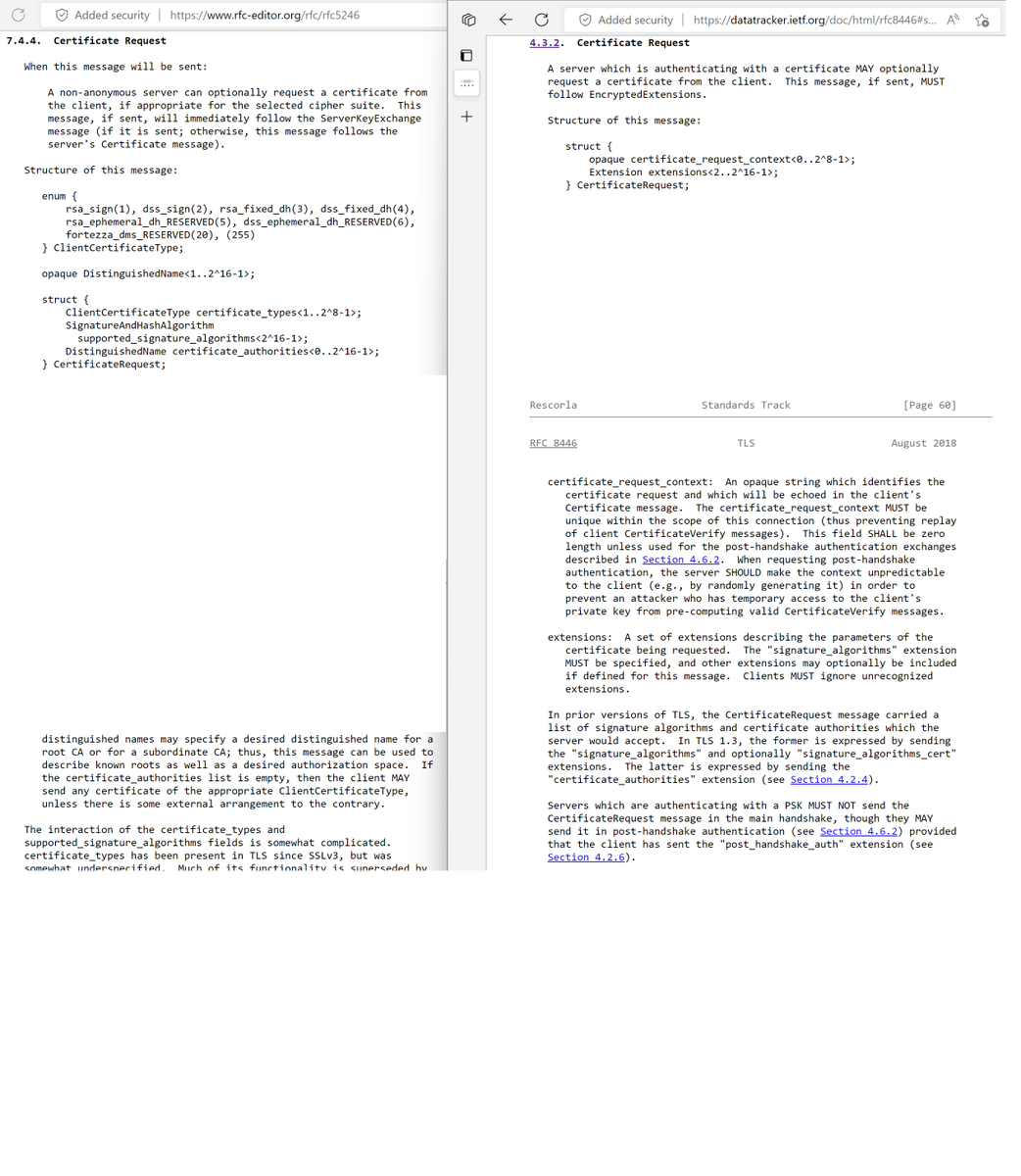
@ericlaw Probably PSS and your decoder hasn't been updated for 1.3? The codepoints are no longer decomposed into hash/sig tuples as that's not how signature schemes work in general.
English

@ericlaw TLS 1.2 changed a bunch of them too, to add the signature algorithm. Anything after ClientHello and bits of ServerHello has always been version-specific and fair game to change.
English

@h4kr @BruceDawson0xB That guidance always worried me. Asking devs to think about worst case bounds on every map feels akin to thinking about whether some missed check is exploitable. Much lower stakes, but still a bit error-prone of a default for my comfort.
English

@BruceDawson0xB I wondered about those containers before, and if they should have a DCHECK that n < $MEDIUM_SIZED_VALUE. But I'm not sure how you'd argue for a particular MEDIUM_SIZED_VALUE in a CL. :)
English

@taviso @GuidoVranken Different reuse there, but yeah X509's setters basically don't work. Except you need to setters to issue certs, so it's a mess. No idea whether anyone actually relies on this particular case. I just reviewed the diff and noticed it broke something they previously had code for.
English

@GuidoVranken I was so annoyed when I found this lol marc.info/?l=openssl-use…
English

@BRIAN_____ It also catched bugs. We learned as a result that a few projects imported RSA keys wrong and swapped p and q! They just never noticed because CRT would always fail and then fallback in OpenSSL, making RSA signing unnecessarily slow.
English

@DrawsMiguel @shafikyaghmour I want a strict aliasing sanitizer, less to check my code (though that too) but really to demonstrate that no real world C code actually follows that rule.
English

@BRIAN_____ @djco @FiloSottile The spec reference in the bug is wrong; ClientHello.legacy_version is not the same as the record layer version.
And yeah I doubt that is the issue. The record layer version is totally meaningless and vestigial.
English

@djco @FiloSottile @davidben__ I wonder if the issue is really that. I suspect the reporter is speculating. I wouldn’t be surprised if the real reason is cipher suite incompatibility, e.g. server requires non-ECDHE RSA key exchange. Presumably the peer is Schannel which does version negotiation pretty OK.
English

@FiloSottile @davidben__ any thoughts on github.com/rustls/rustls/…? (What version to send in ClientHello?)
English

@hanno @buherator @agl__ Thanks to that mess, it takes more bytes to encode RSA-PSS *parameters* in X.509 than to encode an entire ECDSA signature. PSS is singlehandedly the reason X.509 signature algorithms aren't a plain enum.
English

@buherator @agl__ RSA-PSS allows you to choose a hash function, a mask generation function (for which there is only one option), a salt length and a hash function for the mask generation function (yes, you can have a pss sig with two different hash functions). any more questions?
English
David Benjamin retweetledi

Picking parameters: imperialviolet.org/2022/03/15/pic…. (It was too long for Twitter.)
English

@FiloSottile @taviso @GuidoVranken Whether it's a bug in ModSqrt is up to interpretation. Tonelli-Shanks ultimately only works for primes. Always terminating is prudent. But accepting random attacker-supplied coefficients is a bad idea and forbidden by RFC5480. IMO that's the root bug, which doesn't affect Go.
English

@taviso @GuidoVranken @davidben__ Yeah, we have the same issue at the bignum layer, but we don't support custom curves, so we don't know of any vector of attack.
In fact, I am working to make all of math/big unreachable from crypto packages.
Yay for limiting complexity and attack surface :D
English

This was a fun one to work on, @davidben__ helped track it down to a bug in the Tonelli-Shanks implementation in OpenSSL.
Randori Attack Team@RandoriAttack
New high severity DoS in OpenSSL just released: openssl.org/news/secadv/20… CVE-2022-0778 was reported by @taviso and appears to affect systems that parse user-supplied certificates.
English

@bascule @SchmiegSophie @cryptodavidw @cronokirby Malleability of (r, s) aside, parsing ECDSA signatures with DER should be perfectly compatible with real world TLS. Our implementation is strict, and OpenSSL hasn't accepted invalid DER here since 2015.
English
mesur-io.github.io/post-quantum-s…
Maybe a bit of a hot take, but I feel like you should just encode public and private keys as a string of bytes, and treat them as completely opaque blobs. Not sure what you really gain by exposing the internal structure as JSON
English
I would ask @sleevi_ or @davidben__ but I expect they just read the raw hex directly.
English

@RichSalz @sleevi_ @bascule @cwallace_bass I still don't even know how to read the new syntax! I can guess at it, but I've yet to have to learn it properly.
English

@sleevi_ @bascule Put another way: constructed is a property of the value, not the tag. It tells you whether the value is more TLVs or some random leaf element. So EXPLICIT is always constructed (wraps another TLV). IMPLICIT replaces the tag, so its constructed bit is based on the inner element.
English

@__phantomderp @strega_nil @DrawsMiguel imperialviolet.org/2016/06/26/non… is the memcpy language bug. That one is bad enough that we had to add wrapper functions for memcpy because constantly worrying about whether a slice could be empty is not reasonable.
English

@__phantomderp @strega_nil @DrawsMiguel Fixing NULL + 0 would also be good. Both it and the memcpy(NULL, 0) language bug affected real world code in BoringSSL. If you have a function that takes ptr,len, NULL,0 is the natural way to say empty slice. But C is full of unnecessary places that break when you do that.
English

@RichSalz Well, AES is still significant progress. For GHASH, BearSSL has a writeup of a very neat strategy. I have some code I can contribute there if interested.
English