Daniel Púa
3K posts


Daniel Púa
@devploit
Security Researcher · Head of Security @Magnific · CTF Player 🇪🇸 · @hackandbeers Málaga · Real-world infosec, no hype.
Málaga, Spain Katılım Nisan 2016
906 Takip Edilen3K Takipçiler

References:
- github.com/vercel/next.js…
- github.com/dwisiswant0/ne…
English

Mitigation if you can't patch yet: switch unnamed captures ($1) to named ones (?<name>...). Sidesteps the buggy path entirely.
Quick audit: grep -RnE 'rewrite[[:space:]].*\$[0-9].*\?' /etc/nginx
github.com/DepthFirstDisc…
nvd.nist.gov/vuln/detail/CV…

English

Unless I see something to change my mind, I still think the same.
Brian Roemmele@BrianRoemmele
“Anthropic's bug-hunting Mythos was greatest marketing stunt ever, says cURL creator” Not someone random…
English
Daniel Púa retweetledi

Daniel Púa retweetledi

🚫 NoMore403 — HTTP 401/403 Bypass Testing Tool
A powerful CLI tool for finding access-control bypasses, parser inconsistencies & proxy/WAF misconfigurations.
⚡ Tests 403/401 bypass techniques automatically
⚡ Header, path, method & raw HTTP mutations
⚡ Detects frontend/backend parsing differences
⚡ Auto-calibration to reduce false positives
⚡ Replayable curl evidence for findings
⚡ JSON/JSONL support for pipelines
Built for bug bounty hunters, pentesters & web security researchers.
github.com/devploit/nomor…
#BugBounty #Pentesting #WebSecurity #CyberSecurity #AppSec
English

Just got a CVE assigned: CVE-2026-6379
Found an unauthenticated SQL injection in WP Photo Album Plus (< 9.1.11.001). CVSS 8.6 Pre-auth, no creds needed. Verified by @_WPScan_.
Patch is out, update now.
wpscan.com/vulnerability/…
English
Daniel Púa retweetledi

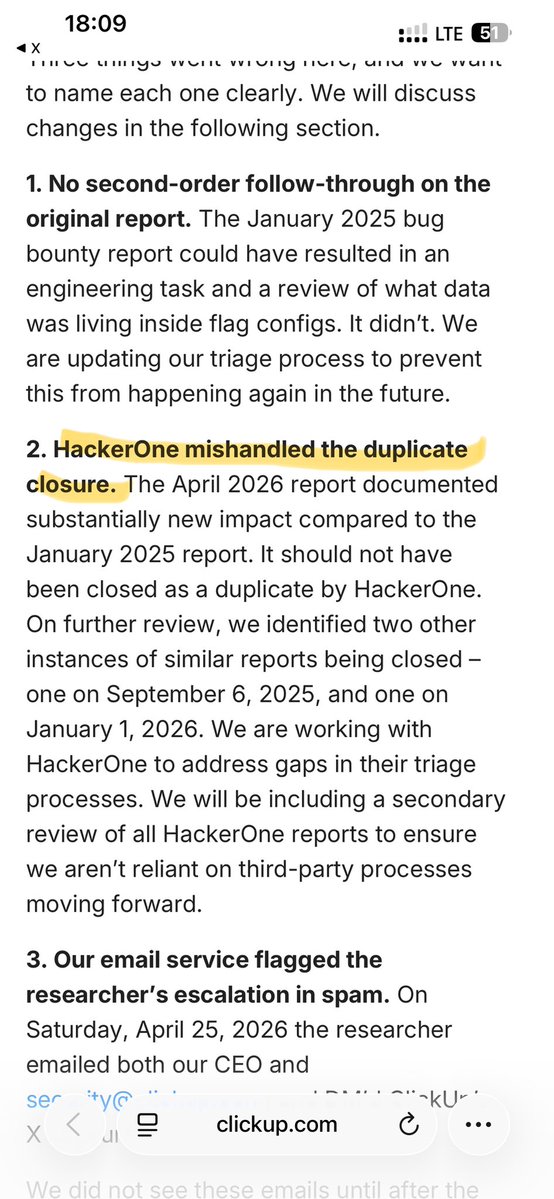
HackerOne just got a company breached.
ClickUp's April 27th data leak? Directly caused by HackerOne's triage failure.
They closed a critical report (893 exposed emails + a live API token) as a "duplicate" twice.
Their AI or analysts auto-close valid findings as "informative" while real vulnerabilities fester.
This wasn't a one-off. HackerOne did it to ClickUp at least three times.
If you run a bug bounty on HackerOne, your security is in the hands of broken triage.
Don't wait for a public shaming to find out they buried your next breach.
Ditch HackerOne.
clickup.com/blog/april-27t…
English
Daniel Púa retweetledi
Daniel Púa retweetledi

⚠️ El "313 Team" tiene Ubuntu.com fuera de servicio con un DDoS y un intento de extorsión a Canonical.
A la vez, circula un exploit público de Copy Fail: 732 bytes de Python para conseguir root en casi cualquier Linux.
Sin repos no hay parche. Y el reloj corre.
Español
Daniel Púa retweetledi

Freepik is now @Magnific
Walking away from a name millions trust is not something you do lightly
I wrote about why we did it
English