/dev/ttyS0
1.9K posts

/dev/ttyS0
@devttyS0
Embedded hacking courses: https://t.co/OgxN50zWNV
Katılım Aralık 2010
107 Takip Edilen7.7K Takipçiler
/dev/ttyS0 retweetledi
/dev/ttyS0 retweetledi

Had a blast doing this podcast!!
The Amp Hour Podcast@TheAmpHour
@nmatt0 is a hardware and #IoT security researcher. He joins Chris to talk about best practices for securing hardware that talks to the internet and share stories of products that didn't pass muster. theamphour.com/698-hardware-s…
English
/dev/ttyS0 retweetledi

Discovered internal Google files inside the sandbox.
Extracted a 579MB binary too big to just print out.
Used Binwalk to unpack it and found… source code.
linkedin.com/posts/kislayy_…
English
/dev/ttyS0 retweetledi
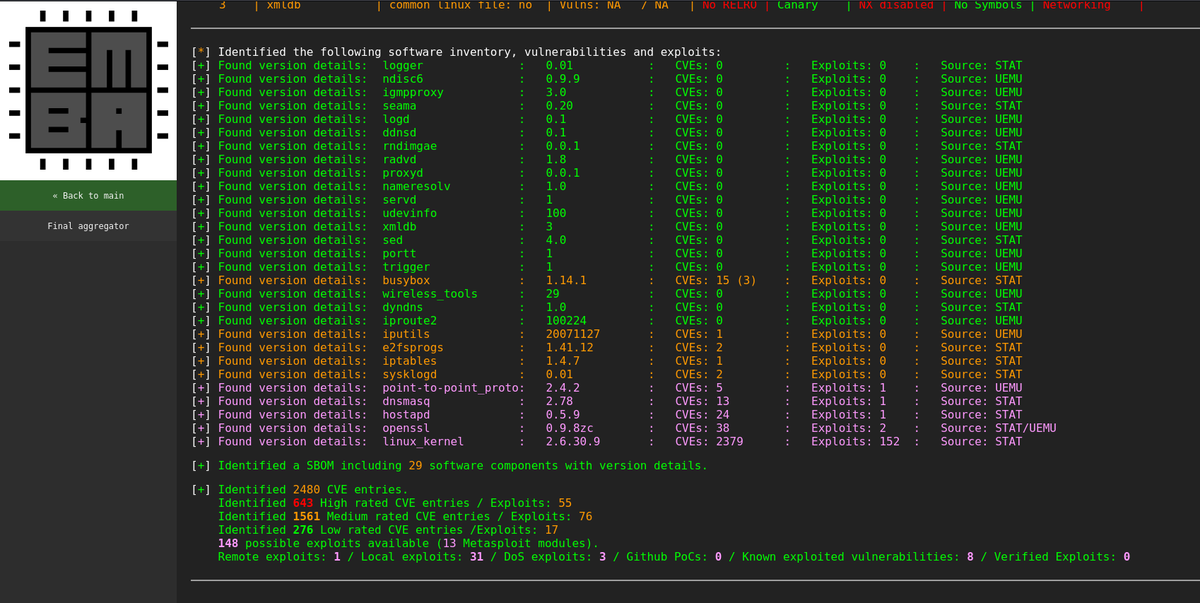
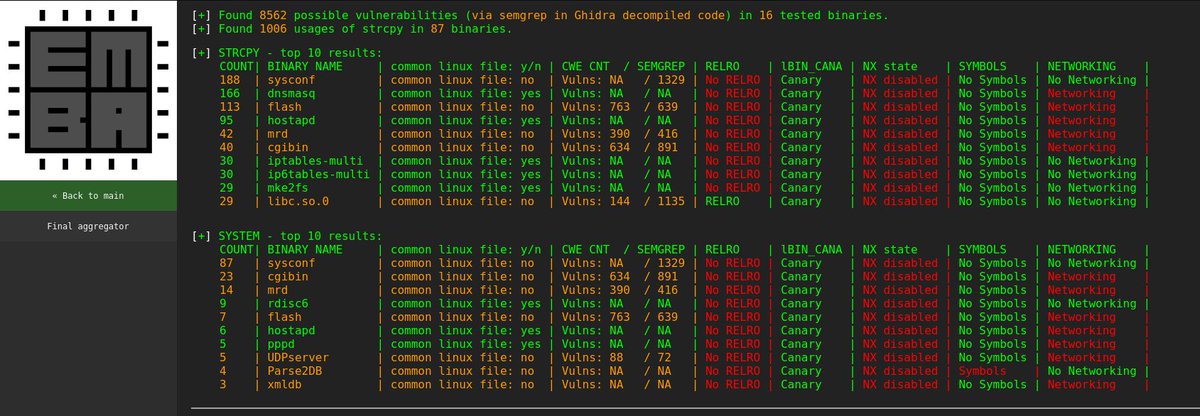
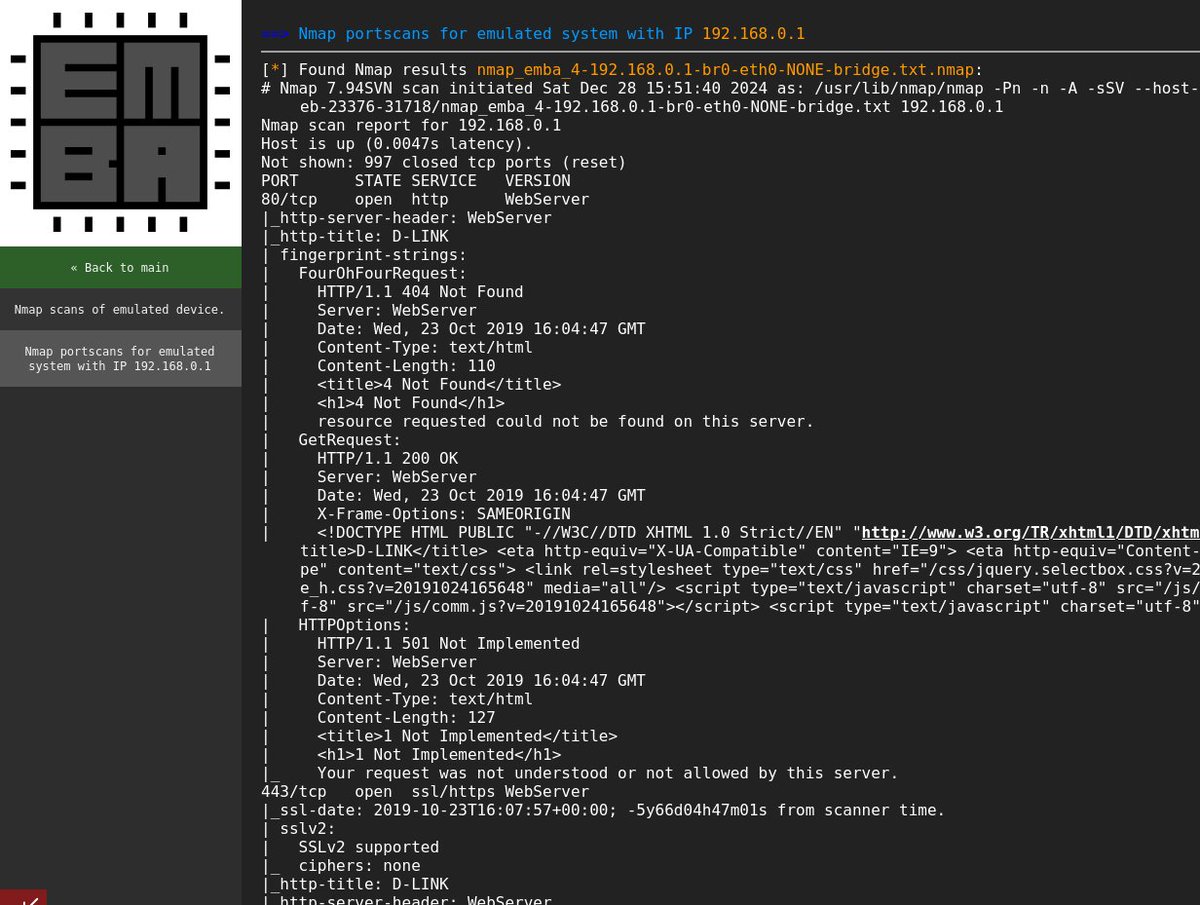
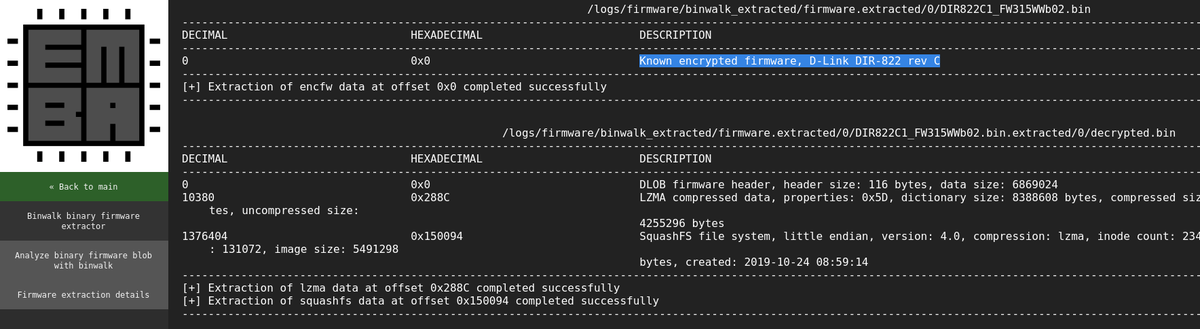
Just in time for a happy new year with better firmware analysis. Now with the enhanced binwalk decryptor available in EMBA. SBOM, known vulnerabilities, static analysis, emulation and much more (Screenshots from DIR-822 Rev C) github.com/e-m-b-a/emba
/dev/ttyS0@devttyS0
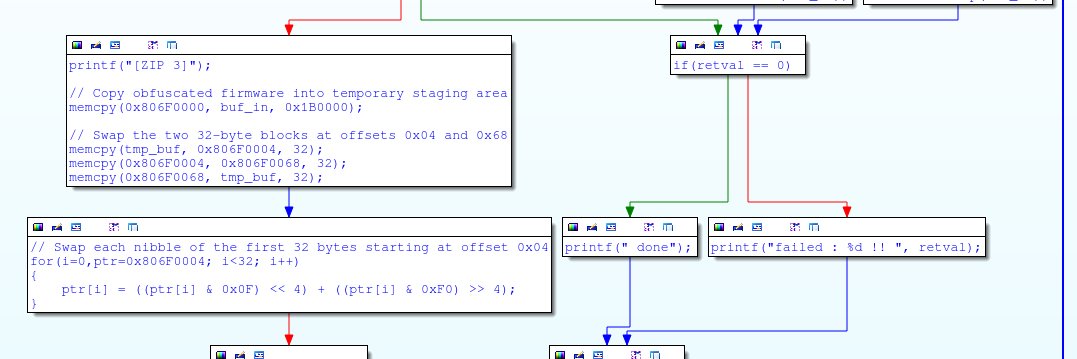
Just in time for Christmas: a repository for decrypting many encrypted D-Link firmware images. Also integrated into Binwalk for auto-magic decryption & extraction. github.com/devttys0/delink
English

@pravda79 Binwalk definitely *should* handle those. Bug reports are always welcome, if you can provide a sample firmware image or link (either here or on the github page) I can take a look. Thanks!
English

@devttyS0 When I did RE work on D-Link devices some time ago, binwalk had multiples issues extracting things from the firmware file like SquashFS file systems, some certificates, etc - that is what I meant with binary blobs. I'll keep your repo for reference in the future, thanks
English

Just in time for Christmas: a repository for decrypting many encrypted D-Link firmware images. Also integrated into Binwalk for auto-magic decryption & extraction.
github.com/devttys0/delink
English

@GM4AJK I did, though I haven’t posted content there in some time now
English

@pravda79 lol that’s the main purpose of binwalk, what binary blob(s) are you referring to? unblob is good, it does some things binwalk doesn’t (and ice-versa), I keep both tools installed on my system for RE work.
English
/dev/ttyS0 retweetledi
EMBA release alert with version 1.5.1 - Rise from the dead or Binwalk is back in town.
We have a big update for all you #SBOM/#IoT/#firmware and binary analysis people out there.
EMBA is getting faster and more powerful with new binwalk v3 and more SBOM github.com/e-m-b-a/emba/r…
English

@nmatt0 Nice work! :) FYI, Binwalk disables text formatting when it's not outputting to a terminal, so piping the output to `tee -` might help when using large terminal fonts for your videos.
English
/dev/ttyS0 retweetledi
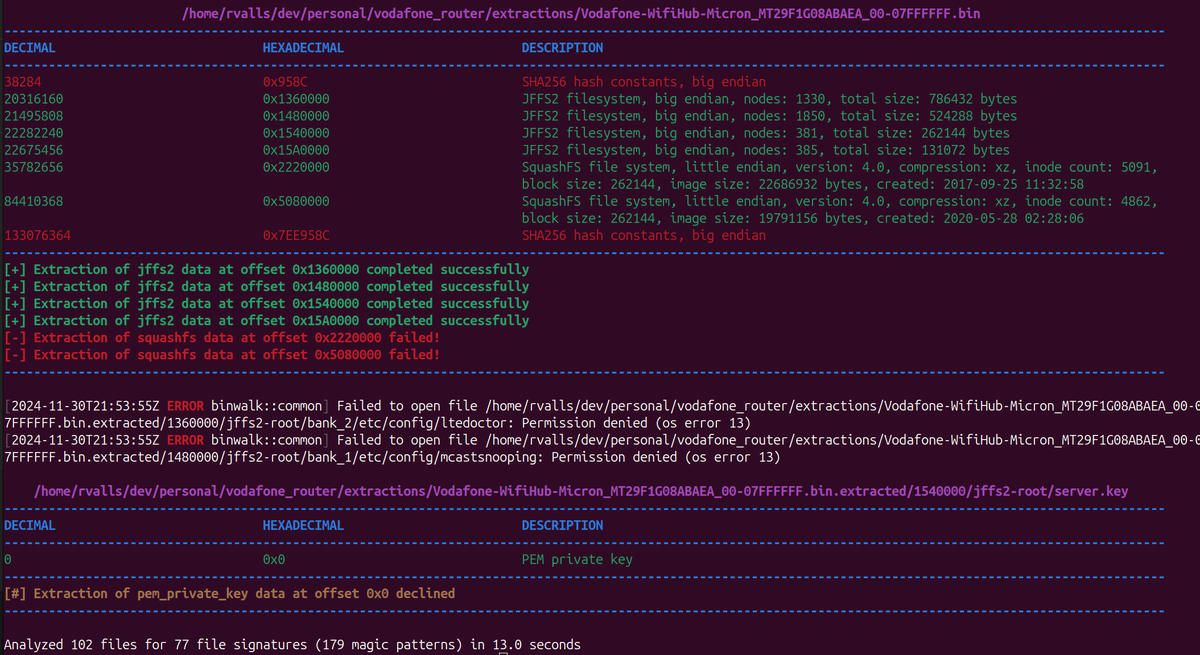
making progress ... say hi to all new binwalk in EMBA

EMBA Firmware Analyzer@securefirmware
Looks as it is time to start with some binwalk v3 integration into EMBA. First run is binwalk v2, 2nd run is v3 ... great work @devttyS0
English

@braincode Interesting, carving out the SquashFS images and running unsquashfs manually provides a partial extraction, but encounters a decompression failure part-way through.
English
@devttyS0 NAND indeed (Micron MT29F1G0), here's the output from binwalk_v3 (git clone fresh from today) and also the dumped flash if you are curious: #wQHG_cidg3rXzM6qvC71Dsa-ksIU7YOtplsmkXRNuRc" target="_blank" rel="nofollow noopener">mega.nz/file/65xDmYZC#…
English

@braincode I don't, but maybe I should create one. :) Interesting about the SquashFS image, was the flash chip NAND perchance? Could be an issue with OOB/spare data in the raw flash dump.
English
@devttyS0 Also, do you have some "bins" repository to share BLOBs? I recently dumped a TSOP flash firmware that has weird squashfs sections, not handled well by binwalk-v3 (sasquatch)...
English
/dev/ttyS0 retweetledi
/dev/ttyS0 retweetledi

@rawz0ne openssl expects the input file to start with "Salted__"; the firmware itself has a 0x41 byte header, which has to be removed first. I haven't tested E15A1_FW120B01_revise.bin, but confirmed to work with E15A1_FW120B01.bin.
English

@sundhaug92 That one was a bit trickier than the others. Required hardware access + an exploit to pop a root shell. :)
English