dirty0124
3K posts


dirty0124
@dirtycoder0124
A positive, never give up person. Founder of https://t.co/2H0KjZ5riG Telegram group https://t.co/bjQUMjI9Lh
India Katılım Ekim 2015
423 Takip Edilen4.5K Takipçiler
dirty0124 retweetledi
dirty0124 retweetledi

1600+ regex patterns for detecting secrets, API keys, tokens, and passwords. 💀🔥
This open-source database can directly improve your secret scanning pipelines (TruffleHog, Gitleaks, etc.).
If you're doing AppSec seriously, this is worth integrating.
github.com/mazen160/secre…
#AppSec #CyberSecurity #Infosec
English

dirty0124 retweetledi

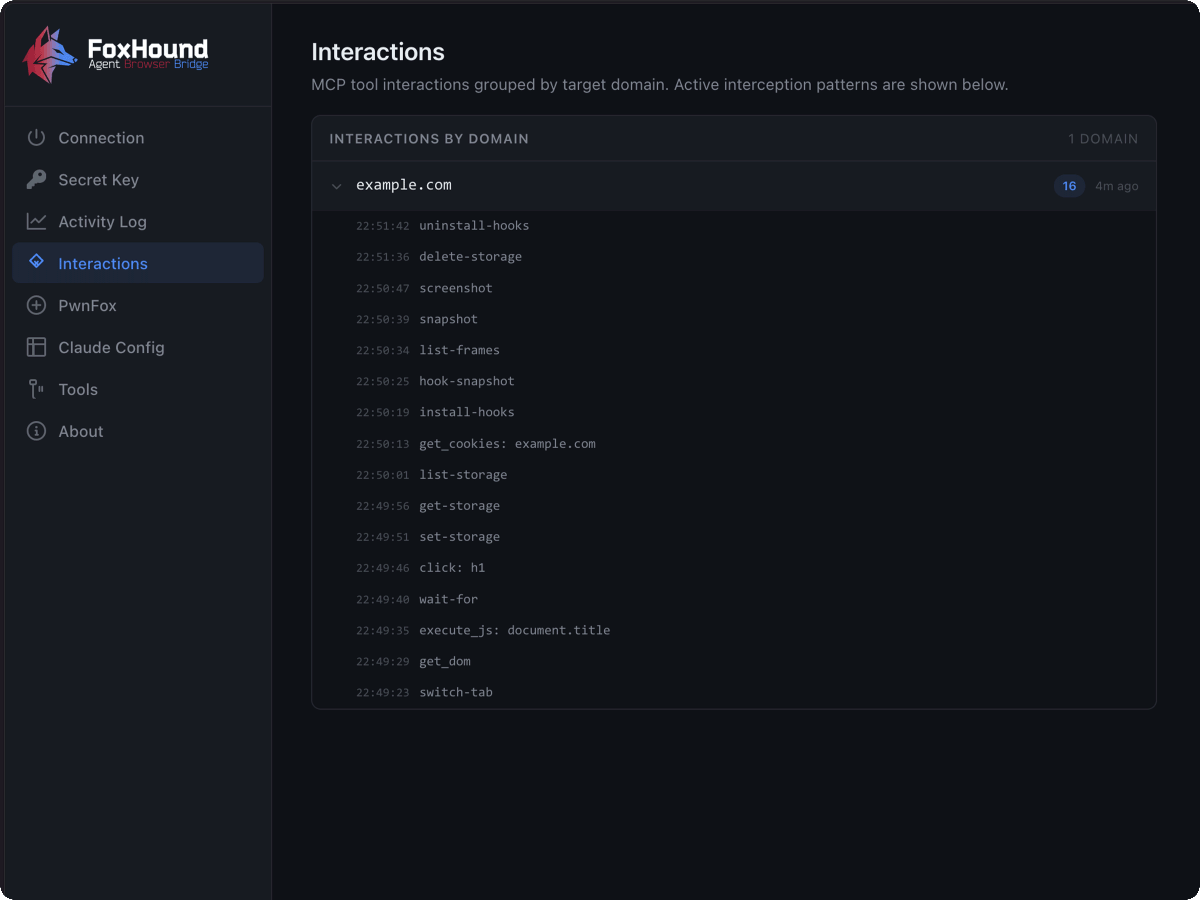
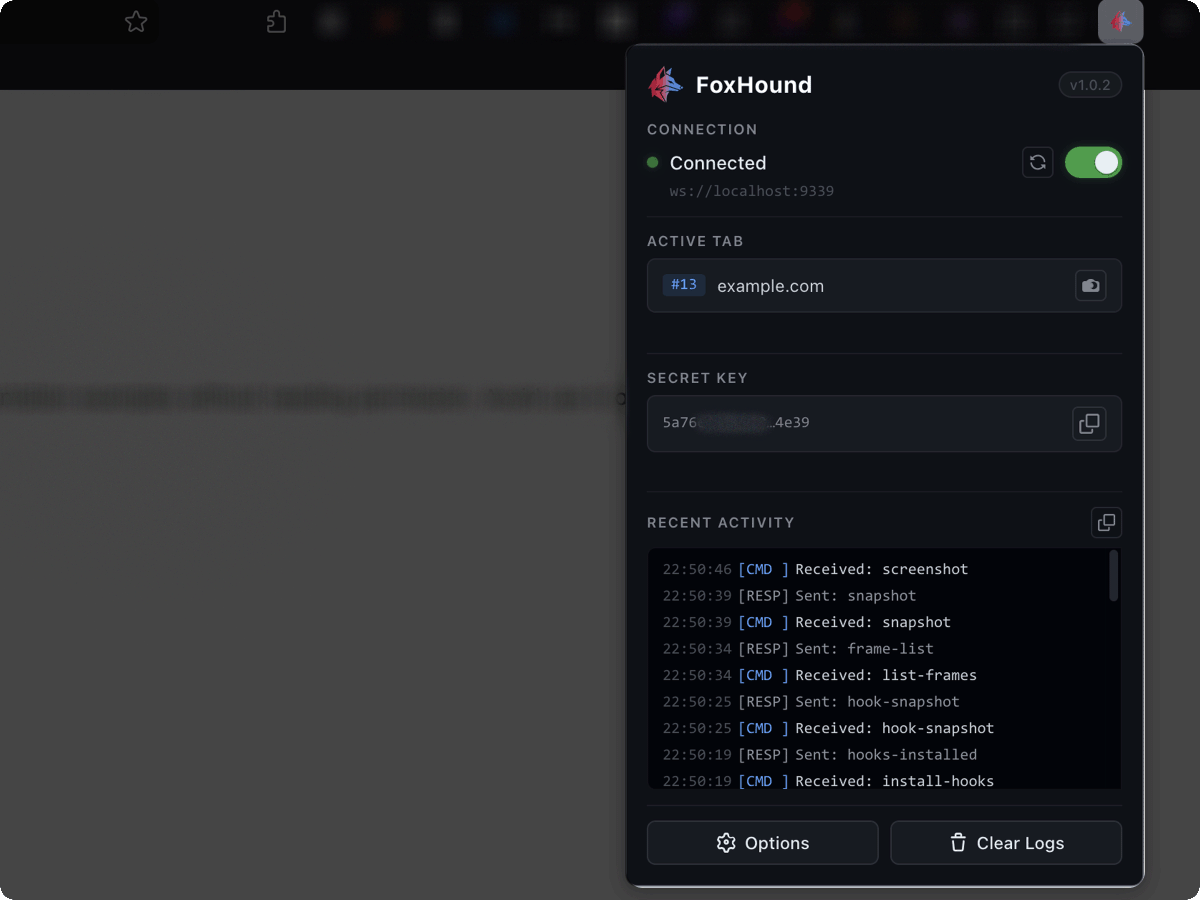
I built FoxHound, a Firefox extension that gives any AI agent full control over your browser.
I needed this while hunting. There are bugs the egent can not properly exploit without using the browser. Clicking things, reading the DOM, replaying requests, checking cookies across containers, running JS on the page. So i built it.
The agent can navigate tabs, click elements, fill and submit forms, upload files, take screenshots, capture all HTTP traffic with full request and response bodies, replay and modify requests, read and write cookies and storage, intercept live requests, hook into postMessage traffic, WebSocket connections, route changes, console output, service workers, and more.
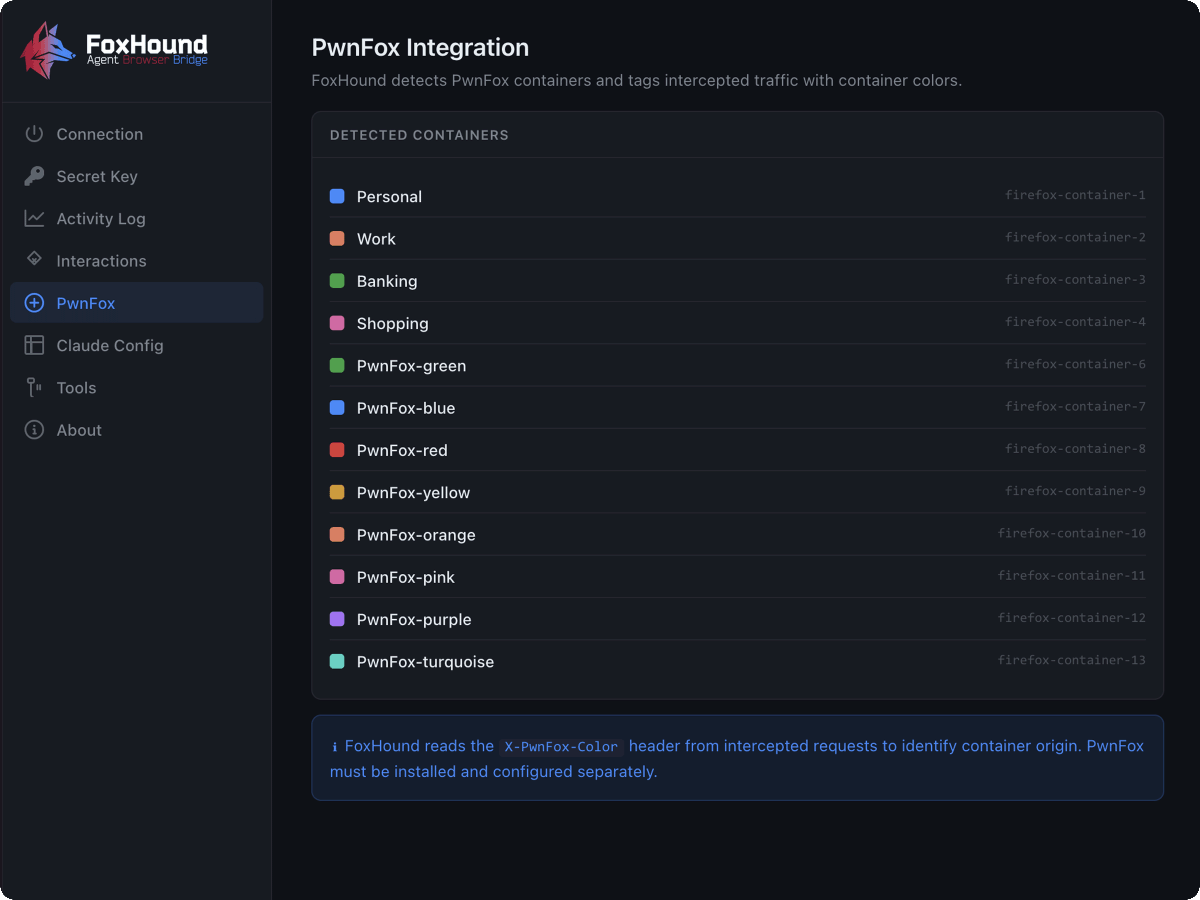
It also uses PwnFox containers so the agent knows which container each request came from. If you are doing multi account testing, everything stays separated.
Setup takes 2 minutes:
1. Install the extension: addons.mozilla.org/firefox/addon/…
2. Run: npm install -g foxhound-mcp
3. Copy the config from the extension options page into your MCP client. Done.
It is free. Give it a try and if you find any issues or want to add anything, open an issue on the GitHub: github.com/amrelsagaei/fo…

English
dirty0124 retweetledi

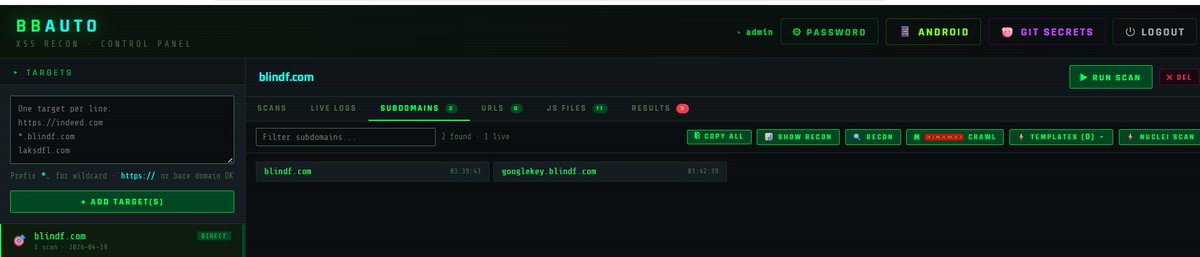
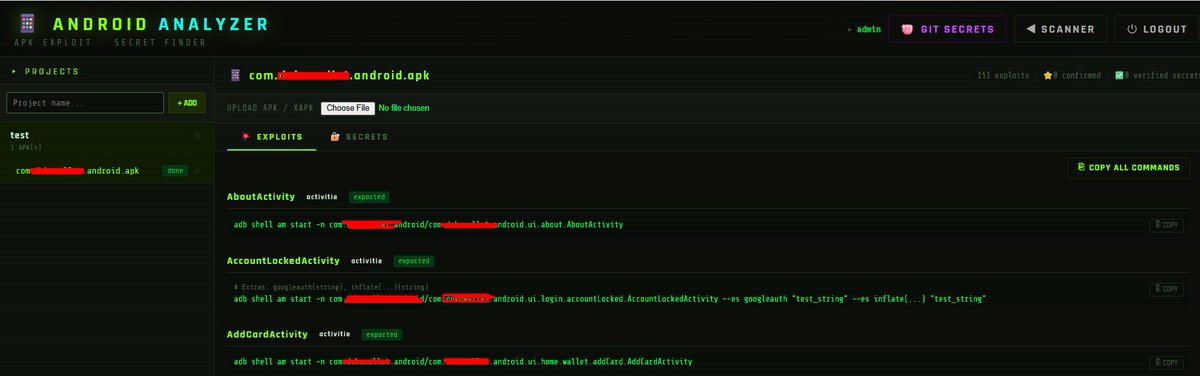
lots of people asked me for my recon methodology
HYG:
github.com/nullthrix/BugB…
soon will publish my full WAP methodology...
#BugBounty #hacking #security #hackerone #bugcrowd #integrity #yeswehack
English

Dropped a critical idor bug on main api of a @yeswehack program, but it got marked as info with a strange justification - api is ours but bug is not.
what’s more surprising: the issue was quietly patched, and there’s been zero response to the support ticket I raised 👏
English
dirty0124 retweetledi

Autonomous bug-bounty framework for Claude Code — 40 specialist agents, exploit-chain builder, writeup search, and live HackerOne/Bugcrowd integration. github.com/H-mmer/pentest…
English


dorkking.blindf.com/bugcrowd-vrt-r…
Bugcrowd Vrt simplified. I hope it will help the beginners. #bugbountytips

English
dirty0124 retweetledi


Drop subdomains in
Get Gemini-enabled API keys out.
Automates HTML + JS crawling & AI access testing.
Bug hunters — this one’s for you 🔥
github.com/dirtycoder0124…
Thanks to @trufflesecurity
#BugBounty #bugbountytips
Automation of
trufflesecurity.com/blog/google-ap…
English
dirty0124 retweetledi

0xJS is an AI-powered JS security tool;
- it can identify API keys, and other medium to critical severity secrets with high accuracy.
- also scans for potential security issues in JS i.e DOM-XSS, postMessage, URL redirect. e..t..c
- e..t..c; 0xJS v4.0 ( github.com/4osp3l/0xJS )
English
dirty0124 retweetledi

I just published a video demonstrating how a token scope misconfiguration can silently lead to privilege escalation, where a normal user login becomes an admin-capable session due to improper scope validation.
youtu.be/Shv84wdyqlg?si…

YouTube
English
dirty0124 retweetledi

🐞If you hunt modern web apps, this guide is worth your time.
A deep dive into Next.js security testing covering real attack surfaces — SSRF, XSS, CSTI/SSTI, cache issues, data leaks, and more — with a mindset tailored for bug hunters and pentesters.
Frameworks evolve fast, and so do their flaws.
Understanding how Next.js handles rendering, routing, APIs, and caching can open doors to impactful findings.
Great work by @daoud_youssef — definitely adding this to my testing workflow.
🔥deepstrike.io/blog/nextjs-se…
#BugBounty #AppSec #WebSecurity #Pentesting #NextJS #CyberSecurity #SecurityResearch
English
dirty0124 retweetledi

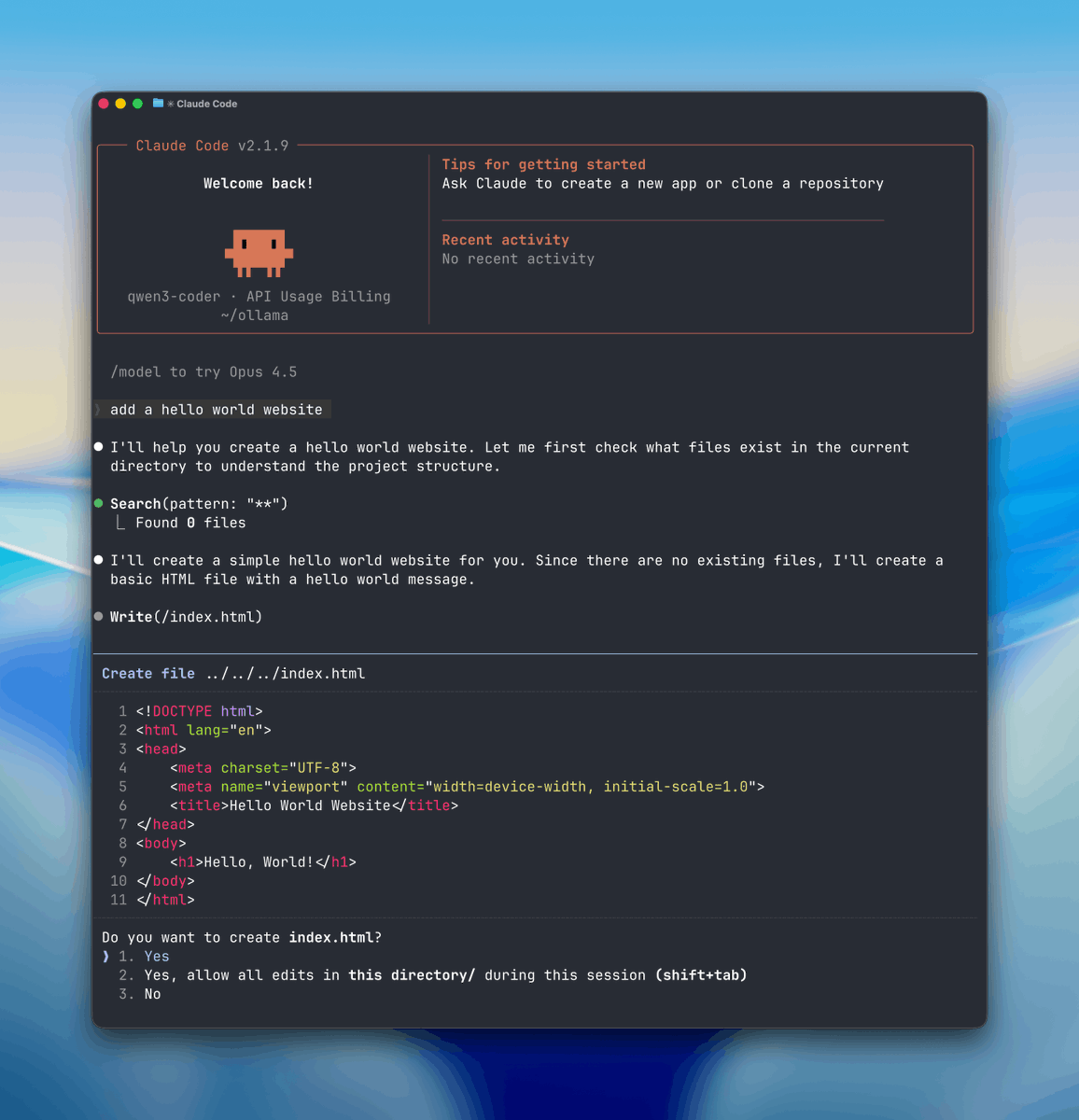
Claude Code costs $17/month and runs out in 2-4 tasks. The $200/month plan? That's rent money.
Here's how I vibe code for FREE with generous limits. Every method is legal and working right now:
The thing most people don't understand
Claude Code is just a terminal agent. The intelligence comes from the model behind it. And comparable models exist — for free.
What you actually need: an open-source agent + a free hosted model. That's it.
Method 1: Aider + Nvidia (the best one)
Aider is an open-source terminal agent that does exactly what Claude Code does. 30K+ GitHub stars, 15B tokens/week processed, built by Paul Gauthier. This isn't some random weekend project.
Setup in 3 steps:
1. Install UV: curl -LsSf astral.sh/uv/install.sh | sh
2. Install Aider: uv tool install aider-chat
3. Go to build.nvidia.com → pick a model (Kimi K2.5 or DeepSeek R1 recommended) → generate a free API key
Export the key, run Aider with the Nvidia model, and you have a Claude Code clone. Free. 40 requests/minute, no monthly quota. It initializes Git repos, builds full apps, maps your entire codebase, auto-commits with sensible messages — everything.
I've been using this daily for side projects. The quality gap with Claude? Smaller than you think.
Method 2: Hackathon credits (up to $100K)
Cerebral Valley hackathon gives up to 100,000 Claude Code credits. Not a typo.
Anthropic runs these regularly. Sign up, participate, walk away with months of free usage. Even if you don't win, sponsors hand out API credits like candy.
Method 3: Alternative platforms
• OpenHands — fully open-source coding agent
• OpenCode — solid Claude Code alternative
• Cursor free tier — not terminal-based, but decent for assisted coding in VS Code
• Copilot free tier — 2000 completions/month on GitHub
Aider remains my go-to for the closest Claude Code experience.
⚠️ The security warning nobody gives you
These models run on third-party servers. NEVER feed them:
• SSH keys
• API tokens
• .env files
• Production credentials
For personal projects and learning? Perfect.
For production with secrets? Stay on paid solutions.
This isn't paranoia. A Firebase misconfiguration just leaked 300M conversations from an AI chat app this week. Free doesn't mean careless.
My actual setup
• Daily coding: Aider + free Nvidia models (95% of my work)
• Critical production: Claude Code with Opus (when I need frontier reasoning)
• The rule: if it touches real user data or credentials → paid. Everything else → free.
Monthly savings: ~$180.
The $0 vibe coding starter kit
1. Install UV + Aider (2 minutes)
2. Get free Nvidia API key (1 minute)
3. Clone a repo, run aider, start building
4. Graduate to paid only when you genuinely need it
You have zero excuses not to code with AI in 2026. The tools are free. The models are good enough. The only cost is your time learning the workflow.
Stop paying rent to Anthropic for side projects.
#ClaudeCode #FreeCoding #VibeCoding #AI
English
dirty0124 retweetledi
dirty0124 retweetledi

HTTP Headers Every Hacker Should Know (Bypass Techniques)
Tags: #BugBounty #WebSecurity #EthicalHacking #http_header

English