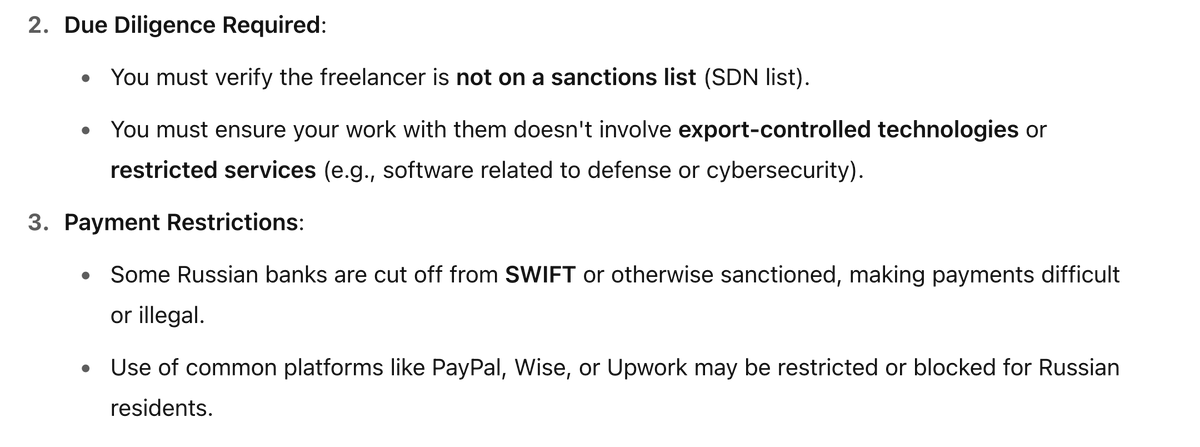
@BuildHackSecure @MiniMjStar @GodfatherOrwa @Hacker0x01 @h4x0r_dz ChatGPT says basically the same. There are restrictions against some individuals and some organisations (GPT mentioned banks).
If you are not one of the sanctioned individuals and are not trying to get paid via the sanctioned bank — then legally you are ok.
English