DON STEVE
1.8K posts

DON STEVE
@donsteve__
Documenting my journey into Cybersecurity & Ethical Hacking Sharing lessons, tools & beginner insights Follow along as I grow



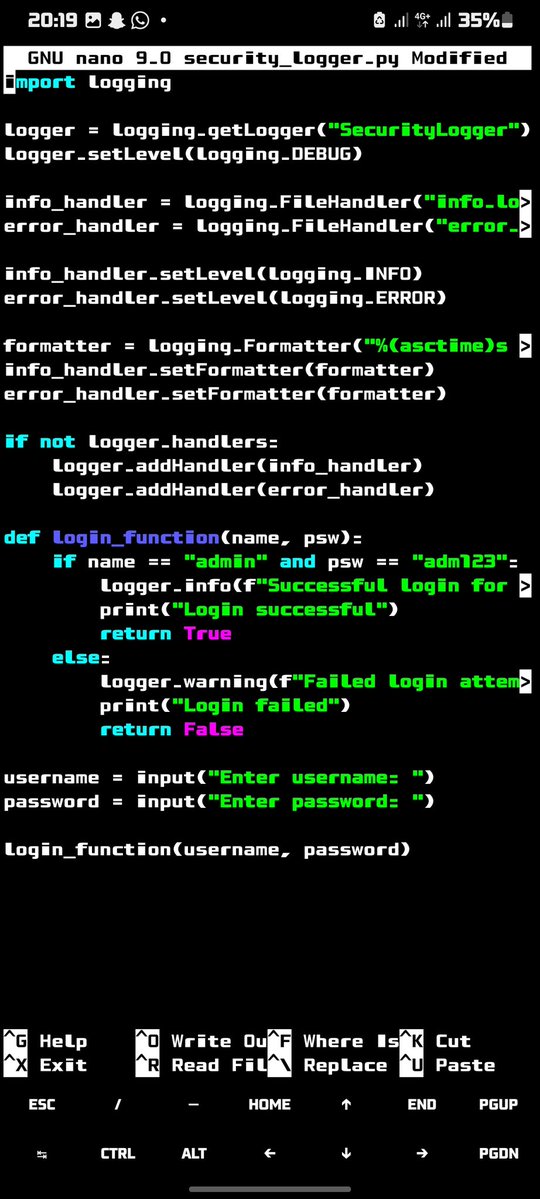
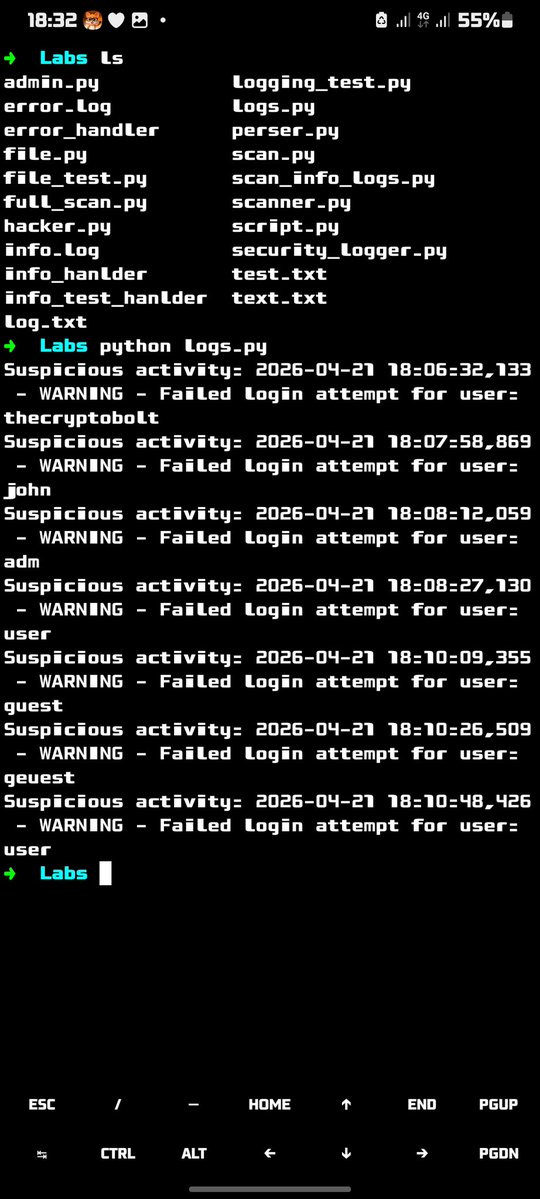

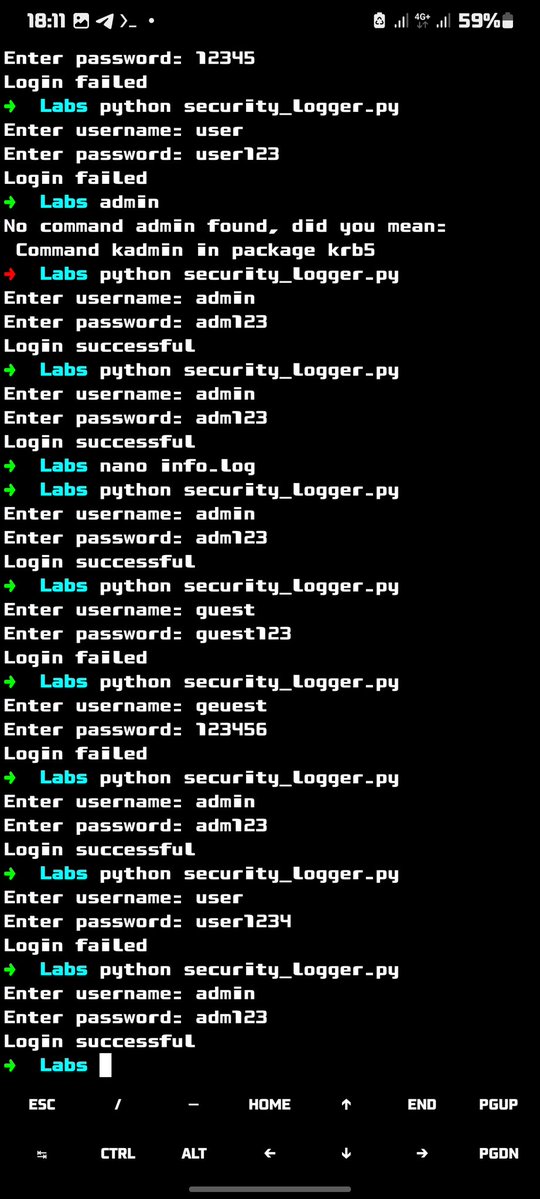
Day 19 of Python for Cybersecurity Today I took something I had already built, a simple login script and started shaping how it behaves under pressure. At first, every failed login looked the same. Just a wrong password message. But then I added structure with Python’s logging module, and things started to feel different. A single failed attempt became a warning… and repeated failures slowly escalated into a critical alert. Same input, same function but now the system starts to react based on patterns, not just events. I also wired it to files using file handlers, so everything gets recorded quietly in the background. One file tracks normal activity, another keeps the serious stuff. From a cybersecurity perspective, this is where things start to matter: — You begin to see how systems detect suspicious behavior — You understand how small actions can escalate into alerts — And you start thinking like the system, not just the user Still early in the journey, but this felt like one of those moments where code stops being just code… and starts acting like a real security system ⚡