
unreal
38 posts
















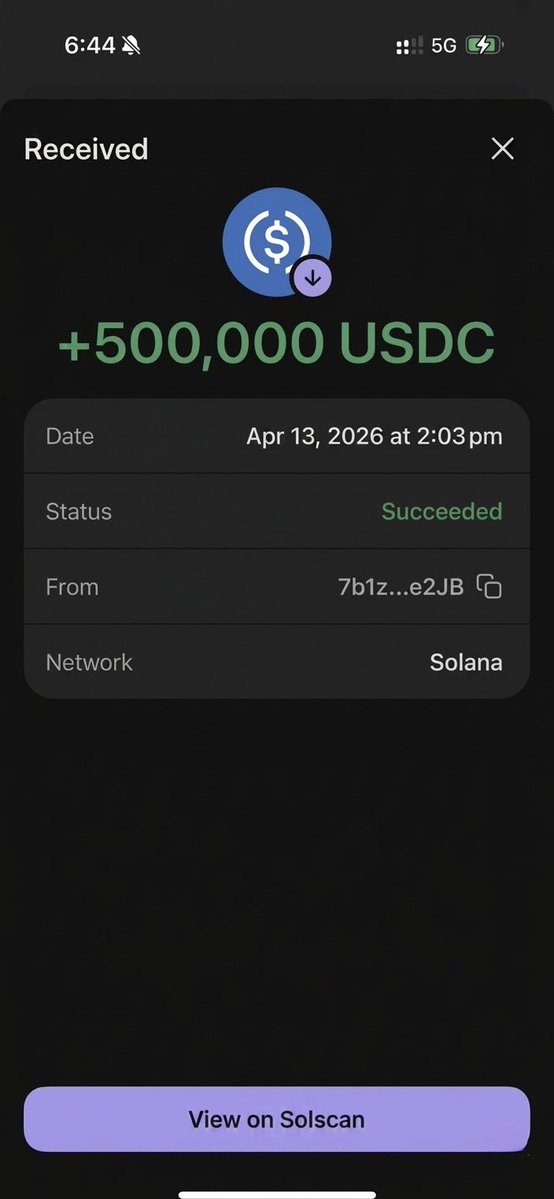
We've identified an address poisoning attack targeting Squads users. We have no evidence of any users being impacted at this time. Attack vector: Since all public keys are visible onchain, attackers are programmatically creating new multisig accounts that include existing Squads users as members. These multisigs appear in the UI because the program indexes all accounts associated with your key. Additionally, attackers are grinding public keys that match the first and last characters of your real multisig addresses, making fake accounts look legitimate at a glance. Attacker goal: Get you to mistake a fake multisig for one of your real ones — either by copying its vault address (sending funds to an attacker-controlled account) or by signing a transaction you didn't initiate. Impact: None, if you don't interact. This is not a protocol vulnerability. The attacker cannot access your funds, execute transactions, or modify your existing multisigs. It is purely a UI-level social engineering attempt. Action required: — Ignore and do not interact with any multisig you did not create or weren't added to by your team — Do not rely on matching the first and last characters of an address to verify it — always verify the full address against your own records — If you're unsure whether a multisig is legitimate, check with your team before taking any action — Set your Squads accounts as default — this pins them to the top of your Squad list, making it easy to distinguish your real accounts from anything unfamiliar. We encourage everyone to do this now if you haven't already (click on ... next to your Squad in the Squad list). UI updates shipping in the next two hours: — A banner alerting users to this attack — An alert on any multisig you've never interacted with before In the next few days we are also shipping a whitelist logic where all new multisig accounts initially go to a pending state requiring you to manually add them to your Squad list. We'll follow up here with updates as we roll these out.




















