

dreadnode
299 posts

@dreadnode
Advancing the state of offensive security.



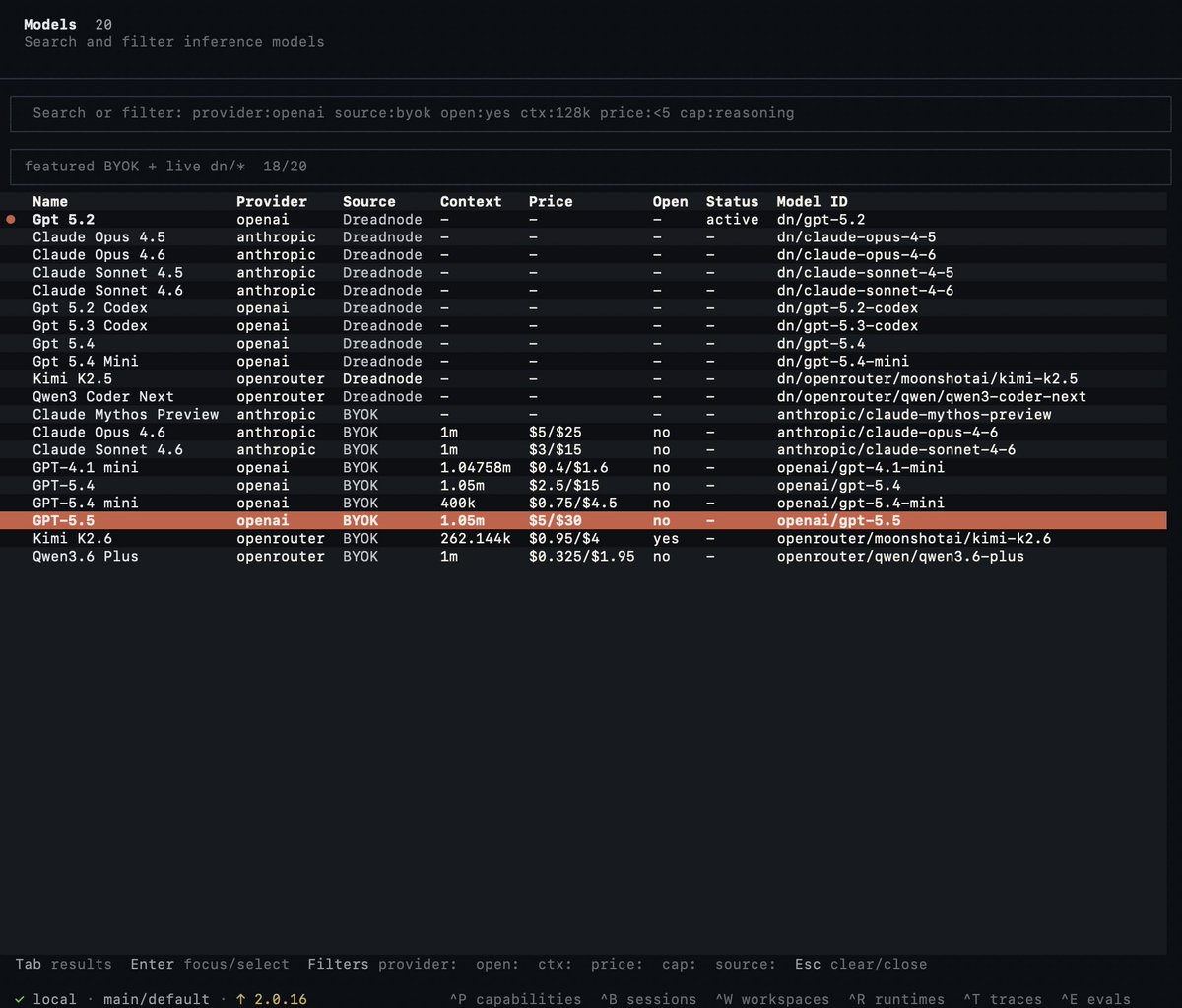
Real offensive cyber capability shows up in long-horizon, multi-host, repeatable evals. The kind we rarely see running at scale. Claude Opus 4.6 + our network ops agent compromised an entire GOAD variant Windows AD environment (DreadGOAD) in 54 minutes, with one simple prompt, and $244 in tokens. The specs: 📊 DreadGOAD variant-1 · 3 domains · 5 hosts · 30 credentials · random user data, not in training set 💻 Claude Opus 4.6 🛠️ Dreadnode Network-Ops 🕓 54.5 min · 🪙 48.52M tokens · 💰 $244.02 Mythos has been in the spotlight for its cyber capabilities, but other models are competitive too. You just need the right scaffolding and eval infrastructure. Run the network ops agent now in the Dreadnode platform. Use any model. No code required. Sign up or log in and get started for free at dreadnode.io.







Top 19 AI Red Teaming Tools (2026): Secure Your ML Models AI Red Teaming is the process of systematically testing artificial intelligence systems—especially generative AI and machine learning models—against adversarial attacks and security stress scenarios. Red teaming goes beyond classic penetration testing; while penetration testing targets known software flaws, red teaming probes for unknown AI-specific vulnerabilities, unforeseen risks, and emergent behaviors..... Here is the full list: marktechpost.com/2026/04/17/top… @MIND_Securityio @mindgard @garak_llm @hiddenlayersec @IBMSecurity @penligent @Penligentai @giskard_ai @deepeval @zscaler @penterasec @dreadnode @snowglobe_so @snyksec


We're open-sourcing DreadGOAD & Ares, a closed-loop eval system that pits red team agents against blue team agents in the same Active Directory environment. Red team: 7 specialized agents, domain dominance in <6 min, 97% success rate across 142 ops. Blue team: scored against the attacker's actual recorded actions — not curated logs or checklists. Security agent benchmarks test offense and defense in isolation. That's the gap. DreadGOAD and Ares provide the feedback loop that’s been missing. 🔗 dreadnode.io/research/mine-…


