Aaron Grattafiori
20.1K posts


Aaron Grattafiori
@dyn___
Offensive Security / AI Red Teaming @ NVIDIA. Ex-GenAI and OffSec Red Teaming Lead at Meta. Ex-Principal Consultant and Researcher @ NCC Group/iSEC Partners.





We have received 6 browser entries for #Pwn2Own Berlin 2026: * Mozilla Firefox renderer: 3 * Apple Safari renderer: 2 * Microsoft Edge renderer + Sandbox escape: 1



Had a similar thing with Opus 4.6 - a macOS SIP bypass that is still under embargo. You still need to monitor a model's output, especially for non-trivial things.

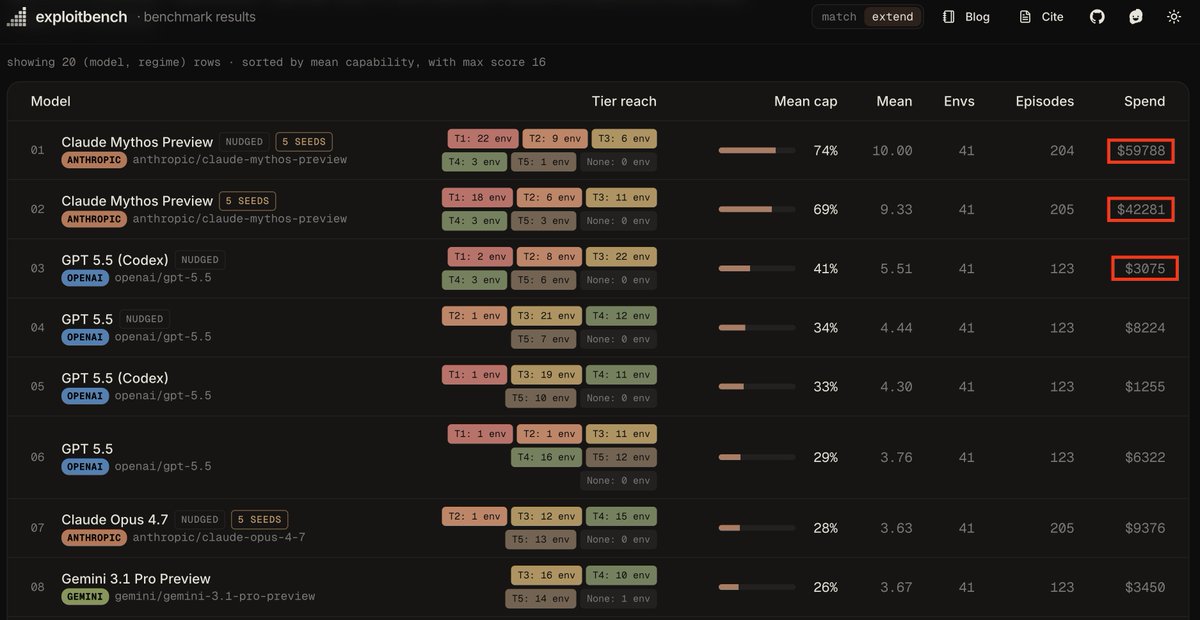
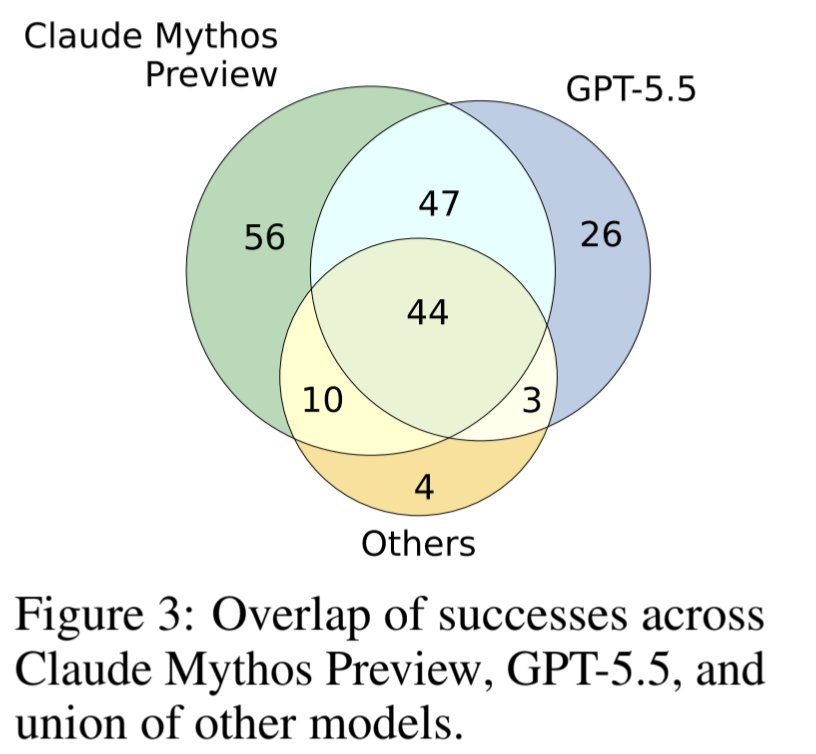
🚨 the "Mythos 69%" headline is misleading GPT-5.5 Codex sits at 41%, looks close. on T1 (full control, the only tier that matters): Mythos: 16 envs GPT-5.5 Codex: 2 Opus 4.7: 0 9x gap, not 1.7x. baseline Mythos (no hints) hits MORE T1s than nudged(hints). it doesn't need help. lead author is David Brumley(picoCTF founder, Bugcrowd CAIO) and @0x10n not benchmark noise.



Aaaand it's official! Orange Tsai (@orange_8361) of DEVCORE Research Team chained 3 bugs to achieve Remote Code Execution as SYSTEM on Microsoft Exchange, earning a whooping $200,000 and 20 Master of Pwn points. Full win! #Pwn2Own #P2OBerlin

today we are releasing a qemu escape

That's my chain — a full chain w/ logic bugs only! No memory corruption, no AI, and of course no collisions at all 😉

Confirmed! Orange Tsai (@orange_8361) of DEVCORE Research Team (@d3vc0r3) chained 4 logic bugs to achieve a sandbox escape on Microsoft Edge, earning $175,000 and 17.5 Master of Pwn points. Full win! #Pwn2Own #P2OBerlin


@daveaitel This is what everyone says until the capability curve of 6 months from now consumes that expert/domain knowledge. The security community should study the bitter lesson and adjust appropriately for whats coming.