Sabitlenmiş Tweet

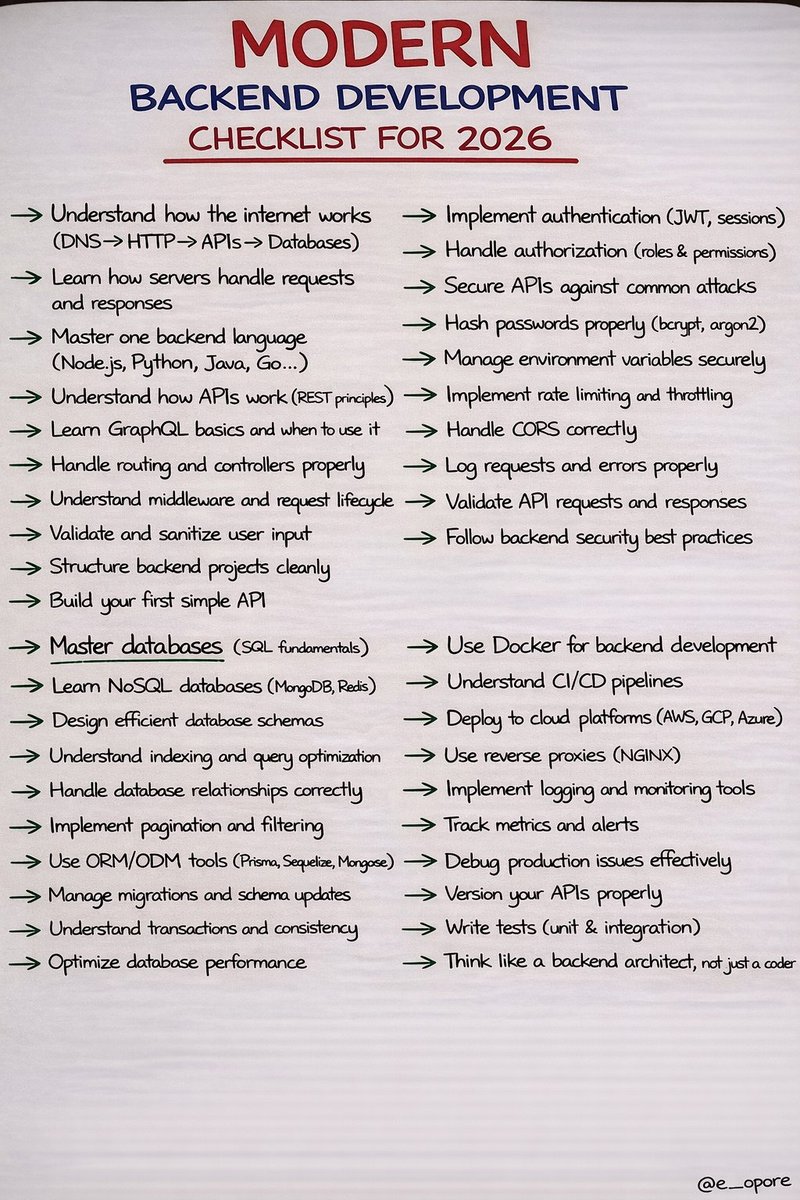
COMPLETE FULL STACK DEVELOPER ROADMAP: MASTERING MODERN DEVELOPMENT IN THE AI ERA (2026) written DAY-BY-DAY (1–365).
Grab the Modern Full Stack Latest Edition Handbook:
codewithdhanian.gumroad.com/l/fzqjct




English
Dhanian 🗯️
60K posts


@e_opore
SoftwareDev. Roadmaps,Cheatsheets, Projects with Source Code & Resources.Learn with me.Coding Ebooks: https://t.co/g835vCPNQA.