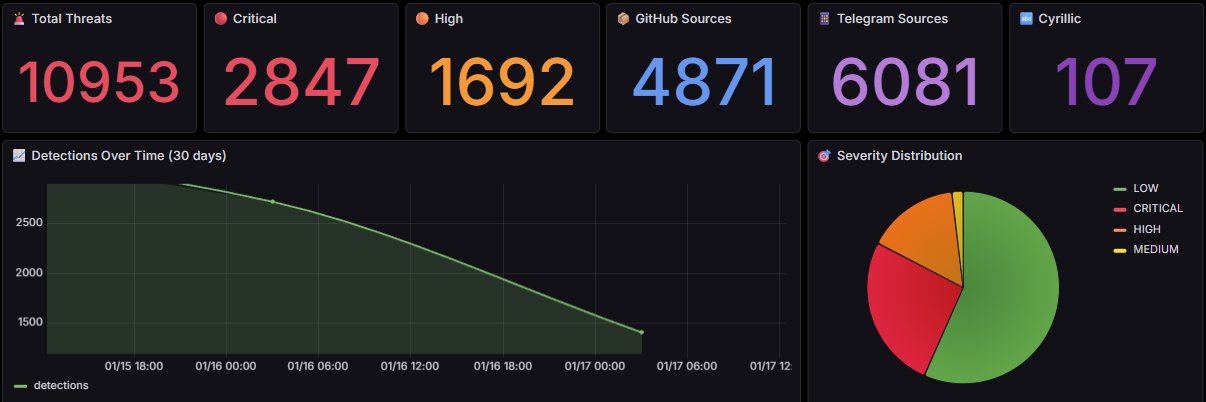
The scale is getting huge. 🔴 Critical Threats: 2,847 📂 Total Database: 10,953 items
See the live war room dashboard here: 🔗 egemenguney.net/hunter_dashboa…
#Infosec #BlueTeam #Automation #Coding

English
Egemen Guney KOC
10 posts

@egemenguney_koc
Cyber Threat Intelligence Architect | Building Autonomous Malware Analysis Pipelines 🛡️ | Python, Playwright & MISP Integration | Hunting 0-days in the wild.