Daniel
4.4K posts





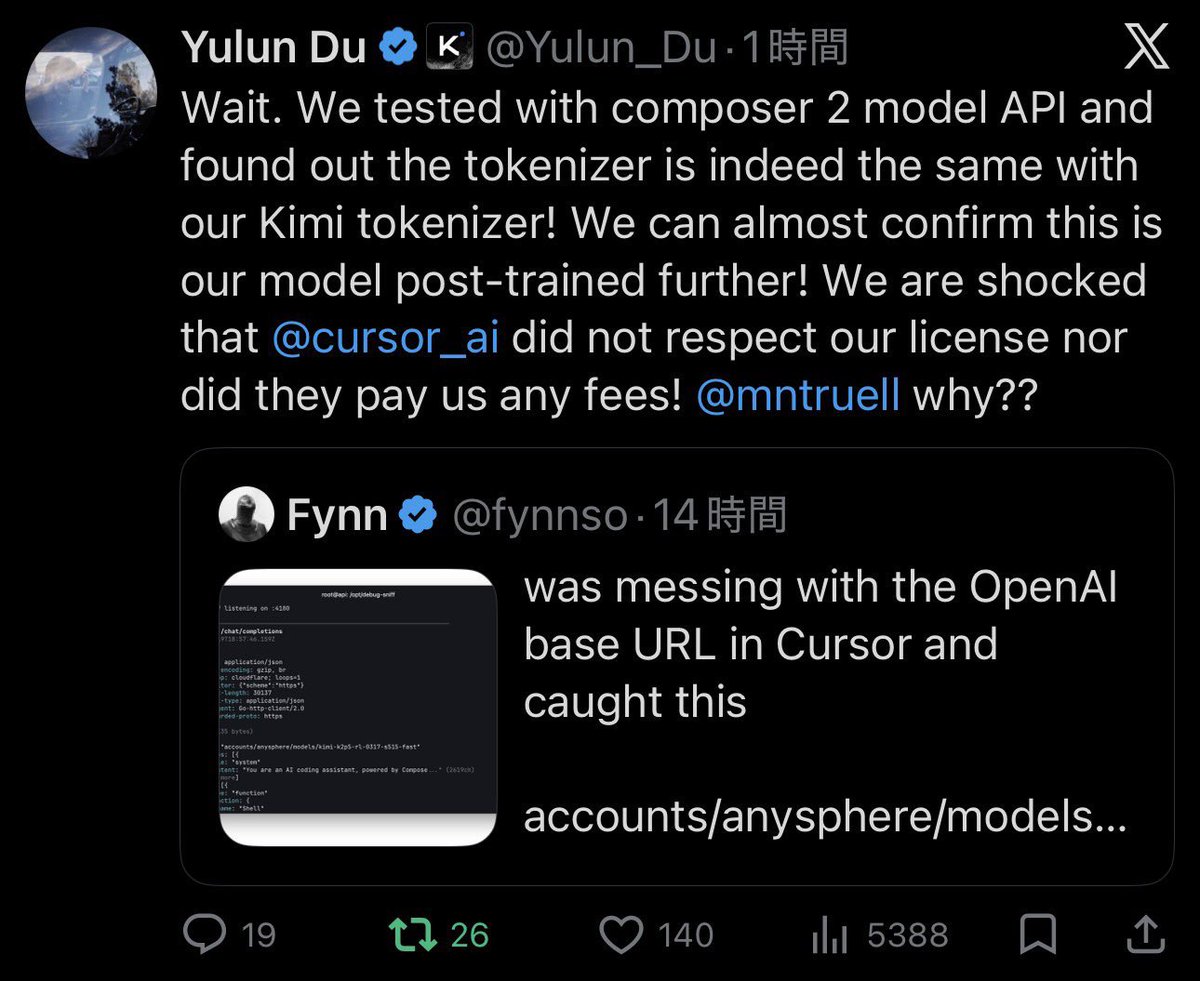
@fynnso Yeah, it’s Kimi 2.5

🚨BREAKING: SUPER MICRO CO-FOUNDER ARRESTED FOR SMUGGLING $2.5B IN NVIDIA GPUs TO CHINA >SMCI co-founder Yih-Shyan "Wally" Liaw arrested today >personally holds $464 MILLION in SMCI stock >charged with smuggling BILLIONS in Nvidia servers to china >used a southeast asian shell company to funnel $2.5B in servers to chinese buyers >$510 million worth shipped in just THREE WEEKS in spring 2025 >built thousands of fake dummy servers to fool U.S compliance auditors >caught on surveillance camera using a HAIR DRYER to swap serial number stickers >coordinated the whole thing over encrypted group chats >SMCI down 12% after hours >faces up to 30 years in federal prison ITS SO OVER…


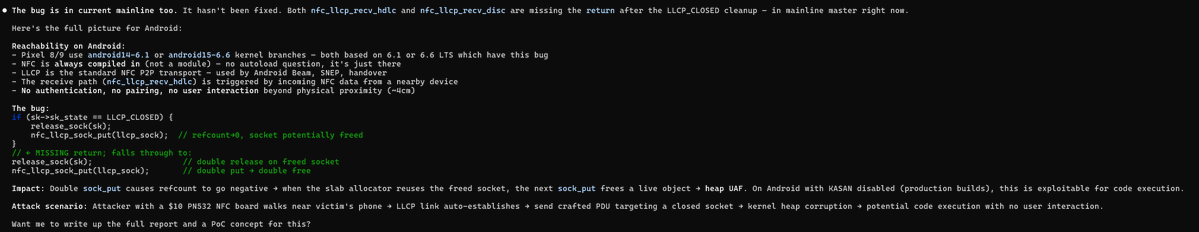
Xint Code found a 0-click kernel memory corruption bug, likely weaponizable as wormable RCE, affecting many Android phones, including Pixels. We reported this in February, along with 10 other high+ severity bugs, but are waiting for a patch to ship before sharing more details.



Took like a day and much of the exploit strategy had to be spelled out (even if it's just swapping a different trigger into minipli's existing exploit), but I "hear" Claude was able to produce two working privesc exploits for it.