Sabitlenmiş Tweet
Ethiack
637 posts



Think a relative redirect parameter is inherently safe just because it restricts full external URLs?👀
Think again.
In our latest article, Ethiack Security Researcher, Rafael Castilho, reveals how subtle discrepancies between server-side handling and browser navigation behavior can be weaponized.
By abusing how Google Chrome processes URL fragments (#) during validation loops, an attacker can intentionally trigger an ERR_TOO_MANY_REDIRECTS crash, leaving sensitive session tokens and OAuth callback secrets completely exposed inside the browser error page.
Stop trusting "path-only" limits blindly. Learn how the breakdown happens and how to defend your application pipelines.
👉 Read the full article here: ethiack.com/news/research/…
English


Data breaches are becoming less costly and AI is leading the charge.
According to IBM's 2025 Cost of a Data Breach Report, the average cost of a data breach dropped by 9% to $4.44 million from $4.88 million, marking a significant shift in how organizations defend themselves. This decline isn't coincidental. It's the direct result of AI-powered security tools enabling faster vulnerability detection and organizations rapidly adapting to this new reality.
So the real question is: What's stopping you from joining them?
Stop waiting for the next breach to force your hand. Ethiack gives you continuous visibility, autonomous testing, and only validated findings, all powered by AI agents that never sleep.
Check us out 👇
ethiack.com

English

In our recent analysis, The State of Digital Exposure to Cybercrime of European Telecoms, we identified the three main challenges the industry is facing today:
1️⃣ Visibility gaps create undefendable attack surfaces. If security teams don't know what assets exist, they cannot protect them. This mirrors industry research showing 37% of enterprise attack surfaces are unknown, a foundational weakness that makes all other security investments less effective.
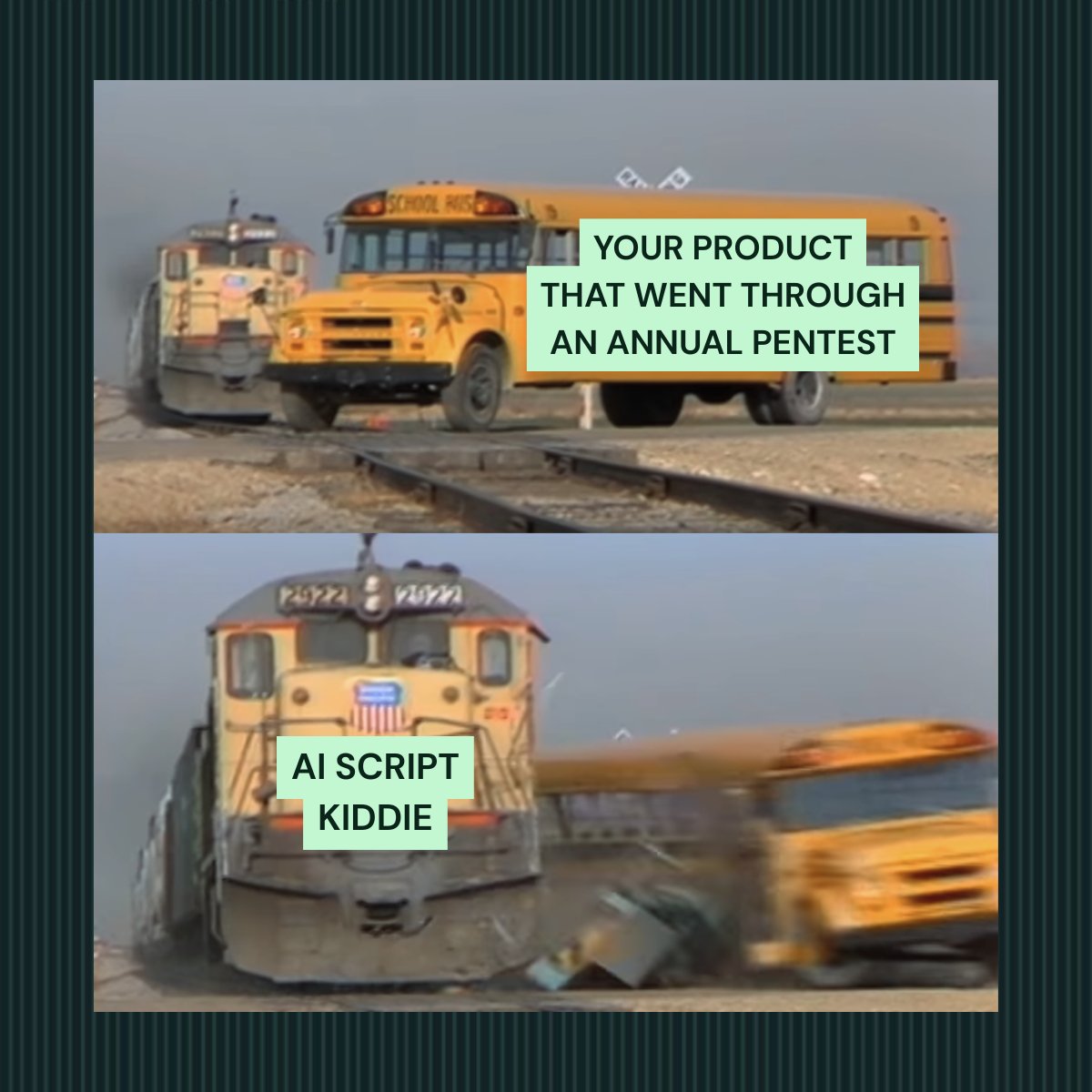
2️⃣ Traditional security approaches cannot match threat velocity. With Time-to-Exploit now approaching -1 days (meaning zero-days are exploited before patches exist) and CVE disclosures up 16% in 2025, annual or quarterly penetration tests are fundamentally inadequate. The attack surface changes faster than periodic assessments can capture.
3️⃣ Critical business assets face disproportionate risk. The assets most vital to operations, such as customer portals, network management systems, and administrative access, show security weaknesses that could result in business disruption, regulatory penalties, and reputational damage.
Read the full report to learn the solutions to these problems👉ethiack.com/news/blog/digi…

English

Ethiack is heading to #RootedCON Portugal 2026 in Lisbon next week!
Our team will be taking the stage to share new research and insights into the future of offensive security:
🟢 May 21: Our CTO, André Baptista (@0xacb), will be delivering a keynote on latest of hacking.
🟢 May 22: Martim Ribeiro (Security Researcher) will present: "From Chat to Agent: How Claude Code is Changing Offensive Security."
We are looking forward to connecting with the community.
👉 If you are attending, let us know so we can connect

English

In our latest report, The State of Digital Exposure to Cybercrime of European Telecoms, we uncovered a growing threat: The connections you maintain with third parties and partners are actively increasing the risk of cyberattacks.
We saw this recently with TalkTalk, where 2 million records were leaked after a criminal exploited a third-party tool.
Terje Jensen, SVP and Head of Global Business Security at Telenor, sums up this complex reality perfectly:
"We see insider threats, but both insider threats within ourselves as a Telecom, but also insider threats from Telecom partners."
Read the full report to learn more👉 ethiack.com/news/blog/digi…

English

Your brand took 10 years to build but a breach could destroy it in minutes.
The consequences go far beyond immediate financial loss. They can include lost customers, shattered trust, lost talent, and a drop in stock value. Reputation damage can compound rapidly, making recovery feel impossible.
Prevention isn't optional. Your brand's survival depends on it.
Our platform gives you continuous visibility into your vulnerabilities, so you can fix security gaps before attackers exploit them. Don't let a preventable breach undo a decade’s worth of dedication and effort. Safeguard your legacy today.
ethiack.com
English

How exposed is the European Telecom sector to modern cybercrime?
Our team analyzed 591 domains across the industry, uncovering a staggering 50,283 exposed digital assets.
If you are a CISO, CTO, or CFO in the telecom space, our report provides the data you need to understand your true exposure to cybercrime, and how your security posture stacks up against the rest of the market.
👉 Read the full report here:👉 ethiack.com/news/blog/digi…

English

Research shows 72% of cybersecurity professionals say false alarms severely hinder productivity.
Hackian, our AI agent, eliminates that burden, continuously hunting and validating vulnerabilities and reporting only true positives.
Experience a smarter, continuous, and more efficient way to enhance your security.
English

The economics of hacking have shifted. Mythos found a 27-year-old vulnerability in OpenBSD's SACK implementation for under $50 per discovery run. Attackers can now achieve scale, depth, and speed that traditional security teams cannot match.
Traditional, human-only defenses are no longer an option against agentic AI. To defend against Mythos-level threats, security posture must include autonomous, continuous pentesting that identifies and validates exploit paths across the entire attack surface in real time.
👉 Read our analysis of Mythos and what it means for the future of cybersecurity: ethiack.com/news/blog/what…

English

90% of organizations have at least one attack path to critical assets. 31% have suffered a supply-chain incident.
Most teams can map their external footprint. The harder problem is verification at scale. Manual pentests are like snapshots, and legacy scanners generate a lot of noise, flagging vulnerabilities that don't chain and misconfigurations that aren't actually exploitable.
Hackian continuously maps your external footprint, verifies exploitability at scale, and delivers prioritized findings with proof-of-exploit and remediation, so you fix only the vulnerabilities that pose actual risk.

English

Your dev team ships 10K lines of code a week. Your security team? Still waiting on last quarter's pentesting report.
That's a massive security gap.
AI pentesters don't get tired. They don't need approval cycles. They validate every deploy in real time, catching the vulnerability before it hits production.
And that's the only way you can actually stay secure at scale in 2026.
ethiack.com

English

Copy-Fail (CVE-2026-31431) is a new Linux kernel zero-day that allows any authenticated user to gain root privileges (Local Privilege Escalation, or LPE) on almost every Linux distribution since 2017.
This release highlights a critical shift in offensive security. While this vulnerability existed unnoticed in legacy code for years, an autonomous AI system identified and validated the flaw in less than one hour.
This discovery underscores three major challenges for traditional defense:
🟢 Legacy Risk: Vulnerabilities can sit dormant for decades in core libraries until an automated system systematically tests every edge case.
🟢 Speed of Discovery: The one-hour discovery-to-validation window proves that manual review and periodic testing are no longer sufficient.
🟢 Economic Scale: When AI can find "undiscoverable" bugs in minutes for a fraction of the cost of a human researcher, the defensive math changes permanently.
What's your take?
English

Alert fatigue is real. Scanner noise is even worse.
You know that feeling when your security tools are screaming at you 24/7 and 90% of it is noise?
We built our AI agent to solve exactly that.
Our AI agent, Hackian, cuts through the noise and tells you exactly what's vulnerable. It doesn't just find vulnerabilities; it understands the context, prioritizes what actually threatens you, and explains the "why" behind each finding.
It only reports when it actually finds something exploitable. Zero false positives with complete insights.
That's pentesting for teams that are actually busy.
Check us out at ethiack.com
#CyberSecurity #AppSec #AlertFatigue #Pentesting

English

The release of Mythos has accelerated a shift in how we handle security. With AI-driven tools like this, quarterly or annual penetration tests are now obsolete.
67% of what is exploited today happens before the defender community even knows a vulnerability exists.
The industry is moving toward a new standard: VulnOps.
VulnOps is a permanent, staffed, and automated function for continuous vulnerability research and remediation. It focuses on the discovery of zero-days across your entire software footprint, including your own code and third-party dependencies, to establish automated remediation pipelines.
Read our article on the Mythos release and what it means for the future of cybersecurity 👇 ethiack.com/news/blog/what…
English

To keep a global communications platform secure, visibility is the first priority. You cannot protect what you cannot see.
We talked with Pedro Cunha, ISO/DPO at Broadvoice, about the challenges of securing a massive, evolving perimeter. Their team faced three compounding problems:
🟢Visibility: AWS resources and shadow IT often fell outside their known ranges, making it impossible to maintain a current map of what was exposed.
🟢Validation: They had no continuous way to prove which vulnerabilities were actually exploitable versus which were just noise.
🟢Velocity: Their environment changed daily, meaning periodic pentests only provided snapshots that quickly became outdated.
By adopting Ethiack’s autonomous engine, they transitioned to continuous validation—staying ahead of vulnerabilities and securing their attack surface in real time.
👉 See the full story: ethiack.com/news/case-stud…
English

Regulators increasingly expect more than a once-a-year snapshot of your security.
Traditional annual pentests create a dangerous illusion of security. They provide a compliance checkbox, not actual protection. By your next audit, new vulnerabilities and attack vectors have already emerged and have probably been exploited.
This gap is exactly what attackers exploit. Your competitors are already aware of this shift, and regulators are too. Continuous security testing is becoming the new baseline.
Ethiack powers continuous AI-driven security validation, enabling you to maintain both genuine security and regulatory compliance.
➡️ ethiack.com
English