Ezrak1e
74 posts

Ezrak1e
@ezrak1e
Security researcher of Ant Security Light-Year Lab

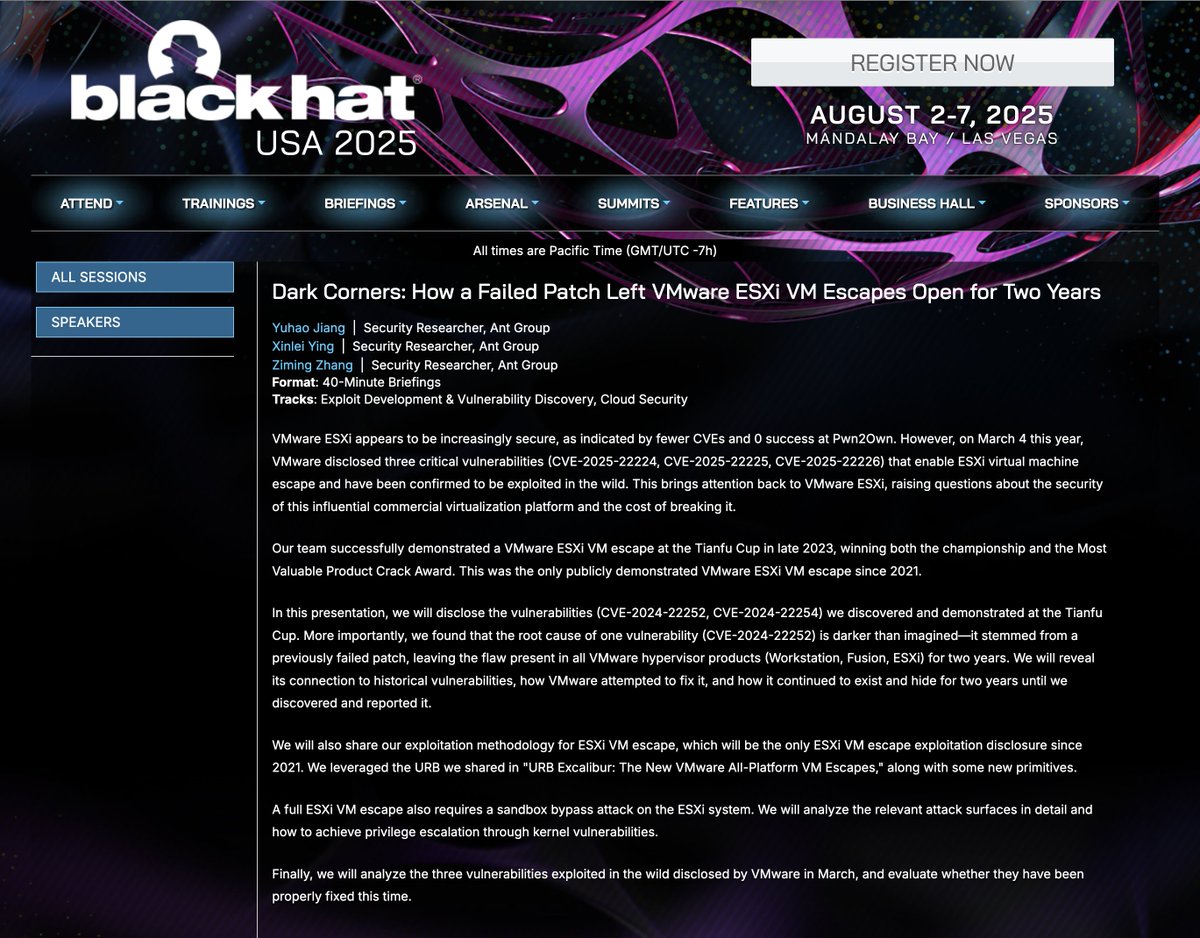

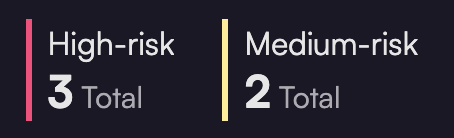
The Microsoft Researcher Recognition Program offers public thanks and recognition to security researchers who help protect our customers by discovering and sharing security vulnerabilities under Coordinated Vulnerability Disclosure. Today, we are excited to recognize this year’s 100 Most Valuable Researchers (MVRs), based on the total number of points earned for each valid report. Please join us in celebrating this year’s MVRs, including our top 10: 1. 🥇 Yuki Chen @guhe120 2. 🥈Wei @XiaoWei___ 3. 🥉VictorV @vv474172261 4. Suresh Chelladurai 5. Dhiral Patel @dhiralpatel94 6. Erik Donker @kire_devs_hacks 7. Nutesh Surana @_niteshsurana working with Trend Micro Zero Day Initiative @thezdi 8. Anonymous 9. Tzah Pahima @TzahPahima 10. wkai See the full list of this year’s 100 MVRs, in addition to our Azure, Office, Windows, and Dynamics 365 leaderboards: msrc.microsoft.com/blog/2024/08/c… #bugbounty #infosec

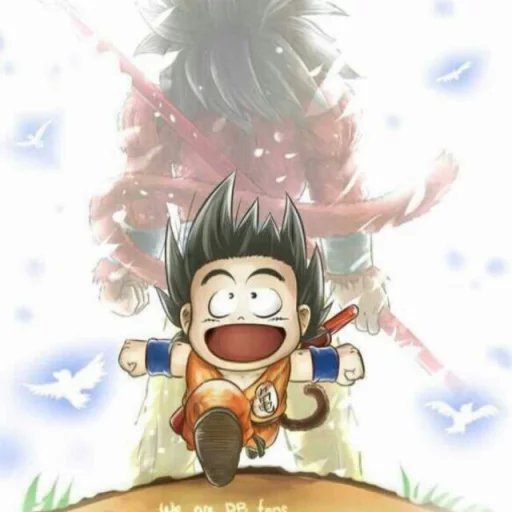
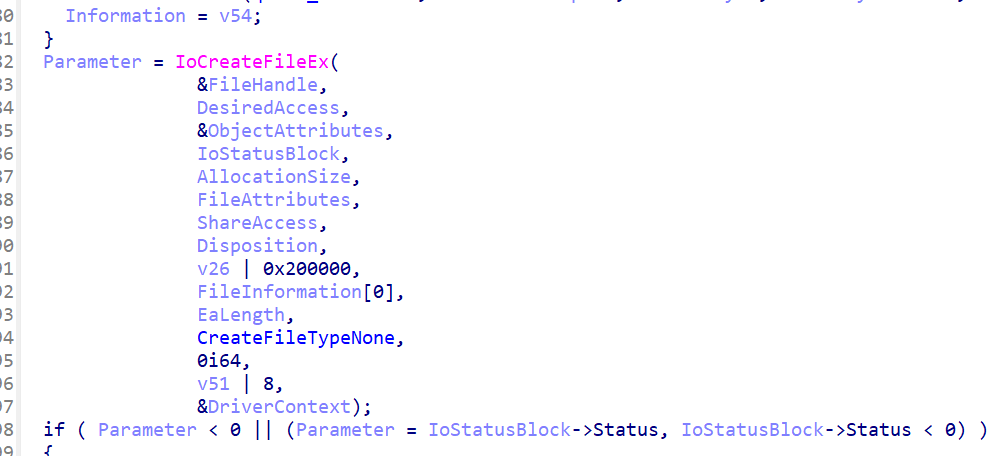
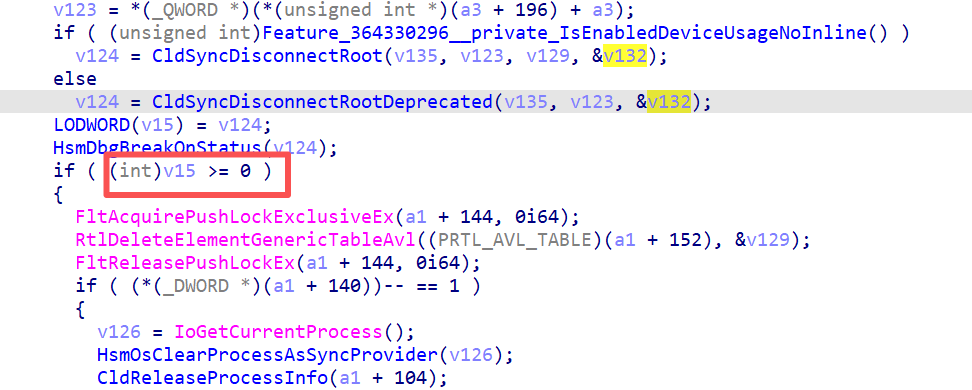
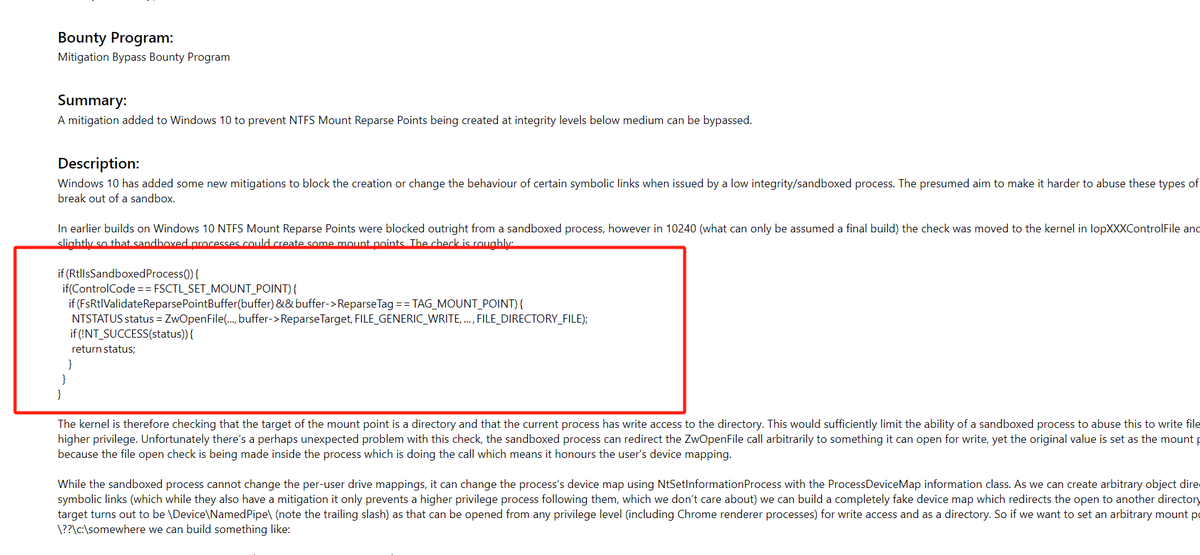
A funny story about a vulnerability I found last year. It was fixed in February this year, probably CVE-2024-21371. The interesting point is that I discovered it and completed the exploit based on a piece of source code disclosed in the high-quality documentation report of msrc🤣







Congratulations to our MSRC 2023 Most Valuable Researchers! Thank you to all the researchers who have helped secure our customers. 👏🎉 Check out our blog for the full list: msft.it/60199yOc9