Sabitlenmiş Tweet

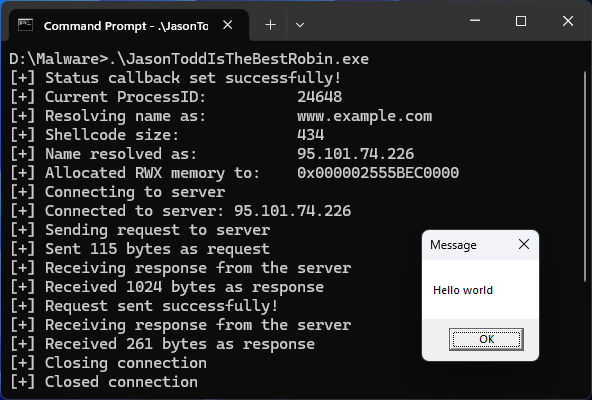
Fun fact: StoneKeeper C2 contains a text file with URLs to Nighthawk samples here github.com/fin3ss3g0d/Sto… 1/4 has been verified and contains the original logic for the Ekko sleep obfuscation technique
English
fin3ss3g0d
220 posts
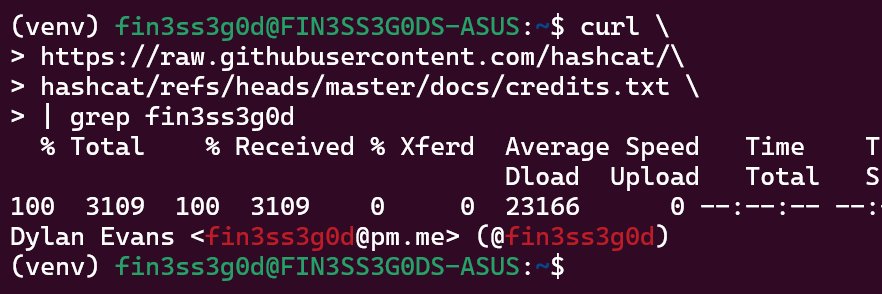

@fin3ss3g0d
Red Team Operator/Pen Tester | Offensive Security Software Developer | Tweets are unaffiliated with my employer | OSCP | OSEP | CRTO | CRTL












Hosts running the WebClient service are prime targets for NTLM relay attacks, and it may be possible to start the service remotely as a low-privileged user. @0xthirteen breaks down the service startup mechanics, plus the protocols and technologies. ghst.ly/41QT7GW