Sabitlenmiş Tweet
0g.hl
1.3K posts

0g.hl
@gin_0x
Og in web3, not yet og in Hyperliquid. Growth & tokenomics Ex CEO @ https://t.co/w7D9askL5v , part of @animocabrands Ex CMO @ Top VPN
Katılım Kasım 2021
2.9K Takip Edilen4.3K Takipçiler
0g.hl retweetledi

Great to see more and more L1 chains talking about their post-quantum roadmap
Arc, an L1 for stablecoin finance, by @circle states: „Quantum resilience cannot live only in research papers, exploratory pilots, or distant roadmap slides. It has to show up in the infrastructure.“
I couldn’t agree more and excited to build an L1 migration toolkit by @qlabsofficial helping chains to migrate to a post-quantum environment.
English
0g.hl retweetledi

Q-Day won't announce itself.
By the time it's obvious, it's already late.
qVAULT protects what you already hold.
Pre-registration is open.
qonetoken.io
English

@gin_0x the stack diversity here is wild. a year ago this would have been a 5-person team with separate video, voice, and design roles. what did the total build time end up being?
English
0g.hl retweetledi

See you shortly.
In case you missed today's quantum news, good timing for this one.
qONE@qlabsofficial
We're hosting Spaces 🎙️ "Building on Hyperliquid: security, data & what's next" Tomorrow, Tuesday at 14:00 UTC w/ @HYLQstrategy, @sedaprotocol, @01quantuminc and @HYPEconomist Set your reminder 👇 x.com/i/spaces/1qKVm…
English
0g.hl retweetledi

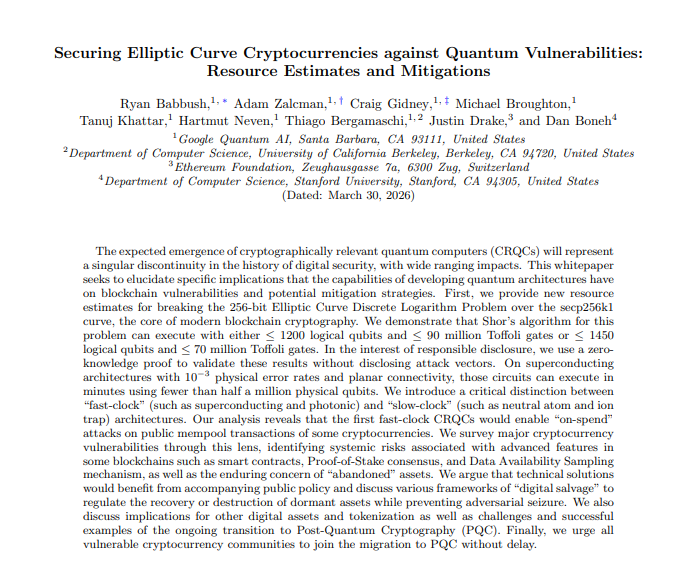
Google just told the entire crypto industry it has ~3 years to migrate to post-quantum cryptography or face existential risk.
Not a blog post. A 57-page research paper with @ethereumfndn and @Stanford.
500K physical qubits. 9 minutes to derive a private key.
Every ECDSA signature in crypto is on a clock now.
We didn't wait for this paper. We're already building the quantum-resistant infrastructure on Hyperliquid.
Link in comments
English
0g.hl retweetledi

🚨$800,000,000,000 WORTH OF BTC AND ETH ASSETS ARE AT RISK
Today, Google Research published a paper on quantum computers, and it's really bad.
First of all, Google now thinks it would only take 500,000 qubits to crack crypto.
Earlier everyone thought it would be 1M, which means 20x less.
But this is just the tip of the iceberg.
Before today, everyone thought that quantum attacks would take months.
This means transactions are safe, and 1/3 of BTC are at risk.
But this has now changed.
Google claims that a quantum computer could crack private keys in just 9 MINUTES.
This is a minute less than Bitcoin's average block time.
And this isn't just limited to BTC.
The research says that quantum computers could break into the top 1000 ETH wallets within 9 days.
And now here's the most scary part?
Google thinks crypto projects don't have decades to prepare for this.
By 2030, Quantum computers could be powerful enough to crack Bitcoin and alts.
This means we have just 4 years before Quantum computers become a reality and not just FUD.


English
0g.hl retweetledi

We're hosting Spaces 🎙️
"Building on Hyperliquid: security, data & what's next"
Tomorrow, Tuesday at 14:00 UTC
w/ @HYLQstrategy, @sedaprotocol, @01quantuminc and @HYPEconomist
Set your reminder 👇
x.com/i/spaces/1qKVm…
English
0g.hl retweetledi

Quantum timelines are accelerating and so is $qONE activity.
Earn up to 140% APR on $qONE / $HYPE. Incentives are active.
Rewards include:
• Trading fees
• USDT incentives
• xSWAP incentives
Add liquidity:
app.hyperswap.exchange/#/pool/172526

English
0g.hl retweetledi

BREAKING 🚨
Google updates their quantum migration deadline to 2029:
“Google’s introducing a 2029 timeline to secure the quantum era with post-quantum cryptography (PQC) migration.
Last month, we called to secure the quantum era before a future quantum computer can break current encryption. This new timeline reflects migration needs for the PQC era in light of progress on quantum computing hardware development, quantum error correction, and quantum factoring resource estimates.”
English
0g.hl retweetledi
0g.hl retweetledi

Why hasn’t crypto upgraded to post-quantum security yet?
Because cryptography in blockchains isn’t isolated.
It’s part of the execution model:
- transaction validation rules
- signature verification (ECDSA / EdDSA)
- address derivation
- wallet key management
- smart contract authorization
All of that assumes one thing:
private keys can’t be derived from public keys.
Post-quantum schemes break the shape of that system:
- larger keys and signatures
- different verification logic
- no drop-in compatibility
That hits constraints everywhere:
- gas costs
- block limits
- node performance
- hardware wallet support
You’re changing how ownership and validation work across the entire stack. The open-source and “community ownership - no sole owner” nature makes it a very hard and long process to adapt to any modification that requires consensus in the entire ecosystem.
That’s why this hasn’t happened yet.
English
0g.hl retweetledi
0g.hl retweetledi

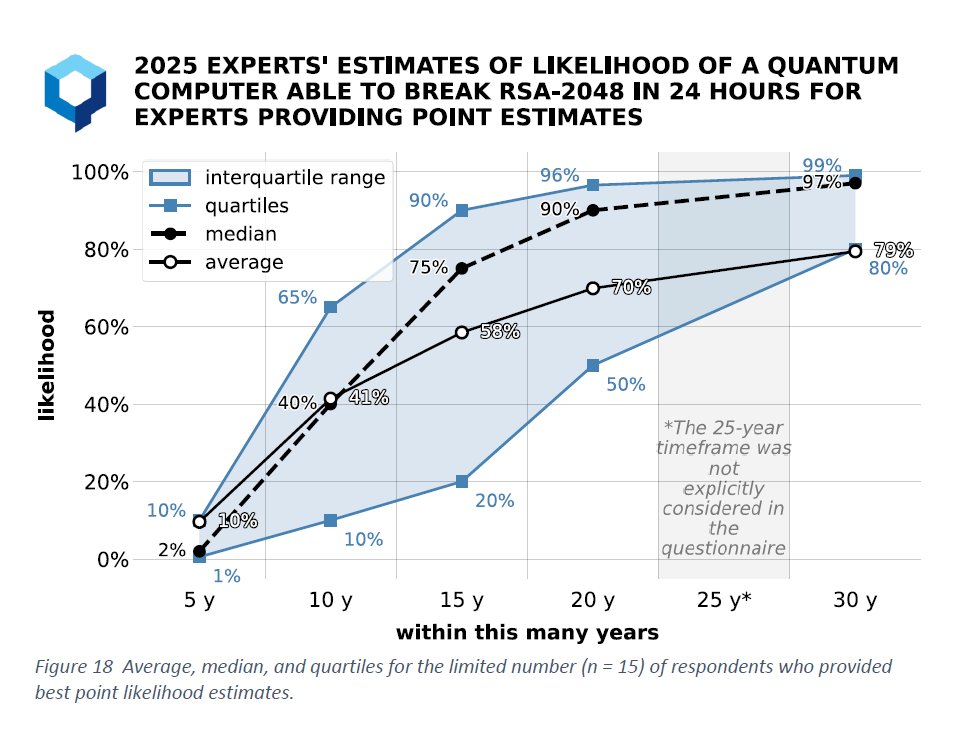
Most people focus on “24-hour breaks.”
That’s the wrong model.
If a quantum attacker can derive a private key in months, not minutes, high-value targets are still exposed.
This chart assumes 24 hours. Reality is more forgiving for attackers.
~50%+ probability within 10 to 15 years is already enough.
English
0g.hl retweetledi

Quantum progress is increasingly defined by error correction, not qubit count.
Recent research focus:
- reducing overhead per logical qubit
- improving stability
- extending coherence times
This matters because:
Without fault tolerance → no cryptographic break.
Scaling is still the bottleneck.
English
0g.hl retweetledi
0g.hl retweetledi

The real quantum threat isn’t blockchain.
It’s the keys behind it.
Our advisor Aaron explains how quantum computers could copy digital signatures used across crypto and the internet.
🎥 Clip below ↓
qONE@qlabsofficial
Ada Jonuse × Aaron Moore (qLABS Advisor) If you missed last night’s stream, the replay is now available. We covered quantum risk, what “post-quantum” really means in practice, and how qLABS is approaching quantum-safe security for Web3. Watch here 👇
English
0g.hl retweetledi

Post-quantum migration is often framed as an algorithm problem.
It isn’t.
NIST already standardized post-quantum signatures.
The difficult part is how those signatures integrate with real systems.
Wallet software, smart contracts, bridges, exchanges → all assume specific signature verification models.
Changing that layer affects the entire stack.
That’s why deployment architecture matters.
At qLABS we focus on introducing quantum-safe authorization through the Quantum-Sig wallet, allowing users to secure assets with post-quantum signatures while remaining compatible with today’s networks.
Stronger cryptography is necessary.
But migration only works if the infrastructure can actually adopt it.
English

