
GridPlus
3.4K posts

GridPlus
@gridplus
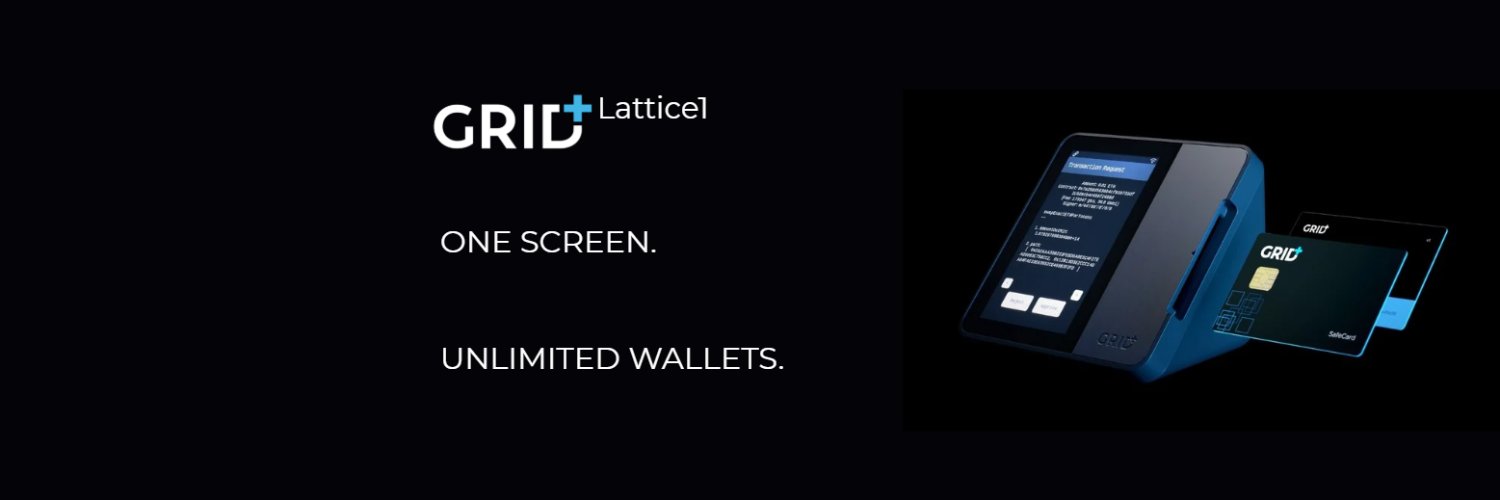
The world's first secure touchscreen hardware wallet. Complete solutions for secure signing, key storage, and backups. Engineered and manufactured in the USA.


🚨 CRITICAL: Active supply chain attack on axios -- one of npm's most depended-on packages. The latest axios@1.14.1 now pulls in plain-crypto-js@4.2.1, a package that did not exist before today. This is a live compromise. This is textbook supply chain installer malware. axios has 100M+ weekly downloads. Every npm install pulling the latest version is potentially compromised right now. Socket AI analysis confirms this is malware. plain-crypto-js is an obfuscated dropper/loader that: • Deobfuscates embedded payloads and operational strings at runtime • Dynamically loads fs, os, and execSync to evade static analysis • Executes decoded shell commands • Stages and copies payload files into OS temp and Windows ProgramData directories • Deletes and renames artifacts post-execution to destroy forensic evidence If you use axios, pin your version immediately and audit your lockfiles. Do not upgrade.






✨LUNAR NEW YEAR SALE IS LIVE 🧧 To celebrate new beginnings in the Year of the Fire Horse, we’re dropping a $100 discount on the Lattice1. 🎁 Each Lattice1 pack includes 3 free SafeCards. ⏳ 7 days only. Shop at gridplus.io. No code needed.





🚨 Security update: large-scale address poisoning + social engineering campaign targeting multisig users We’ve identified a coordinated effort by malicious actor(s) to create thousands of lookalike Safe addresses designed to trick users into sending funds to the wrong destination. This is social engineering combined with address poisoning. Important: this was not a protocol exploit, not an infrastructure breach, and not a smart contract vulnerability. That said, we take reports like this extremely seriously, because the end result is the same: users’ funds may be at risk. Etherscan reference (attacker factory used to deploy malicious Safes): etherscan.io/address/0x8b77… With the help of SEAL911, Hypernative, and Blockaid, we investigated the attack pattern and identified ~5,000 malicious addresses. These addresses have been flagged as malicious via SafeShield (powered by our security partners) and are being removed from Safe Wallet’s UI, reducing the risk of accidental interaction. Please note: similar schemes are easy for malicious actors to reproduce. It’s therefore critical to follow secure signing procedures, especially for high-value transfers (e.g., verify the full address, use an address book/allowlist, confirm recipients out-of-band, make a smaller transfer first). Address poisoning and social engineering, like phishing, are evolving and persistent threats in crypto. Defending against them requires continuous investment in both detection and UX improvements that reduce human error. For anyone unfamiliar with this attack pattern, we strongly recommend reading more here: help.safe.global/en/articles/18… Using address book in safe: help.safe.global/en/articles/23… Using address book in spaces: help.safe.global/en/articles/38… Stay vigilant: don’t trust—always verify full addresses, not just prefixes and suffixes. 🛡️ Huge thanks to SEAL911, Hypernative, and Blockaid for their rapid support.




We spent 48+ hours researching security-first OpenClaw setups. By the end of this guide you'll have: - OpenClaw on a Pi via Tailscale - Matrix E2E chat - Prompt injection hardening - No-log LLM provider - Firewall + habits for damage control It's long but totally worth it.

