
Hacken🇺🇦
10.7K posts

@hackenclub
End-to-End Blockchain Security & Compliance Partner Born on blockchain. Built for what’s next 🛡️






A months long, premeditated attack exploiting a known, dismissed vulnerability in a low liquidity token market. Mefai Analysis. We investigated after seeing some articles suggesting that @Binance was to blame. It has nothing to do with Binance,(We know this was intentional.) and #Venus has also warned team about this. Venus Protocol vTHE Attack | Full Analysis Attacker, 0x1a35bd28efd46cfc46c2136f878777d69ae16231 Funding: 7,400 ETH from Tornado Cash The Block How It Worked, Attacker spent 9 months (starting June 2025) quietly accumulating ~84% of THE's supply cap (14.5M tokens). Then, instead of depositing normally, they transferred tokens directly to the vTHE contract a donation attack bypassing the supply cap entirely and building a 53.2M THE position, 3.7× the allowed limit. They then ran a classic loop, 1 deposit THE 2 borrow assets 3 buy more THE 4 wait for TWAP oracle update 5 repeat, pushing THE's price from ~$0.263 to ~$0.563 before it collapsed to ~$0.22 on liquidation. Assets borrowed, 6.67M CAKE, 1.58M USDC, 2,801 BNB, and 20 BTC. Damage , ~$2.15M in bad debt remained 1.18M CAKE and 1.84M THE unrecoverable. The playbook mirrors the October 2022 Mango Markets exploit. Damning Part ,This exact donation attack vector was flagged in Venus's own Code4rena security audit. The team dismissed it, arguing donations were supported behavior with no negative side effects.

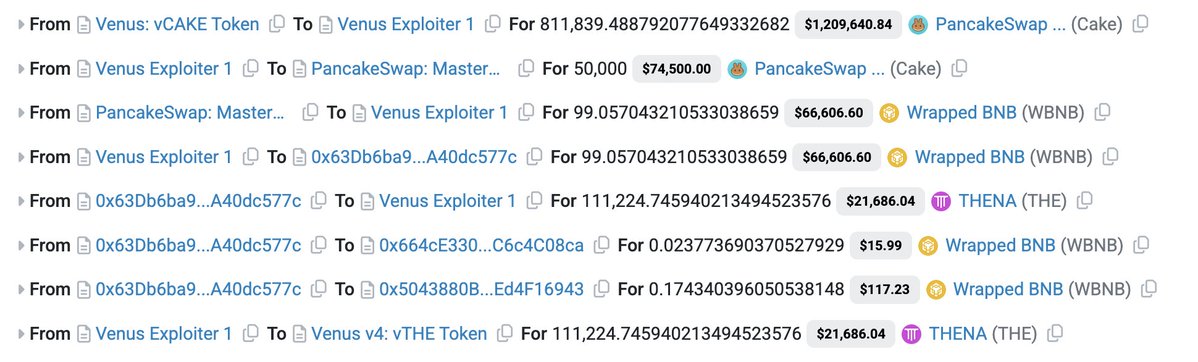


A months long, premeditated attack exploiting a known, dismissed vulnerability in a low liquidity token market. Mefai Analysis. We investigated after seeing some articles suggesting that @Binance was to blame. It has nothing to do with Binance,(We know this was intentional.) and #Venus has also warned team about this. Venus Protocol vTHE Attack | Full Analysis Attacker, 0x1a35bd28efd46cfc46c2136f878777d69ae16231 Funding: 7,400 ETH from Tornado Cash The Block How It Worked, Attacker spent 9 months (starting June 2025) quietly accumulating ~84% of THE's supply cap (14.5M tokens). Then, instead of depositing normally, they transferred tokens directly to the vTHE contract a donation attack bypassing the supply cap entirely and building a 53.2M THE position, 3.7× the allowed limit. They then ran a classic loop, 1 deposit THE 2 borrow assets 3 buy more THE 4 wait for TWAP oracle update 5 repeat, pushing THE's price from ~$0.263 to ~$0.563 before it collapsed to ~$0.22 on liquidation. Assets borrowed, 6.67M CAKE, 1.58M USDC, 2,801 BNB, and 20 BTC. Damage , ~$2.15M in bad debt remained 1.18M CAKE and 1.84M THE unrecoverable. The playbook mirrors the October 2022 Mango Markets exploit. Damning Part ,This exact donation attack vector was flagged in Venus's own Code4rena security audit. The team dismissed it, arguing donations were supported behavior with no negative side effects.
