Sabitlenmiş Tweet

🚀 Join Our Official WhatsApp Channel!
Stay updated with the latest Cybersecurity content, internships, training updates, and exclusive learning resources 💻🔥
👉 Join here: whatsapp.com/channel/0029Vb…
Don’t miss out on important updates from Hacking Articles & Ignite Technologies ⚡
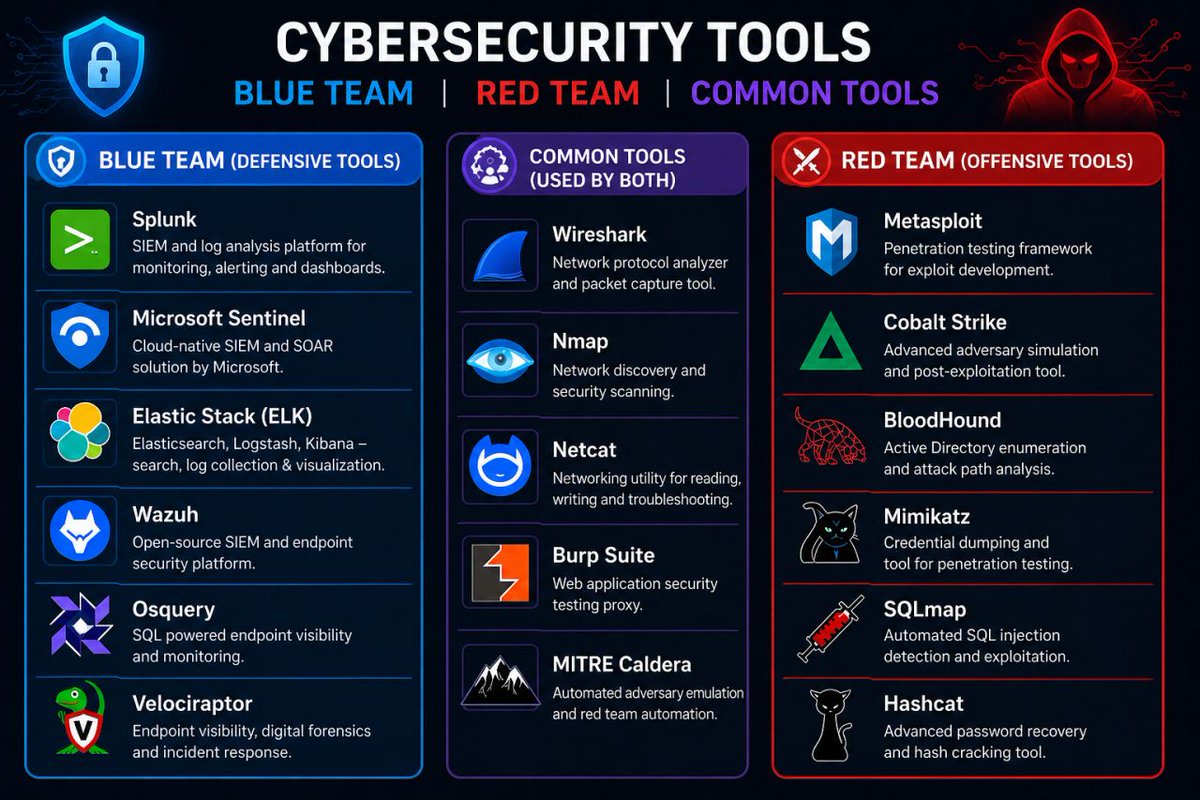
#CyberSecurity #EthicalHacking #HackingArticles #Infosec #RedTeam

English