Sabitlenmiş Tweet
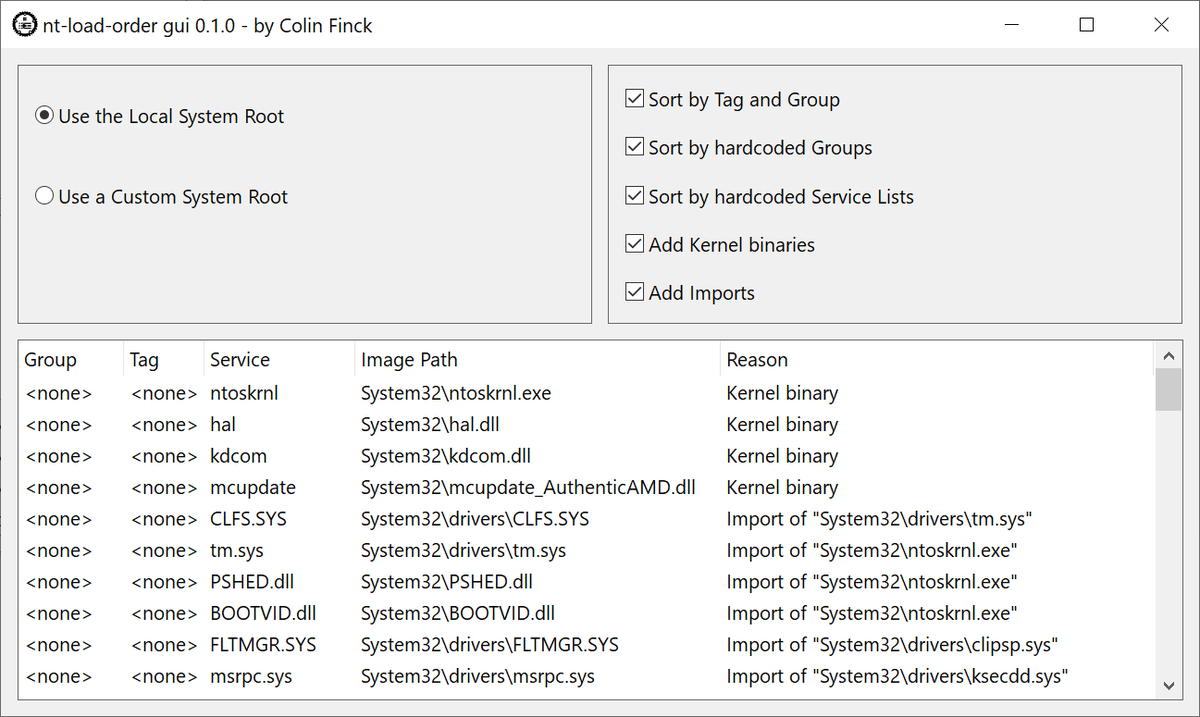
I am sharing my Windows-specific #Python codebase: github.com/hakril/PythonF….
It even has a documentation ! hakril.github.io/PythonForWindo…
English
Clement Rouault
466 posts
@hakril
Python (ab)user / Security / Windows internals / @ExaTrack