Haseeb Awan - efani.com
9.7K posts


@haseeb
CEO @efani - America’s Most Secure Mobile Service - @ycombinator
















Sigh…



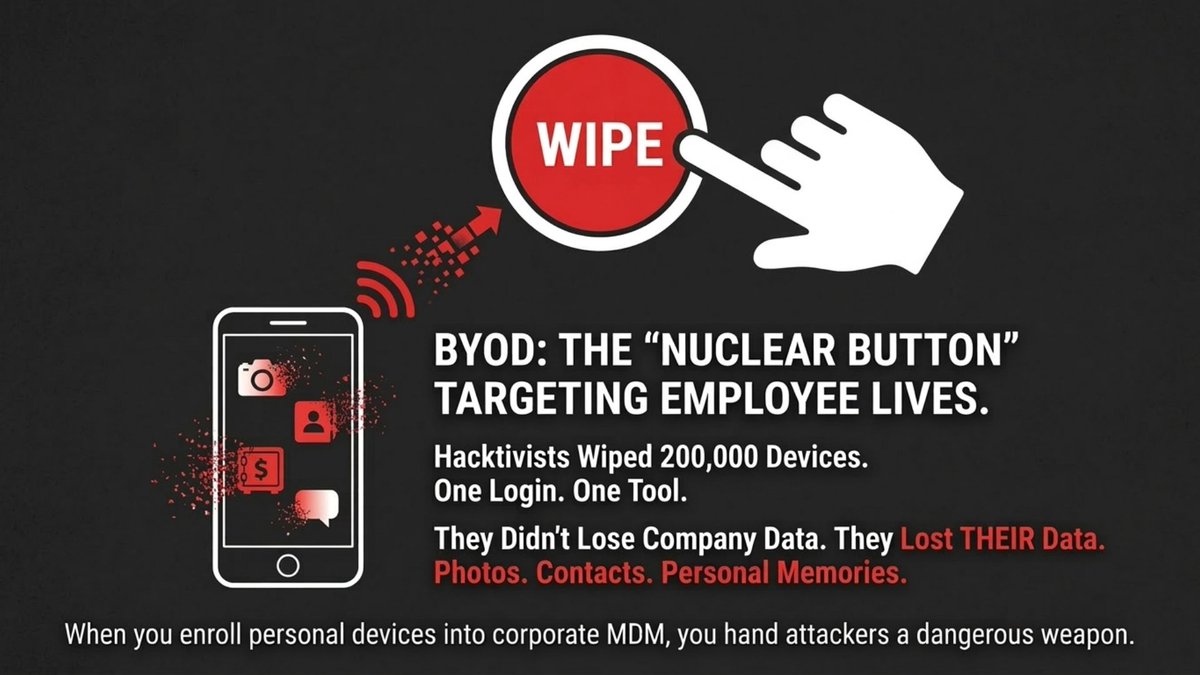
Cybersecurity is not failing because of technology. It is failing because of behavior. Mark recently hosted @RobertSiciliano, founder of @ProtectNowLLC, on our Efani Features podcast. One idea from that conversation stands out: All security is personal. Organizations spend heavily on tools. Firewalls. Monitoring. Compliance training. Phishing simulations. Yet breaches continue. Why? Because most people do not see security as something that protects them. They see it as policy. As inconvenience. As someone else’s responsibility. If someone reuses passwords in their personal life, ignores two-factor authentication, or dismisses identity protection at home, that mindset follows them into the workplace. That is where account takeovers begin. That is where SIM swaps succeed. That is where social engineering works. The real shift is not from insecure to secure systems. It is from awareness to appreciation. When people care about protecting their own identity, they protect company data differently. That is the conversation we need to be having in 2026. The full episode is live on @efani’s YouTube channel: youtu.be/NdMLY0-uNJY