Sabitlenmiş Tweet
HaxRob
858 posts

HaxRob
@haxrob
I enjoy breaking things. Telco / mobile and IoT security. Surfing the information super highway one keystroke at a time.
Australia Katılım Nisan 2017
458 Takip Edilen15.1K Takipçiler

@0xmadvise Cool - nice
to see more content published around this technique.
haxrob.net/hiding-in-plai…
English

Hello, i wrote a blog on one of the modern persistence techniques in Linux using the unshare syscall. Enjoy reading
@0xmadvise/rJPLNLRwlx" target="_blank" rel="nofollow noopener">hackmd.io/@0xmadvise/rJP…
English

@TheHackersNews The group-ib report seems to have omitted one of most important details: hashes of the sample(s) ....
English

🔥 A hacker gang planted a 4G Raspberry Pi inside a bank’s ATM network—bypassing firewalls to install a rootkit called CAKETAP.
It spoofed PIN checks, hid processes, and aimed to trigger fraudulent withdrawals.
Details you should know ↓ thehackernews.com/2025/07/unc289…
English
@haxrob Cool!
Related (a paper we wrote recently):
arxiv.org/abs/2506.07827
English
HaxRob retweetledi

Really interesting ways here to hide files and other activity on Linux.
HaxRob@haxrob
A relatively unknown but particularly stealthy technique to hide files on Linux hosts. On unhardened boxes, unprivileged users can conceal files from even the root user. Disk content remains in memory, hindering disk acquisition during forensic investigation. (1/7) 👇
English

@e__soriano Nice one - creative use within user space rootkits. I have just referenced your paper in the appendix of the post under 'related research'.
English

Full writeup including mitigations, threat hunting and other detection ideas.👇
(7/7)
haxrob.net/hiding-in-plai…
English
HaxRob retweetledi

Security researcher @haxrob released a two-part technical breakdown of BPFDoor, a Linux-targeting malware tied to past APT campaigns. The analysis includes insights on recent variants observed this year.
haxrob.net/bpfdoor-past-a…
haxrob.net/bpfdoor-past-a…



English
HaxRob retweetledi

Great blog posts and updates on latest BPFDoor changes by @haxrob
BPFDoor - Part 1 - The past:
haxrob.net/bpfdoor-past-a…
BPFDoor Part 2 - The Present:
haxrob.net/bpfdoor-past-a…
English

A writeup of this content can be found in a two part series:
(22/x)
haxrob.net/bpfdoor-past-a…
English

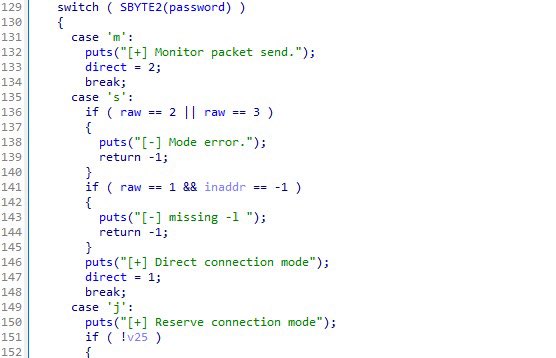
Newer samples can be found to have the authentication password as a salted MD5 hash.
github.com/haxrob/bpfdoor… can extract the hashes from samples and generate the respective hashcat command.
Here are a few cracked ones. Those that identify victims are not included.
(21/x)

English




