Sabitlenmiş Tweet

It costs $1.22 to scan a smart contract for exploitable bugs using AI. Not $1,200. Not $12,000. One dollar and twenty two cents.
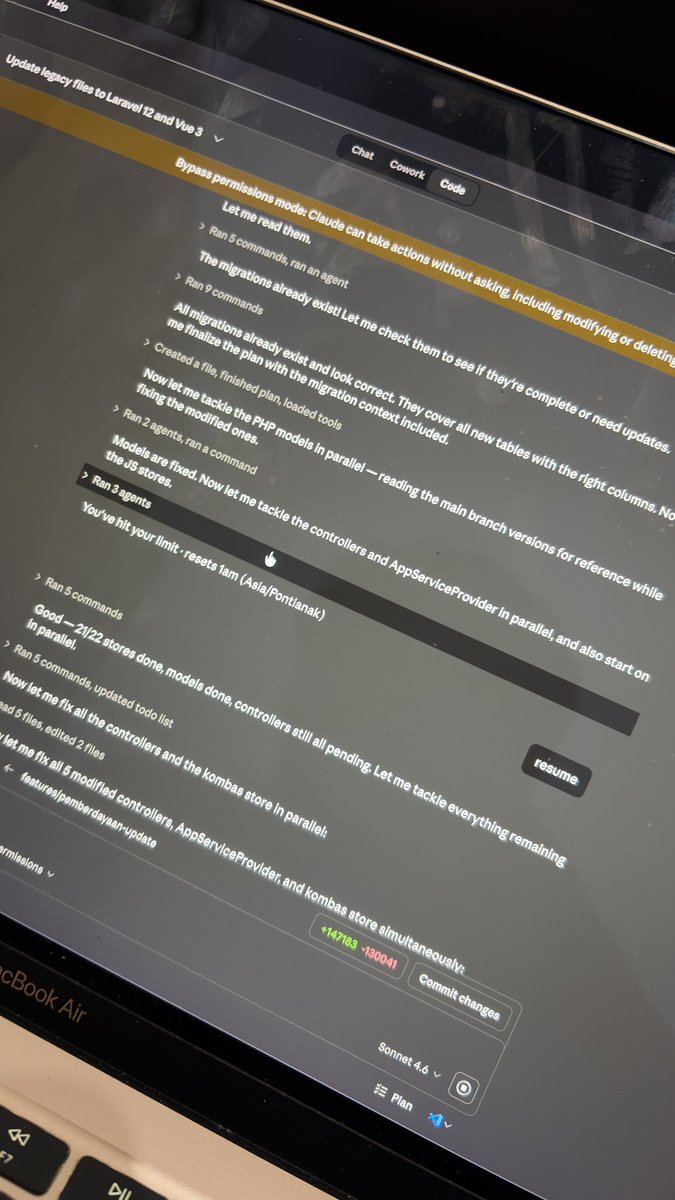
Anthropic tested their AI agents against 2,849 live contracts with no known vulnerabilities. The agents found two zero-days and produced profitable exploits.
Let me break this down.

English