Er Pratik Panchal🐬 retweetledi

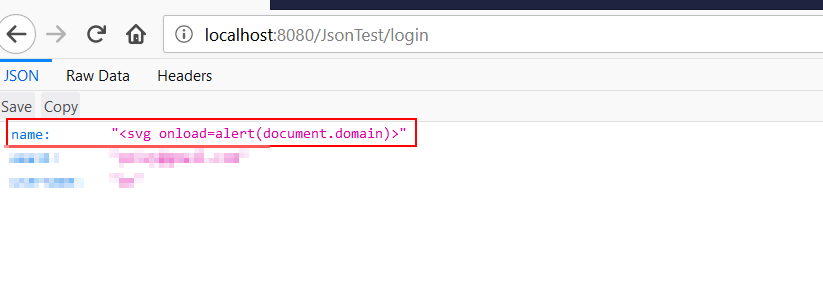
Popping alert(1) doesn't show REAL impact.
Escalate your XSS by stealing cookies instead👇
Better XSS escalation paths here: bugcrowd.com/blog/the-ultim…
English
Er Pratik Panchal🐬
2.1K posts


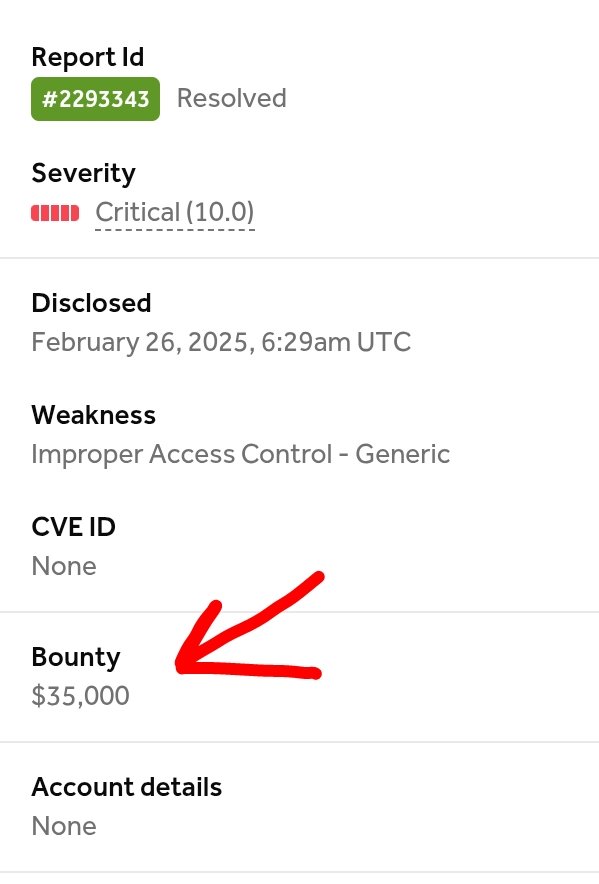
@iDiablo5
💻 = 'print("Playing on :", (@Hacker0x01 + @SynackRedTeam))' exec(💻)